Raw data alone does not help security teams stop attacks. The real value comes from well-designed detection logic that identifies suspicious behaviour early.
Understanding how to design detection rules in CrowdStrike NG-SIEM becomes essential for organisations building a mature SOC. Effective detection rules allow teams to surface meaningful threats quickly while reducing unnecessary alerts.
CrowdStrike’s Next-Generation SIEM combines Falcon telemetry, third-party integrations and advanced analytics. However, even powerful platforms require thoughtful rule design. Security teams must align detections with real-world attack techniques, business risks and operational workflows.
In this guide, we explore practical steps for designing detection rules that help SOC teams identify threats faster and respond with confidence.
Detection engineering in modern SOCs
Security teams often struggle with alert fatigue. Thousands of alerts appear every day, yet only a small fraction represent genuine threats. This happens when detection rules are poorly tuned or disconnected from attacker behaviour. The result is wasted analyst time and delayed response to real incidents.
Detection engineering solves this challenge by focusing on high-signal indicators tied to attacker tactics.
Well-designed rules within CrowdStrike NG-SIEM help organisations:
- Identify threats earlier in the attack chain
- Reduce false positives across large datasets
- Align monitoring with frameworks like MITRE ATT&CK
- Improve SOC efficiency and response times
When detection logic reflects real adversary techniques, the SIEM becomes far more valuable to security teams.
Key principles for designing detection rules
Before building rules inside CrowdStrike NG-SIEM, security teams should define clear design principles. These principles guide detection quality and long-term maintainability.
1. Align detections with attacker behaviour
Detection rules work best when tied to real attack techniques rather than isolated indicators.
Frameworks like MITRE ATT&CK help security teams map behaviours such as privilege escalation, credential dumping or lateral movement. These behaviours remain consistent across many attack campaigns.
For example, monitoring suspicious PowerShell execution or unusual credential access patterns often surfaces real threats earlier than relying on simple IOC matching.
This behaviour-driven approach helps CrowdStrike NG-SIEM detections remain effective even when attackers change tools or infrastructure.
2. Focus on high fidelity signals
Too many SIEM alerts originate from weak signals. High fidelity signals combine multiple attributes that strongly indicate malicious activity. For instance, a single failed login may not matter. But repeated failed logins followed by a successful authentication from a new location might indicate a brute-force attempt.
CrowdStrike NG-SIEM enables analysts to correlate multiple event types across telemetry sources. This correlation helps transform noisy events into meaningful detections.
3. Use contextual enrichment
Context improves detection accuracy. Modern SIEM environments ingest telemetry from endpoints, identity providers, cloud services and network infrastructure. Detection rules should leverage this context whenever possible.
Examples of useful enrichment include:
- Asset criticality
- User privilege level
- Geographic login anomalies
- Known administrative tools
- Threat intelligence indicators
With CrowdStrike NG-SIEM, enriched telemetry allows analysts to detect threats that appear benign in isolation but dangerous when viewed in context.
4. Design rules that analysts can investigate
Detection rules must support investigation. Each alert should provide enough information for analysts to begin triage immediately. This means including fields such as process names, command-line parameters, user accounts and host details.
Clear context reduces investigation time and helps SOC teams respond faster. Detection engineering is not just about identifying activity. It is about making that activity understandable.
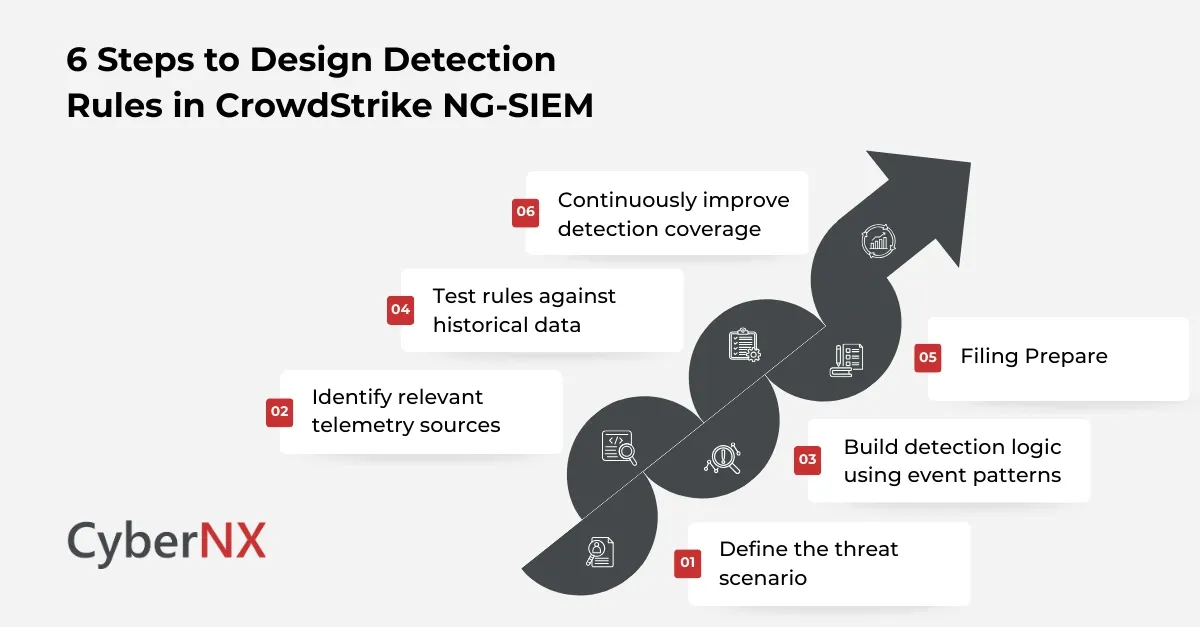
Steps to design detection rules in CrowdStrike NG-SIEM
Creating effective rules requires a structured approach. The following steps help security teams design reliable detections.
1. Define the threat scenario
Every rule should begin with a clear threat hypothesis.
Ask simple questions:
- What attack technique are we trying to detect?
- Which systems could be affected?
- What signals indicate this behaviour?
For example, a detection scenario might focus on identifying suspicious credential dumping attempts from endpoint hosts. By defining the scenario clearly, detection logic becomes easier to build and validate.
2. Identify relevant telemetry sources
Detection rules depend on reliable data. CrowdStrike NG-SIEM integrates several telemetry streams, including Falcon endpoint data, identity logs and cloud activity. Analysts should confirm that required events exist before writing a rule.
Common telemetry sources include:
- Endpoint process execution logs
- Authentication activity
- Network connection events
- Cloud control plane logs
- Privilege escalation events
Choosing the right telemetry ensures the rule captures meaningful behaviour.
3. Build detection logic using event patterns
Once telemetry is identified, analysts can create detection queries that describe suspicious patterns.
These patterns may involve:
- Specific command execution
- Rare process relationships
- Abnormal login behaviour
- Suspicious network connections
For example, a rule might detect PowerShell launching encoded commands followed by outbound network communication. Such patterns often indicate attacker activity rather than legitimate administration. CrowdStrike NG-SIEM query capabilities allow teams to search across large event datasets efficiently.
4. Test rules against historical data
Testing is a crucial step in detection engineering. Before deploying a new rule, analysts should run it against historical telemetry to evaluate accuracy. This helps answer key questions:
- Does the rule trigger frequently?
- Are alerts legitimate or noisy?
- Are important events missed?
Testing helps refine the rule before it enters production. Security teams often discover small adjustments dramatically improve detection quality.
5. Tune rules to reduce false positives
Even strong detection logic requires tuning. False positives occur when legitimate activities resemble malicious behaviour. Detection rules must account for common administrative workflows.
Examples of tuning strategies include:
- Excluding known management tools
- Filtering expected service accounts
- Limiting detections to sensitive systems
- Adjusting threshold values
CrowdStrike NG-SIEM allows security teams to fine-tune rules while maintaining strong detection coverage.
6. Continuously improve detection coverage
Threat landscapes evolve quickly. Detection rules should evolve as well. Security teams should review rule performance regularly and update detections when new techniques appear. Threat intelligence reports, incident learnings and red team exercises often reveal gaps in detection logic. Continuous improvement keeps detection rules relevant and effective.
“Detection engineering is the foundation of effective SOC operations. Behaviour-based detection helps security teams identify attackers even when traditional indicators fail.”
Source: SANS Institute Detection Engineering Research
This insight highlights why modern SIEM deployments focus heavily on behavioural detection rather than simple IOC matching.
Common detection use cases in CrowdStrike NG-SIEM
Security teams often prioritise specific threat scenarios when building detection rules.
Typical use cases include:
- Suspicious PowerShell or command-line activity
- Credential dumping attempts
- Privilege escalation behaviour
- Lateral movement across endpoints
- Cloud account compromise indicators
By focusing on high-risk attack paths, organisations gain meaningful visibility into attacker activity.
Conclusion
Understanding how to design detection rules in CrowdStrike NG-SIEM is a key capability for modern security teams. Strong detection logic transforms raw telemetry into actionable intelligence that helps SOC analysts identify threats quickly.
By aligning detections with attacker behaviour, using enriched telemetry and continuously tuning rules, organisations can significantly improve threat visibility.
At CyberNX, we work closely with security teams to strengthen detection strategies across SIEM and XDR platforms. Our approach focuses on practical improvements that reduce noise, accelerate investigations and improve security outcomes.
If your team is exploring CrowdStrike NG-SIEM, connect with us for a CrowdStrike consultation.
How to design detection rules in CrowdStrike NG-SIEM FAQs
What is detection engineering in SIEM platforms?
Detection engineering is the process of designing, testing and maintaining rules that identify malicious activity within SIEM telemetry. It focuses on behaviour-based detection rather than simple indicator matching.
How does CrowdStrike NG-SIEM improve threat detection?
CrowdStrike NG-SIEM combines Falcon telemetry, third-party log ingestion and advanced analytics. This enables security teams to correlate events across multiple sources and detect complex attack behaviours.
How often should detection rules be reviewed?
Security teams should review detection rules regularly. Many mature SOCs evaluate rule performance monthly and update logic whenever new attack techniques emerge.
What causes false positives in SIEM detections?
False positives often occur when legitimate administrative activity resembles attacker behaviour. Proper rule tuning, contextual enrichment and telemetry correlation help reduce these alerts.