If your employee credentials appear in an underground forum tonight, would your SOC know tomorrow morning?
Security teams often use “dark web” and “deep web” interchangeably. But for CISOs and CXOs, the difference between the two is very real. It defines monitoring scope, intelligence strategy, and response readiness.
Understanding dark web vs deep web monitoring is important to build a mature digital risk protection program.
This guide breaks down the differences, explains what security teams should monitor, and clarifies how each approach fits into enterprise cybersecurity strategy.
What is the deep web?
The deep web refers to internet content that is not indexed by search engines.
This includes:
- Internal corporate portals
- Cloud storage dashboards
- SaaS platforms
- Academic databases
- Private customer portals
- Webmail interfaces
The deep web is not inherently malicious. In fact, most legitimate business operations exist there.
But sensitive data leaks often surface in deep web environments before becoming publicly visible. Monitoring this layer is essential for early exposure detection.
What is the dark web?
The dark web is a subset of the deep web that requires special tools like Tor to access.
It is intentionally hidden and often associated with:
- Threat actor marketplaces
- Stolen credential dumps
- Ransomware leak sites
- Initial access broker listings
- Exploit discussions
- Data trading forums
While not all dark web activity is criminal, it is heavily used for illicit transactions and data exchange.
The distinction between these layers matters when evaluating dark web vs deep web monitoring strategies.
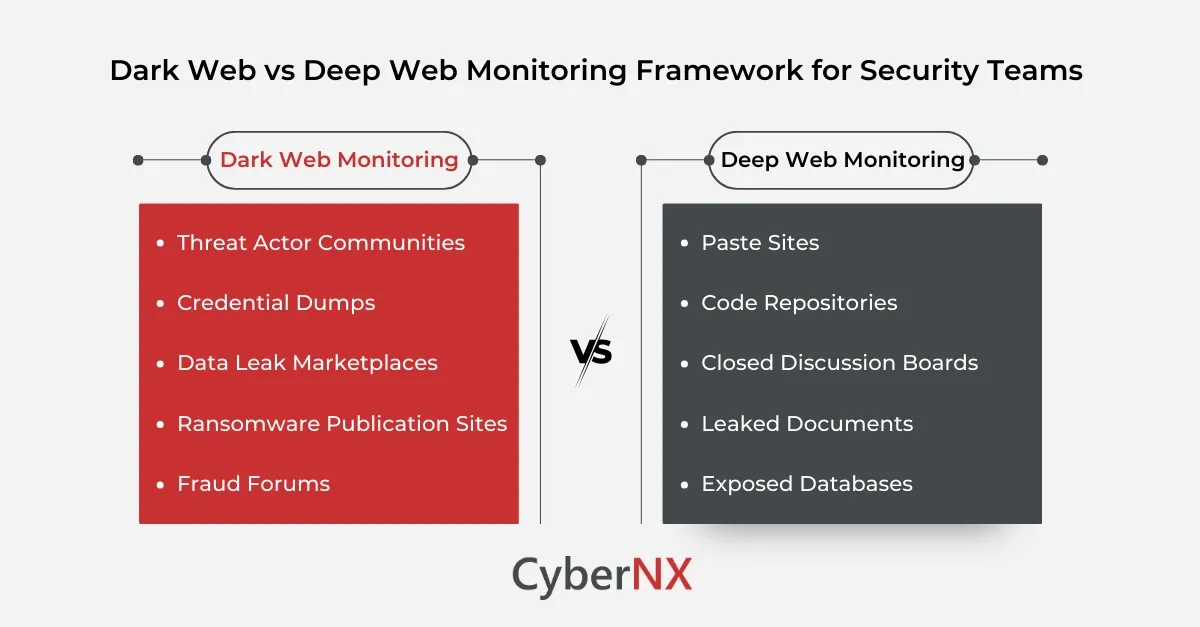
Dark web vs deep web monitoring: what’s the operational difference?
It’s important to understand that the monitoring approach, intelligence feeds, and risk implications differ a lot.
Dark web monitoring usually focuses on:
- Threat actor communities
- Credential dumps
- Data leak marketplaces
- Ransomware publication sites
- Fraud forums
Deep web monitoring focuses on:
- Paste sites
- Code repositories
- Closed discussion boards
- Leaked documents in semi-private portals/Leaked documents
- Exposed databases not indexed publicly/Exposed databases
When comparing dark web vs deep web monitoring, the former often provides high-risk intelligence signals, while the latter provides early-warning exposure detection.
Both are necessary for a complete digital risk posture.
Why security teams often misunderstand the difference
Many organisations purchase “dark web monitoring” solutions believing they cover all hidden internet exposure.
In reality:
- Dark web monitoring does not automatically cover deep web leaks.
- Deep web monitoring does not necessarily include threat actor forums.
- Surface web monitoring does not cover either layer comprehensively.
This misunderstanding leads to visibility gaps.
What security teams should monitor across both layers
Before selecting tools, define what matters most to your organisation.
Monitor for:
- Employee credential exposure
- Stolen customer data
- Leaked internal documents
- Compromised API keys
- Mentions of executive leadership
- Brand impersonation
- Third-party vendor breaches
A structured monitoring checklist reduces reactive incident handling.
How dark web monitoring supports incident response
Dark web intelligence is often reactive in nature.
It helps security teams:
- Identify leaked data
- Assess breach scope
- Monitor threat actor intent
- Validate ransomware claims
- Prioritize remediation
Dark web findings often confirm exposure after compromise.
How deep web monitoring supports proactive risk detection
Deep web monitoring is often preventive.
It helps detect:
- Early data exposure
- Misconfigured cloud storage
- Publicly accessible internal files
- Credential leaks before monetisation
- Brand misuse in early stages
In many cases, deep web monitoring identifies risks before they reach dark web marketplaces.
This proactive advantage is why security leaders must test both components.
Integrating dark web and deep web monitoring into enterprise security
A mature monitoring strategy should include:
- Continuous automated intelligence feeds
- API-driven threat ingestion into SOC workflows
- Multilingual threat intelligence coverage
- Executive exposure tracking
- Real-time alerting
- Incident response alignment
When evaluating dark web vs deep web monitoring, avoid treating them as competing services. They are complementary layers within digital risk protection.
Common mistakes in monitoring programs
Even advanced enterprises make errors.
- Relying only on keyword alerts: This produces noise and limited actionable intelligence.
- Failing to validate data authenticity: Not all leak claims are legitimate.
- Operating without escalation workflows: Intelligence without response is ineffective.
- Ignoring brand monitoring: Executive impersonation and phishing campaigns often originate in hidden layers.
A structured approach reduces these blind spots.
When should organisations implement both monitoring layers
Implement integrated monitoring when:
- Handling large volumes of customer data
- Operating in regulated industries
- Managing global workforce credentials
- Conducting digital commerce
- Expanding SaaS ecosystems
- Experiencing phishing or impersonation incidents
In 2026, hidden internet exposure is not a theoretical risk. It is a measurable operational threat.
Conclusion
The difference between dark web vs deep web monitoring is not technical trivia. It defines your visibility into hidden digital risk.
Deep web monitoring helps detect early exposure. Dark web monitoring helps detect harmful exploitation.
Together, they form a comprehensive digital risk intelligence framework.
Our advanced cyber services combine AI analytics, real-time alerts, global monitoring coverage, expert investigation, proactive detection and compliance-aligned reporting to protect enterprise brands and sensitive data across both deep and dark web layers.
If your organisation is evaluating how to strengthen its digital risk protection strategy, and you want to learn more about the dark web vs deep web monitoring services, connect with us to build an integrated monitoring program aligned to your security operations and executive risk priorities.
Dark Web vs Deep Web Monitoring FAQs
What is the main difference between dark web and deep web monitoring?
Dark web monitoring focuses on hidden threat actor communities and illicit marketplaces, while deep web monitoring focuses on non-indexed content like exposed databases and private portals.
Does dark web monitoring automatically cover deep web exposure?
No. The two layers require different intelligence sources and monitoring techniques.
Why do enterprises need both monitoring approaches?
Because data exposure may appear first in deep web sources and later be traded in dark web forums.
How should monitoring alerts integrate with SOC operations?
Alerts should feed directly into incident response workflows with severity-based escalation.
Is dark web monitoring enough to prevent brand damage?
No. Prevention requires combined monitoring, response workflows, and proactive digital risk protection controls.