Strategic detection engineering in the hands of security teams often leads to detection of real threats. This is even more true with platforms like CrowdStrike NG-SIEM, where speed, scale, and signal fidelity define success.
Many teams choose today are bogged down by noisy detections, poor correlation, and limited visibility across environments, which ultimately leads to alert fatigue, missed threats, and inefficient SOC operations. That calculus does not work anymore. A structured, platform-native detection engineering approach significantly improves both detection quality and response speed.
In this blog, we explore detection engineering best practices in CrowdStrike NG-SIEM with a strong focus on technical depth, operational clarity, and measurable outcomes.
Detection engineering in CrowdStrike NG-SIEM
Detection engineering in CrowdStrike NG-SIEM means you are designing high-confidence detections that leverage the Falcon platform’s telemetry, threat intelligence, and real-time processing capabilities.
Unlike traditional SIEMs, CrowdStrike NG-SIEM operates on a unified data model built on endpoint, identity, and cloud telemetry. This allows detection engineers to move beyond siloed logic and build context-rich detections. You can also enrich detections using features such as:
- Native Falcon telemetry
- Real-time threat intelligence
- Cross-domain correlation across endpoints, identities & workloads
This initiates a massive change in the way detection logic is built because of its focus on behavioural patterns and adversary techniques.
Are there challenges in detection engineering?
Of course, there are challenges. Therefore, before diving into best practices, it is important to recognise where most organisations struggle.
- Alert noise and false positives: Many detections are overly broad. They trigger frequently but lack context. This overwhelms analysts and slows response.
- Poor mapping to adversary behaviour: Detections often fail to align with frameworks like MITRE ATT&CK. This creates gaps in coverage and weakens threat visibility.
- Limited use of native platform capabilities: Teams often treat CrowdStrike NG-SIEM like a traditional SIEM. This leads to underutilisation of its real-time analytics and telemetry depth.
- Lack of continuous tuning: Detection engineering is not a one-time effort. Without regular tuning, detections become outdated and ineffective.
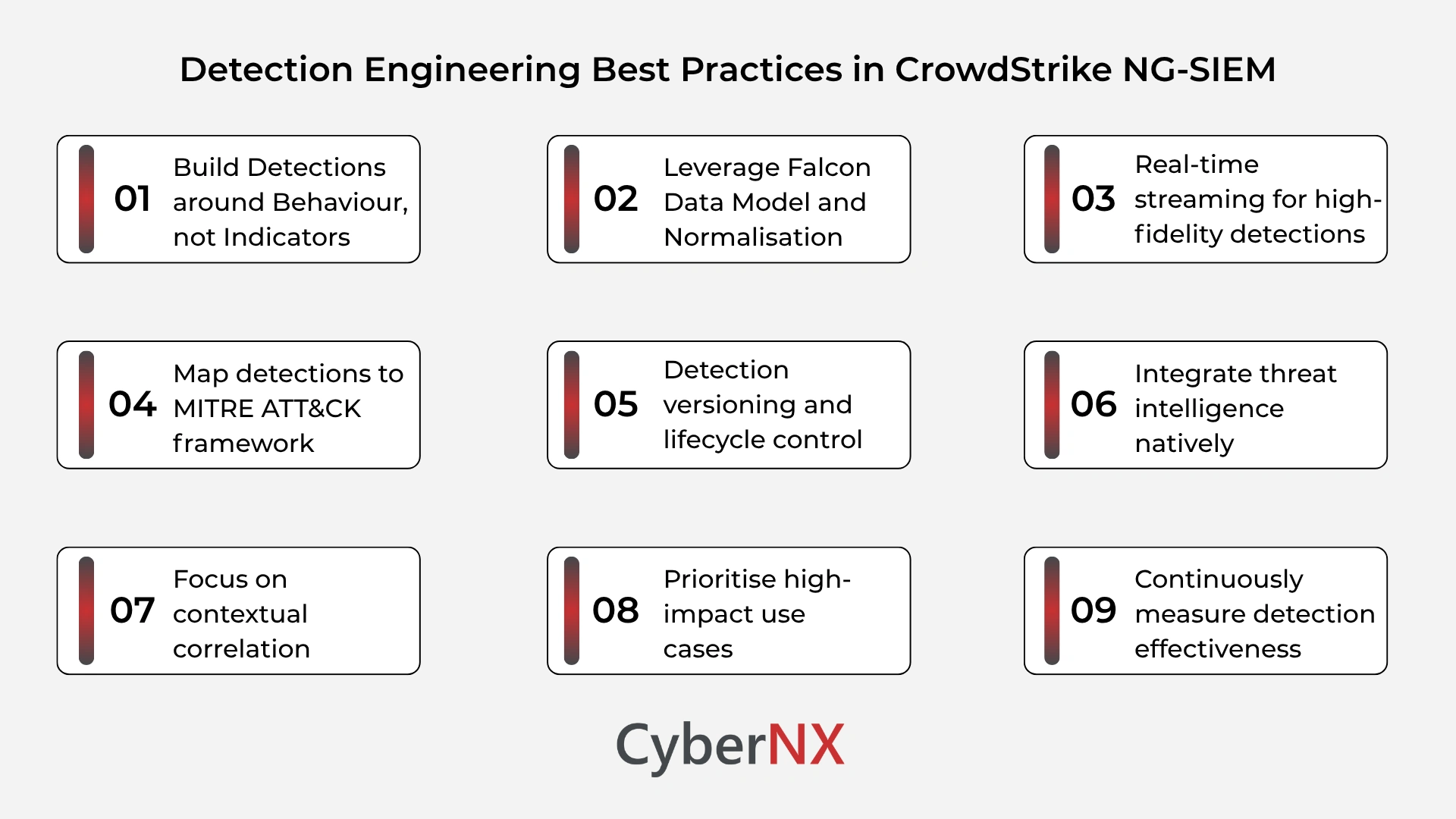
Detection engineering best practices in CrowdStrike NG-SIEM
Technical precision and operational discipline are core pillars on which a strong detection engineering programme is built. These are some practices that consistently deliver results in our experience:
1. Build detections around behaviour, not indicators
Indicator-based detections are easy to implement but easy to evade. CrowdStrike NG-SIEM provides rich behavioural telemetry that allows you to detect patterns rather than static values. Focus on process execution chains and command-line anomalies.
For example, instead of detecting a known malicious hash, build logic that identifies suspicious PowerShell execution with encoded commands and unusual parent processes. This approach improves detection resilience and reduces dependency on threat feeds.
2. Leverage Falcon data model and normalisation
CrowdStrike NG-SIEM standardises data across sources. Detection engineers should align queries and rules with this model. This ensures:
- Consistent detection logic across environments
- Easier correlation between endpoint, identity, and cloud signals
- Faster query performance
Avoid building detections on raw or unstructured data when normalised fields are available. This small shift can significantly improve detection accuracy.
3. Use real-time streaming analytics for high-fidelity detections/ Real-time streaming for high-fidelity detections
One of the most powerful capabilities in CrowdStrike NG-SIEM is real-time data processing. Instead of relying only on scheduled queries, design detections that trigger instantly on suspicious behaviour. Plus, correlate multiple events in near real time and reduce dwell time of threats.
For example, detecting lateral movement attempts should not depend on delayed batch processing. Real-time correlation between login anomalies and endpoint activity provides faster insights.
4. Map detections to MITRE ATT&CK framework
Every detection should have a clear purpose. Mapping detections to MITRE ATT&CK techniques ensures structured coverage. This helps teams:
- Identify detection gaps
- Prioritise high-risk techniques
- Align with threat intelligence
In CrowdStrike NG-SIEM, detections enriched with ATT&CK context become easier to triage and investigate.
5. Implement detection versioning and lifecycle management/ Detection versioning and lifecycle control
Detection engineering should follow a lifecycle, similar to software development. Each detection must have version control, testing before deployment and clear documentation. Over time, detections should be:
- Tuned based on false positives
- Retired if no longer relevant
- Updated with new threat intelligence
This disciplined approach prevents detection sprawl and keeps your SOC efficient.
6. Integrate threat intelligence natively
CrowdStrike provides built-in threat intelligence that can enrich detections automatically. Instead of manually adding indicators, leverage adversary profiles, known tactics and techniques and real-time intelligence feeds. This enables detections that are not only reactive but also predictive. For instance, if a known adversary group uses specific lateral movement techniques, detections can be tuned to prioritise those behaviours.
7. Focus on contextual correlation
Single-event detections often lack depth. CrowdStrike NG-SIEM enables multi-event correlation across domains. Strong detections combine endpoint activity, identity signals and network behaviour. For example, a failed login attempt may not be suspicious alone. But when combined with unusual process execution on the same host, it becomes a high-confidence signal. Context reduces noise and increases detection accuracy.
8. Prioritise high-impact use cases
Not all detections are equal. Focus first on scenarios that have the highest business impact. These typically include privilege escalation, lateral movement and data exfiltration. By prioritising these, security teams can improve risk coverage quickly without being overwhelmed.
9. Continuously measure detection effectiveness
Detection engineering must be measurable. Track metrics such as:
- True positive rate
- False positive rate
- Mean time to detect
Regular reviews help identify weak detections and improve overall performance.
Conclusion
Detection engineering best practices in CrowdStrike NG-SIEM go beyond writing rules. They require a strategic approach that combines behavioural analysis, real-time processing, and continuous improvement.
When done right, detection engineering transforms your SOC from reactive to proactive. It reduces noise, improves visibility, and strengthens your overall security posture.
Here at CyberNX, our team of experts align with security teams to design, implement, and optimise detection engineering programmes tailored to CrowdStrike environments. If you are looking to improve detection quality and SOC efficiency, contact us today for a CrowdStrike Consultation.
Detection engineering best practices in CrowdStrike NG-SIEM FAQs
How is CrowdStrike NG-SIEM different from traditional SIEM for detection engineering?
CrowdStrike NG-SIEM offers real-time analytics, unified telemetry, and native threat intelligence. This allows more advanced and context-driven detections compared to traditional SIEMs.
What skills are required for effective detection engineering in CrowdStrike?
Teams need strong knowledge of adversary tactics, query languages, Falcon telemetry, and data correlation techniques.
How often should detections be reviewed and updated?
Detections should be reviewed regularly, ideally every quarter or after major threat intelligence updates or incidents.
Can detection engineering reduce SOC workload?
Yes. High-quality detections reduce false positives and improve alert prioritisation, making SOC operations more efficient.