Phishing is the most common form of cyberattack in the world. According to estimates, billions of phishing emails are sent every day, and millions of phishing attacks are recorded year after year.
What about fake domains? In 2025, World Intellectual Property Organization (WIPO) reportedly handled 6000+ domain dispute cases. A report from Decodo revealed 68% rise in digital squatting scams in the past five years. In 2026, attackers replicate company websites within hours and launch campaigns that look legitimate even to trained employees.
This is where brand risk monitoring is helping to identify and stop phishing and fake domains before they cause harm.
Phishing: the perennial cybercrime
Phishing has been a cybersecurity problem, perhaps, for the longest of time. Now, attackers are using sophisticated attack methods to execute phishing campaigns, blending social engineering with brand impersonation. Poor grammar or obvious tricks have given way to legitimate-looking messages.
Customer deception
What’s one thing that hasn’t changed? Phishing campaigns targeting customers using fake emails that appear to come from trusted brands. These emails push users to click links, enter credentials, or complete transactions.
Take a look at this example:
Way back in 2023, banking institutions faced coordinated phishing campaigns where attackers mimicked official email formats and branding. Customers unknowingly shared login credentials, leading to significant financial losses.
While the breach did not occur within the bank’s systems, the financial burden and customer compensation fell on the institution.
Brand reputation erosion at scale
When a phishing campaign traps and impacts customers, it can trigger widespread distrust. In 2022, several global e-commerce companies were targeted with phishing emails directing users to fake checkout pages. Customers who lost money shared their experiences online. Consequently, a wave of negative sentiment swept those brands affecting the bottom line.
Business email compromise
Phishing attacks is a major headache for employees. Hackers impersonate executives or vendors to manipulate internal processes. Such an incident occurred in 2021. A company received fraudulent payment instructions from what appeared to be a trusted supplier. The email domain looked nearly identical to the original. Funds were transferred before the fraud was detected. Such attacks disrupt operations and expose gaps in internal verification processes.
The menace of fake domains
Fake domains are the backbone of modern phishing campaigns. They are designed to look nearly identical to legitimate brand domains, making detection difficult for the average user.
Large-scale brand impersonation
So, how is it done? Attackers first register domains that closely resemble your official website. This includes minor spelling variations or alternative extensions. For example, instead of a legitimate domain, attackers may use slight changes that are easy to miss. These domains host websites that replicate login portals, payment pages, or customer support interfaces.
Loss of customer trust and engagement
When customers interact with fake domains, the experience often ends in fraud or failed transactions. This directly impacts how they perceive the brand. Even if the organisation is not technically compromised, customers tend to blame the brand. This reduces engagement and increases churn.
Abuse of marketing and digital campaigns
Fake domains are sometimes used to hijack marketing efforts. Attackers create websites that mimic promotional campaigns, discounts, or product launches. In 2024, several retail brands faced issues where fake domains promoted non-existent offers. Customers who engaged with these sites were either defrauded or misled. This diluted the effectiveness of genuine campaigns.
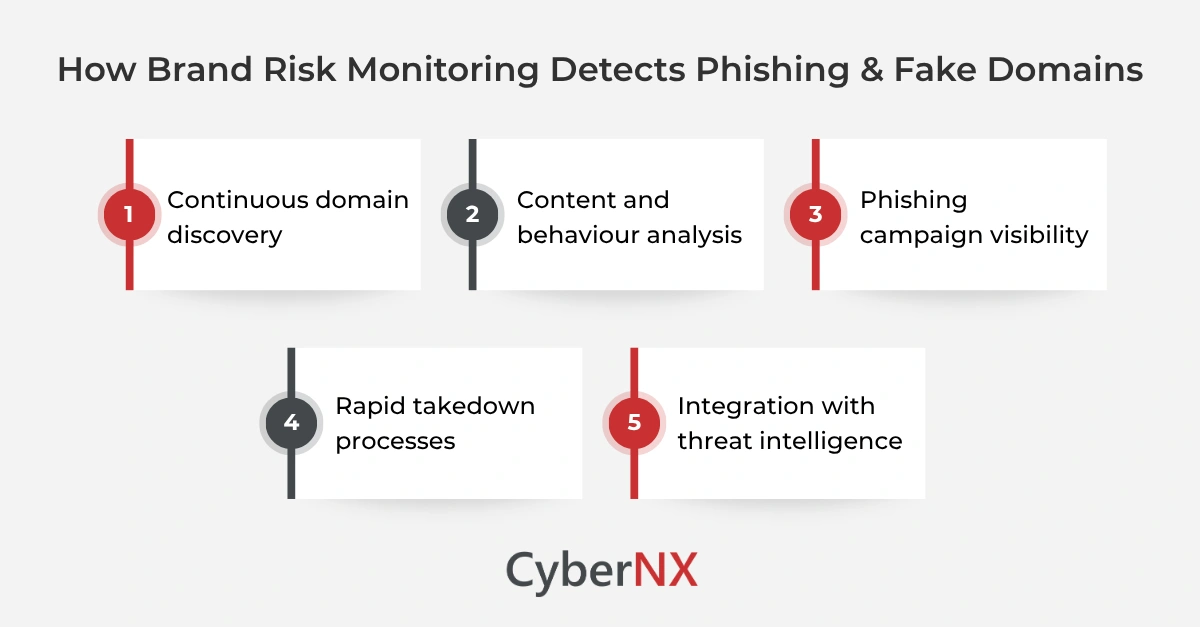
Brand risk monitoring to the rescue
Brand risk monitoring focuses on the external threat landscape. It continuously scans, analyses, and responds to risks targeting your brand.
Continuous domain discovery
Monitoring solutions track newly registered domains across global registries. They identify domains that resemble your brand using pattern recognition and similarity checks. This includes variations in spelling, prefixes, and domain extensions. Early detection allows teams to investigate before the domain becomes active in an attack.
Content and behaviour analysis
Once a suspicious domain is identified, the next step is analysing its content. Monitoring tools assess whether the site hosts:
- cloned login pages
- replicated branding
- data collection forms
This helps confirm whether the domain is being used for phishing or remains dormant.
Phishing campaign visibility
Brand risk monitoring extends beyond domains. It identifies phishing campaigns across email, social media, and messaging platforms. By correlating data from multiple sources, it uncovers coordinated campaigns early. This is critical in stopping attacks before they scale.
Rapid takedown processes
Speed is crucial in reducing impact. Monitoring platforms support takedown efforts by coordinating with domain registrars and hosting providers. This shortens the lifespan of malicious domains and reduces exposure to customers.
Integration with threat intelligence
Advanced solutions enrich findings with threat intelligence. This provides context such as attacker history, infrastructure patterns, and risk scores. It helps security teams prioritise high-risk threats and respond effectively.
Conclusion
Phishing and fake domains have become direct threats to brand value and customer trust. They operate outside traditional security boundaries, making them harder to detect with standard controls. Brand risk monitoring addresses this gap. It provides visibility into external threats, enabling early detection and faster response.
At CyberNX, we help organisations to identify brand abuse and reduce exposure to phishing and fake domains. If you want to strengthen your external threat visibility, now is the time to act. Connect with our experts to learn more about our brand risk monitoring capabilities.
How brand risk monitoring detects phishing and fake domains FAQs
How do attackers create convincing phishing campaigns today?
Attackers use automation, stolen branding assets, and AI-generated content to create highly realistic phishing messages and websites.
What is the difference between spoofed emails and fake domains?
Spoofed emails manipulate sender information, while fake domains involve registering lookalike websites to deceive users.
How long do fake domains typically remain active?
Without monitoring, fake domains can remain active for days or weeks. With proper detection, they can be taken down much faster.
Can brand risk monitoring integrate with existing security tools?
Yes. Most modern solutions integrate with SIEM, SOAR, and threat intelligence platforms for better visibility and response.