Security leaders invest heavily in the right technology. But when that technology fails to deliver – when alerts stay noisy, detections stay shallow and the SOC still struggles – the gap is not always the platform. In many cases, it’s the implementation. That is exactly why knowing the right questions to ask a CrowdStrike NG-SIEM implementation partner has become one of the most important decisions you can make.
CrowdStrike’s Falcon Next-Gen SIEM is among the most powerful security platforms available today. Organisations that have deployed it well, report good number of improvements in detection speed, analyst efficiency and overall SOC maturity. But the same platform, deployed without the right expertise, can produce the same alert fatigue, the same blind spots and the same noise that drove firms away from legacy SIEM in the first place.
This blog is a practical guide for anyone who is looking for a trustworthy CrowdStrike NG-SIEM implementation partner and want to make a confident, well-informed decision.
Why NG-SIEM migrations fail without the right partner
CrowdStrike’s Chief Business Officer has been direct about this: “SIEM isn’t a plug-and-play sensor like EDR. SIEM migration requires movement & ingestion of data and requires dashboarding and workflow automation. It’s a true SOC transformation.”
The global SIEM market is projected to grow from $8.33 billion to $28.85 billion by 2032. Every major organisation is rethinking its detection and response infrastructure. But the rush to modernise has also produced a familiar pattern: rushed deployments, incomplete data onboarding, untested detection logic and SOC teams left without proper training. When implementation falls short, security leaders end up with a sophisticated platform they cannot fully operationalise.
Selecting a certified, experienced CrowdStrike NG-SIEM implementation partner is a strategic decision that directly affects your organisation’s threat detection capability.
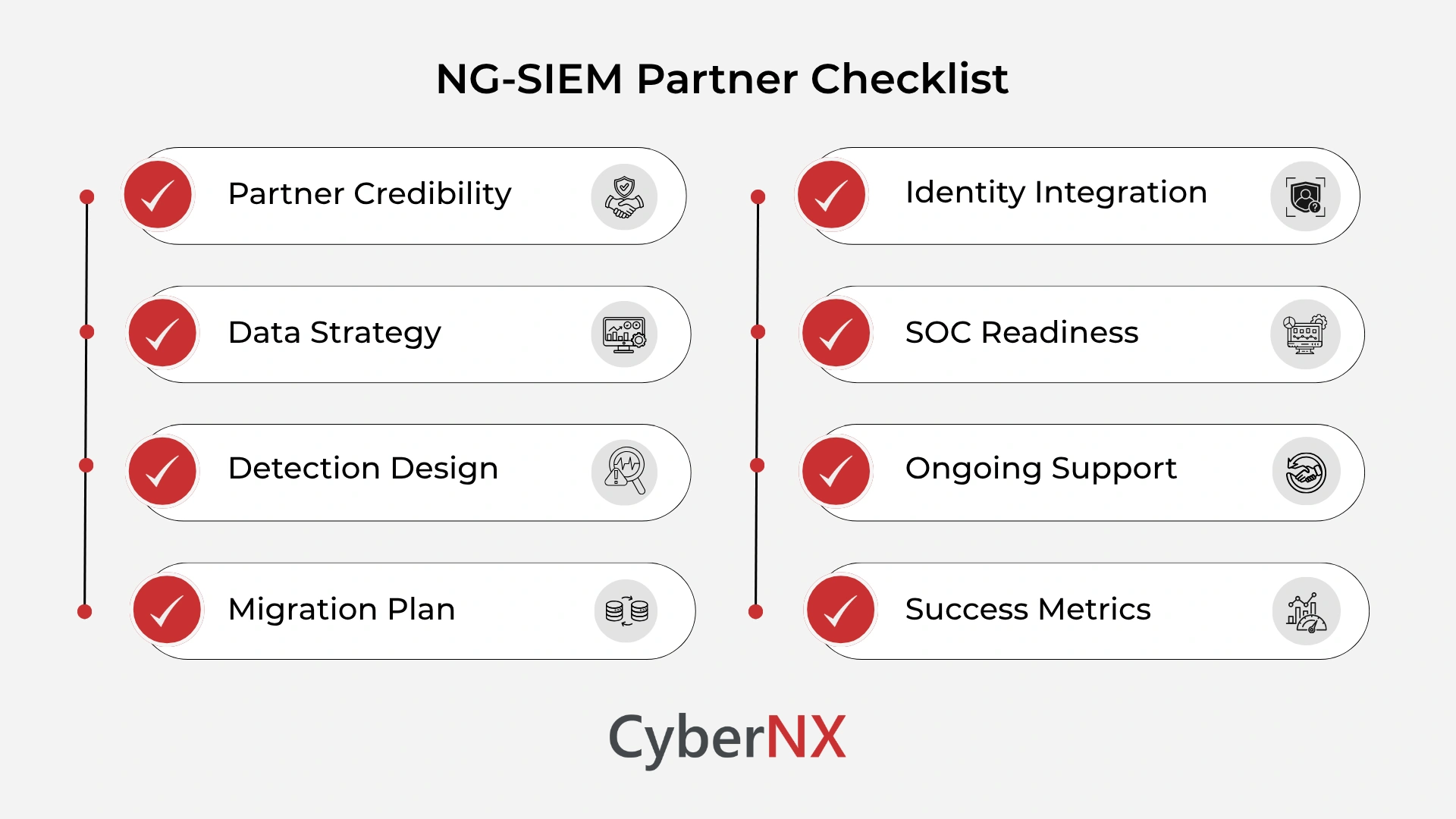
8 questions to ask a CrowdStrike NG-SIEM implementation partner
Before you finalise an engagement, these are the questions every security leader should ask. They are designed to separate credible partners from those who are simply reselling licences.
Are you a certified CrowdStrike services partner with documented NG-SIEM deployments?
This is where your evaluation should begin – and both parts of the question carry equal weight. Certification confirms that the partner has met CrowdStrike’s training standards, operates within their Services Partner Programme and has access to the resources and frameworks that generic resellers simply do not have.
Deployment history, on the other hand, tells you whether that training has translated into real-world outcomes.
Ask the partner to share specific examples of Falcon Next-Gen SIEM implementations they have led, like the industries involved, the size and complexity of the environments and the measurable results delivered.
A partner with strong certification but limited deployment experience carries risk, as does a partner with field experience but no formal standing. What you are looking for is both. Verify their certification status directly with CrowdStrike if needed, and treat any reluctance to share deployment references as a warning sign.
How will you approach data onboarding and log source integration for our environment?
Data strategy is the foundation of every NG-SIEM deployment. Ask the partner how they plan to inventory your existing log sources, prioritise ingestion order and handle parsers for custom or niche data sources. Falcon Next-Gen SIEM supports a growing set of out-of-the-box data connectors, but complex hybrid environments. Particularly those mixing on-premises infrastructure, multi-cloud workloads and legacy applications need a deliberate data architecture plan.
A strong partner will ask about your data volumes, retention requirements and compliance obligations before proposing a solution.
How do you handle detection engineering and MITRE ATT&CK alignment?
One of the most common failures in SIEM deployments is treating detection as an afterthought. Ask the partner how they approach detection logic. Specifically, whether they build custom detection rules aligned to your threat model or depend entirely on out-of-the-box content.
Ask whether they map detections to MITRE ATT&CK and how they validate coverage gaps. Detection design should feel operational and tied to real adversary behaviour, not theoretical. Partners who cannot articulate their detection engineering methodology are likely to hand you a populated dashboard that generates noise rather than signal.
What is your migration plan for decommissioning our legacy SIEM?
Most organisations moving to CrowdStrike NG-SIEM are coming from legacy platforms like Splunk, IBM QRadar or Microsoft Sentinel. The migration plan should include parallel running – a period where both the legacy system and NG-SIEM operate simultaneously – so your team can validate detection parity before full cutover. Ask the partner how they manage this transition and what criteria they use to confirm the legacy platform can be safely retired. Rushing this process is one of the most common causes of post-deployment gaps.
How will you integrate identity and cloud data sources?
Modern attacks rarely respect network boundaries. Identity misuse and cloud misconfiguration now sit at the centre of most significant breaches. Ask the partner specifically about their experience integrating identity providers like Microsoft Entra ID, Okta, Active Directory – and cloud platforms such as AWS, Azure and Google Cloud into Falcon Next-Gen SIEM. Authentication anomalies, privilege escalations and token misuse are high-signal events that should feed directly into your detection layer. Partners who treat SIEM as a network-centric tool and neglect identity telemetry will leave critical blind spots in your coverage.
How do you approach SOC workflow redesign and analyst training?
Platform migration is not just a technology change, it is an operational change. Alert triage models shift. Experienced analysts build instinct around familiar tools, and resistance to change is normal.
Ask the partner how they support SOC teams through this transition:
- Do they offer hands-on training tailored to your analysts’ existing skills?
- Do they provide guidance on restructuring alert prioritisation and escalation paths?
A partner who deploys the technology and then walks away, leaves your team to figure out the operational implications on their own.
What post-implementation support and ongoing tuning do you provide?
The work does not end after going live. Ask the partner what their post-deployment support model looks like – specifically how long they remain engaged after the initial implementation, what SLAs they offer for tuning requests and whether they provide ongoing detection content updates.
Partners who treat implementation as a one-time project rather than a continuous programme of improvement are unlikely to support your long-term security maturity goals.
How will you measure and report on deployment success?
Ask the partner how they define success for a CrowdStrike NG-SIEM implementation. A credible partner will track concrete operational metrics – detection latency before and after deployment, false positive rates, mean time to investigate, analyst handling time and reduction in dwell time.
These numbers show whether the implementation is delivering genuine security value or simply populating a new interface with the same volume of unactionable alerts. If a partner cannot articulate a measurement framework, it is worth asking what outcomes they are actually optimising for.
Red flags to watch for during partner evaluation
Not every partner who claims CrowdStrike expertise can deliver a production-grade NG-SIEM deployment. Watch for these warning signs during your evaluation process.
- Vague implementation timelines: Legitimate partners will scope your environment before committing to timelines. Partners who promise quick deployment without first understanding your architecture are definitely skipping critical steps.
- No parallel running strategy: Any partner recommending an immediate hard cutover from your legacy SIEM is introducing unnecessary risk. Parallel running is standard practice for a reason.
- No post-go-live engagement model: SIEM tuning is ongoing. Partners who treat the project as complete at go-live will leave you managing false positives and detection gaps without support.
- Inability to discuss detection engineering: If a partner cannot explain how they build, test and validate detection logic, they are likely relying entirely on default content – which is insufficient for most enterprise environments.
- No reference customers in your sector: Industry-specific experience matters, particularly for regulated organisations. Ask for references from similar environments before signing.
Conclusion
Choosing the right CrowdStrike NG-SIEM implementation partner is one of the most important decisions a security leader will make during a SOC transformation.
CrowdStrike Falcon Next-Gen SIEM is a powerful platform. But as the industry has seen, even the best technology delivers results only when it is implemented with care, precision and the right expertise by your side. The blog highlights a few of the important questions to ask a CrowdStrike NG-SIEM implementation partner. A strong partner will welcome these questions. They will have clear, evidence-based answers that reflect genuine deployment experience.
CyberNX is a certified CrowdStrike partner with deep expertise in Falcon Next-Gen SIEM deployments. We help CISOs and security leaders design, deploy and operationalise NG-SIEM environments that deliver real outcomes. Connect with us today for a CrowdStrike Consultation, and let’s build your NG-SIEM strategy together.
Questions to ask a CrowdStrike NG-SIEM implementation partner FAQs
How long does a CrowdStrike NG-SIEM implementation typically take?
Timelines vary depending on environment complexity, number of data sources and the scope of legacy SIEM migration. Simple deployments can be completed in four to eight weeks. Enterprise environments with large-scale data onboarding and legacy decommissioning typically take three to six months.
Do we need to replace our existing security tools to implement CrowdStrike NG-SIEM?
No. CrowdStrike Falcon Next-Gen SIEM is designed to ingest data from a wide range of third-party sources. The goal is to consolidate visibility, not necessarily to replace every existing tool immediately. Your implementation partner should help you map your existing stack to the new platform’s ingestion framework.
What is the difference between a CrowdStrike reseller and an implementation partner?
A reseller primarily handles licence procurement. An implementation partner provides technical design, deployment, data onboarding, detection engineering, SOC workflow support and ongoing tuning. For NG-SIEM, you need an implementation partner, not just a licence seller. CrowdStrike’s Services Partner Programme specifically identifies partners with proven delivery capabilities.
How does CrowdStrike NG-SIEM handle compliance logging and audit requirements?
Falcon Next-Gen SIEM supports configurable data retention periods up to 36 months, which meets the requirements of most compliance frameworks. It provides detailed audit trails of security events, user activities and policy adherence. Your implementation partner should be able to configure retention settings aligned to your specific regulatory obligations – whether that is PCI-DSS, ISO 27001, DPDPA or sector-specific frameworks.