Log data, although it is like an ocean, is where you find anomalies. And most often, this is how a SOC analyst or some other security professional prevents or responds to breaches. However, log storage grows much faster than expected. And when an audit begins, teams scramble to prove control and compliance.
This is a common pattern which can plague your organisation too. Data is either over-retained or not useful when needed. Both situations increase risk.
This is where log retention & compliance best practices using CrowdStrike NG-SIEM stand out. Unlike traditional SIEM platforms, NG-SIEM reshapes how logs are collected, stored, and used. In this blog, we focus on how to build a smarter retention strategy using its native capabilities and compliance best practices.
Traditional log retention strategies isn’t effective
Most log retention strategies were designed for older SIEM systems. They rely heavily on infrastructure, manual tuning, and rigid pipelines. That creates three problems precisely:
- First, ingestion becomes expensive. Teams limit what they collect to control cost. This creates blind spots.
- Second, retention policies are static. Logs are stored for fixed periods without considering actual value.
- Third, search and retrieval take time. During audits or incidents, delays become a serious issue.
CrowdStrike NG-SIEM approaches this differently. It uses a cloud-native architecture that decouples ingestion, storage, and analytics. This allows organisations to rethink retention without the usual trade-offs.
Compliance in a CrowdStrike NG-SIEM environment
Compliance means you have to prove integrity, accessibility, and relevance, and NG-SIEM helps you in this regard.
Aligning retention with regulatory intent
Regulations don’t just define duration. They expect secure storage, controlled access and traceable activity. With CrowdStrike NG-SIEM, logs are tied to unified telemetry across endpoints, identities, and workloads. This improves traceability, which auditors care about.
Supporting data minimisation without losing visibility
A common challenge is balancing GDPR requirements with security needs. In Indian context, it would be DPDPA. NG-SIEM helps by enabling selective retention. You can retain enriched, high-value data instead of raw, redundant logs. This supports compliance while maintaining detection capability.
Ensuring audit readiness at all times
Audit preparation often becomes a separate project. With NG-SIEM, real-time search and centralised visibility mean your logs are always ready. There is no need to reconstruct timelines from multiple tools.
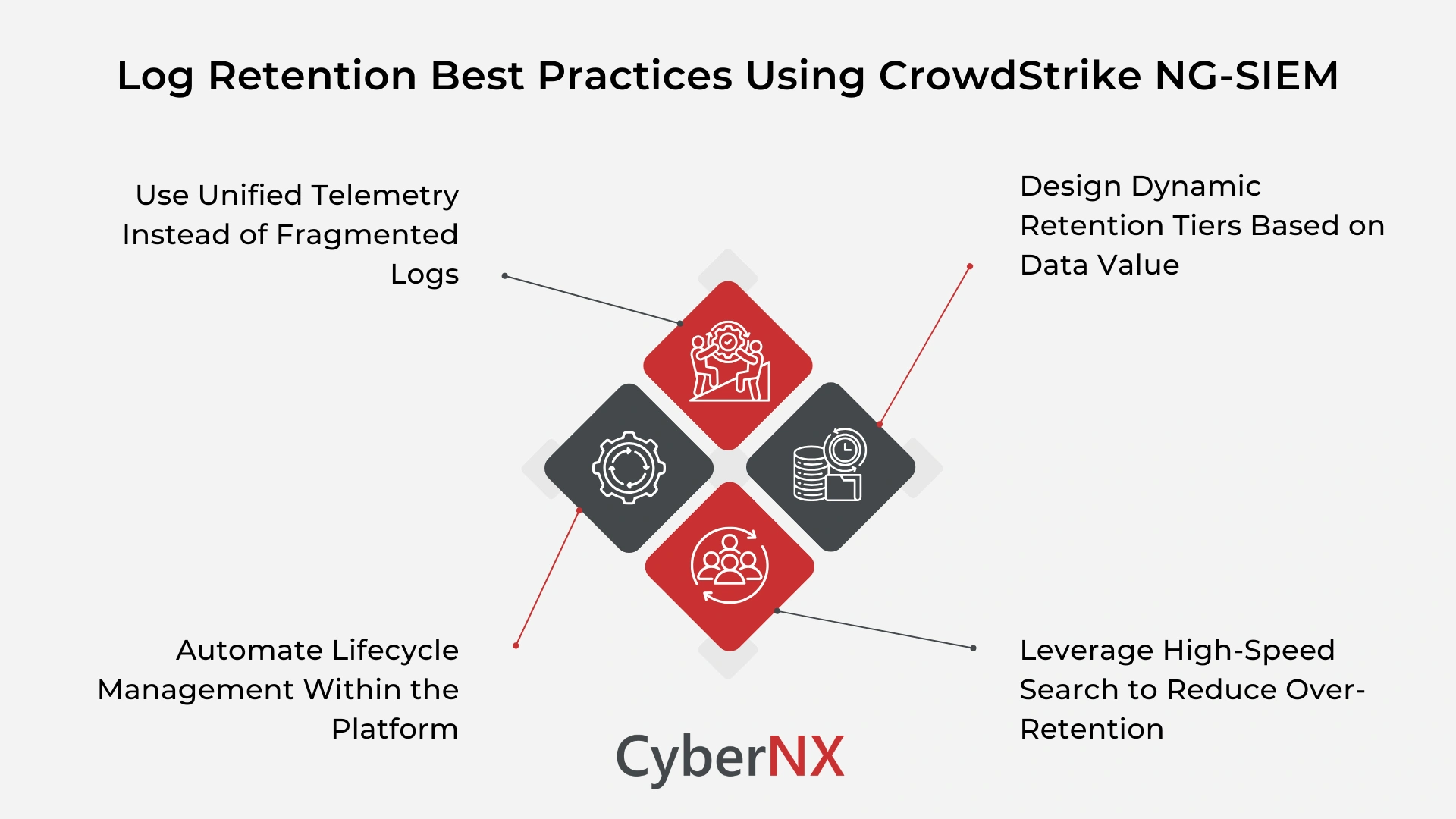
Key log retention best practices using CrowdStrike NG-SIEM
To get real value, retention strategies must align with how the platform works.
Use unified telemetry instead of fragmented logs
Traditional SIEM tools depend on multiple log sources stitched together. CrowdStrike NG-SIEM collects telemetry natively from the Falcon platform. This includes endpoint, identity, and cloud signals in one stream. This changes retention strategy. Instead of storing duplicate logs across tools, you retain a single, enriched dataset. The result is good visibility with less storage overhead.
Design dynamic retention tiers based on data value
Static retention policies don’t work well in modern environments. With NG-SIEM, you can define retention tiers based on:
- Threat relevance
- Investigation frequency
- Compliance requirements
For example, endpoint detection data may need longer retention than routine system logs. Because storage is decoupled, you can scale retention without redesigning infrastructure.
Leverage high-speed search to reduce over-retention
Many organisations retain excess data because retrieval is slow. They fear losing critical evidence. CrowdStrike NG-SIEM offers fast search across large datasets. This changes behaviour. Teams can confidently reduce retention periods for low-value data because relevant logs are easy to find and investigations do not depend on excessive storage. This directly impacts cost optimisation.
Automate lifecycle management within the platform
Manual retention enforcement creates inconsistency. NG-SIEM allows automated lifecycle policies. Logs move through stages:
- Active analysis
- Warm storage
- Archive or deletion
This ensures compliance policies are consistently applied without manual effort. It also reduces operational overhead for security teams.
How CrowdStrike NG-SIEM strengthens compliance outcomes
The real advantage lies in how the platform integrates retention with security operations.
Built-in data integrity and immutability
Logs must remain tamper-proof. CrowdStrike NG-SIEM supports secure storage mechanisms that maintain integrity. This ensures logs remain reliable during audits or legal investigations.
Real-time visibility across the environment
Compliance often requires proving “who did what and when.” Because NG-SIEM unifies telemetry, you can track activity across endpoints, users, and workloads in one place. This eliminates gaps that auditors often flag.
Simplified reporting and evidence collection
Audit reporting can drain resources. With NG-SIEM, teams can quickly generate reports using centralised data. There is no need to manually correlate logs from different systems. This reduces audit preparation time significantly.
Practical use case: PCI compliance with CrowdStrike NG-SIEM
Let’s make this real. A financial organisation needs to meet PCI DSS requirements. This includes:
- Retaining logs for at least one year
- Monitoring access to sensitive systems
- Providing audit trails on demand
Using CrowdStrike NG-SIEM, the organisation can:
- Collect endpoint and user activity through Falcon telemetry
- Retain high-value security logs for one year
- Archive less critical data with automated policies
- Use fast search to retrieve logs instantly during audits
The result is a compliant and scalable log retention model.
Conclusion
Log retention should not slow your security team down. It should support faster decisions, stronger investigations, and smoother audits. Log retention & compliance best practices using CrowdStrike NG-SIEM show how this can be achieved. By leveraging unified telemetry, dynamic retention, and automated lifecycle management, organisations can simplify compliance while improving visibility.
At CyberNX, we offer CrowdStrike Consulting services, helping organisations to design NG-SIEM strategies that fit their environment. From architecture to optimisation, we help you get measurable value from your investment.
If you are looking to optimise log retention using CrowdStrike NG-SIEM, speak with our experts to build a compliant, cost-effective, and scalable strategy tailored to your business.
Log retention & compliance best practices using CrowdStrike NG-SIEM FAQs
How is CrowdStrike NG-SIEM different from traditional SIEM for log retention?
It uses a cloud-native architecture with unified telemetry, allowing flexible retention without heavy infrastructure management.
Can CrowdStrike NG-SIEM handle long-term log retention for compliance?
Yes, it supports scalable storage and automated lifecycle policies for long-term retention needs.
Does NG-SIEM reduce the need for multiple logging tools?
Yes, it consolidates telemetry across endpoints, identity, and cloud, reducing reliance on separate tools.
How does NG-SIEM improve audit readiness?
It provides fast search, centralised logs, and built-in reporting, making audit evidence easy to access.