A modern enterprise generates massive amount of data, which is then fed into a SIEM. A centralized plcatform which assesses the data collected and find Indicators of Compromise (IOCs). CrowdStrike NG-SIEM is one such tool and helps in making sense of logs that flow in from endpoints, cloud platforms, identity providers, and network controls. Security leaders expect the SIEM to drive fast detection and confident investigations. But that only happens when data is properly parsed and normalised.
We have observed time and again teams focusing on detection rules while ignoring the quality of underlying data. As a result, alerts lack context, correlation rules fail quietly and analysts spend more time fixing data than investigating threats.
This blog looks at how to approach data normalization and parsing in a way that supports detection outcomes within CrowdStrike NG-SIEM.
Why data structure matters more in CrowdStrike NG-SIEM
Modern SIEM platforms have evolved. CrowdStrike NG-SIEM is built with a cloud-native architecture and flexible schema handling. That changes how teams should think about data.
Unlike traditional SIEMs that enforce rigid schemas upfront, this platform allows more flexibility through schema-on-read. That sounds convenient and sure it is. But it also introduces a subtle risk.
If teams delay normalisation for too long, inconsistencies start creeping into detection logic. For example, one data source may log an IP as src_ip, while another uses source.ip. Both exist and work independently. But correlation across them becomes unreliable. Over time, this creates hidden blind spots. Flexibility works best when paired with intentional structure. Not rigid. But consistent where it matters.
Where parsing breaks down in real environments
Most parsing issues show up later, when detection use cases mature. One common scenario involves identity logs. A team ingests authentication data from multiple providers. Initially, everything seems fine. But during an investigation, analysts realise that user identifiers are inconsistent. One log uses email while another uses username. And a third uses a unique ID. The data exists. But it cannot be stitched together easily.
Another issue appears with third-party integrations. While Falcon telemetry inside CrowdStrike NG-SIEM is already well-structured, external logs often are not. Firewall logs, SaaS audit trails, and custom application logs all require careful parsing.
Without that effort, detection rules become overly complex or worse, ineffective. Then there is over-parsing. Teams sometimes extract every possible field, assuming more data equals better visibility. In reality, this slows down queries and adds noise.
A more focused approach works better. Let’s see what the best practices which you can follow.
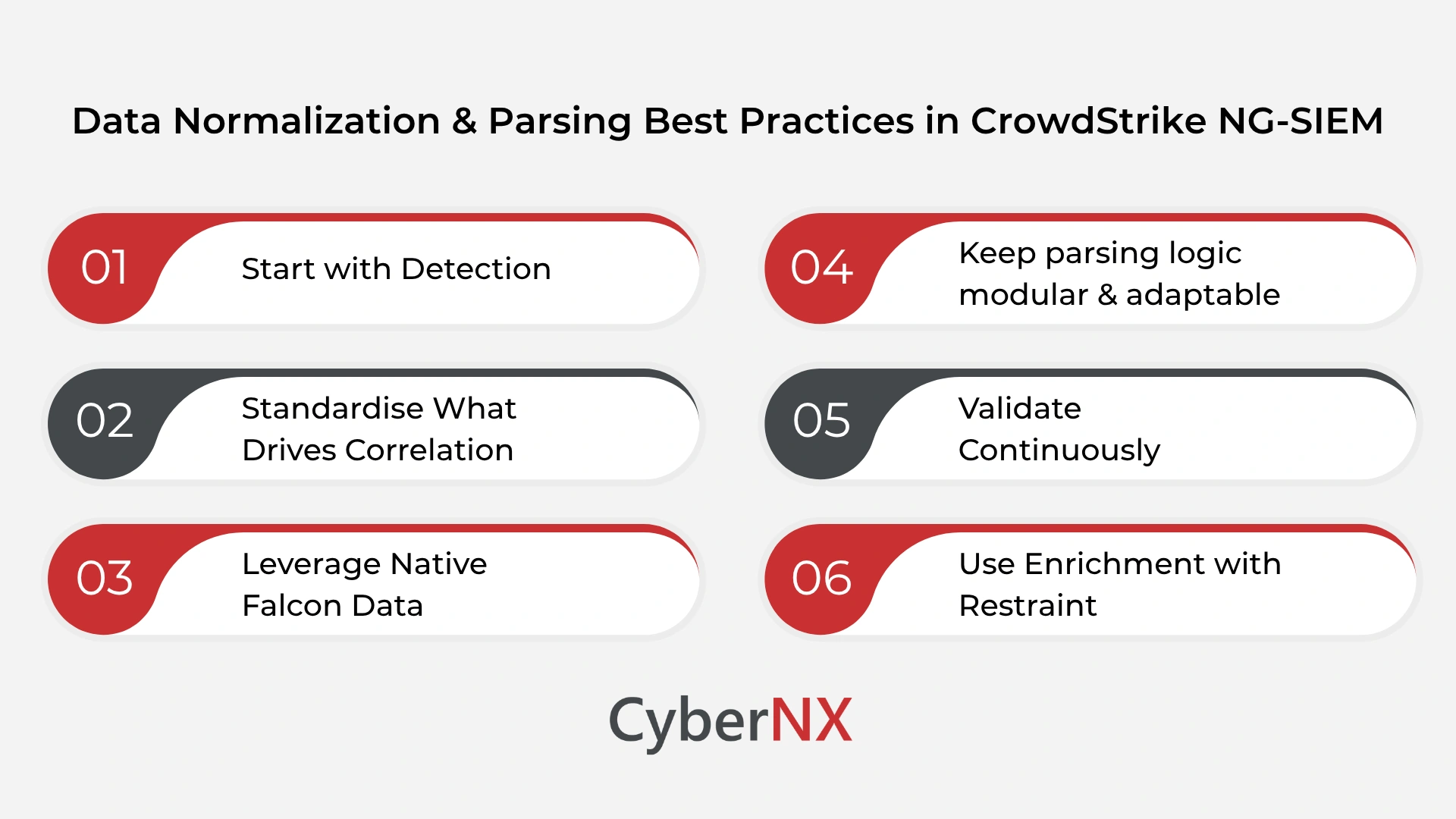
Best practices: data normalization & parsing in CrowdStrike NG-SIEM
A more focused approach works better. Let’s see what the best practices which you can follow.
1. Start with detection
It is tempting to normalise everything upfront. But that rarely delivers value. Instead, begin with key detection scenarios. Think about what your SOC needs to identify. Lateral movement, privilege escalation or suspicious logins. Then work backwards. Ask what fields are essential for those detections. Focus parsing efforts there first. This keeps the process aligned with outcomes, not assumptions.
2. Standardise what drives correlation
In a flexible schema environment, not every field needs strict normalisation. Focus on high-impact fields such as:
- User identifiers
- IP addresses
- Hostnames
When these are consistent, cross-source correlation becomes far more reliable. Everything else can remain flexible if needed. This balance keeps performance strong without sacrificing accuracy.
3. Leverage native Falcon data
One advantage of CrowdStrike NG-SIEM is its deep integration with Falcon telemetry. Endpoint data is already structured and enriched. That reduces the need for heavy parsing. The smarter approach is to treat this as your baseline. Build detections using native data first. Then extend with third-party logs where necessary. This reduces complexity and speeds up time to value.
4. Keep parsing logic modular & adaptable
Parsing rules should evolve. This is because log formats change and vendors update schemas. Instead of building large, rigid parsing pipelines, break them into smaller components. This makes updates easier and reduces the risk of cascading failures. It also helps teams troubleshoot faster when something breaks.
5. Validate continuously
Parsing failures are rarely obvious. They often go unnoticed until a detection fails. That is why continuous validation matters. Simple checks can make a big difference:
- Are critical fields consistently populated?
- Have any field formats changed recently?
These checks do not need to be complex. But they should be regular.
6. Use enrichment with restraint
Context improves investigations. But too much enrichment can slow performance. Adding geo-location or threat intelligence tags is useful. However, not every event needs full enrichment. Focus on high-risk or high-value events. This keeps queries efficient while still providing context where it matters.
Improving your current setup
Improving parsing and normalization does not require a complete overhaul.
Start by reviewing your current data pipeline inside CrowdStrike NG-SIEM. Look for inconsistencies in key fields. Pay attention to where correlation rules fail or produce unexpected results. Then prioritise fixes based on impact. Identity and endpoint data usually offer the quickest gains.
It also helps to involve multiple teams. Parsing is not just a SOC concern. Application owners and infrastructure teams often understand log structures better. Their input can save time and reduce errors.
Conclusion
Data normalization and parsing are not background tasks. They directly influence how well your SOC performs. In CrowdStrike NG-SIEM, the flexibility of schema handling gives teams more control. But it also demands clearer decisions around what to standardise and when. When done right, the impact is immediate. Cleaner alerts, faster investigations and more reliable detections.
CyberNX is one of leading CrowdStrike Consulting providers in India. Our partnership with CrowdStrike and highly qualified team consisting of SOC experts can help your security team to refine data pipelines and align them with real detection goals. If you are looking to improve detection accuracy and reduce SIEM noise, connect with us for a focused assessment of your CrowdStrike NG-SIEM data strategy. Let’s turn your data into a stronger security advantage.
Data normalization and parsing best practices in CrowdStrike NG-SIEM FAQs
How does schema-on-read impact normalization strategy in CrowdStrike NG-SIEM?
Schema-on-read allows flexibility during ingestion, but teams still need to standardise key fields to ensure reliable detection and correlation.
What types of logs require the most parsing effort?
Third-party logs such as firewalls, SaaS platforms, and custom applications usually need more parsing compared to native Falcon telemetry.
How can over-parsing affect SIEM performance?
Extracting too many fields increases data volume and query complexity, which can slow down investigations.
What is the first step to improving parsing in an existing SIEM?
Start by identifying inconsistencies in critical fields used for detection and prioritise fixes based on impact.