Security leaders today face a structural shift. For years, traditional penetration testing focused on applications, infrastructure, APIs and networks. Now, AI systems are entering production environments – connected to enterprise data, internal tooling and decision workflows.
The problem? AI systems do not fail the same way traditional applications do.
This is where the discussion around AI penetration testing vs traditional pentesting becomes critical for organisations.
Let’s break down the real differences that matter.
What is traditional penetration testing?
Traditional penetration testing simulates how an attacker would exploit vulnerabilities in your IT environment. The focus is largely technical and deterministic.
A typical traditional pentest evaluates:
- Network misconfigurations
- Web application flaws such as SQL injection or XSS
- Authentication and authorization weaknesses
- API security gaps
- Cloud misconfigurations
- Privilege escalation paths
The attacker model is relatively clear. Exploit a technical flaw, escalate privileges, move laterally and exfiltrate data.
The logic is binary. Either a vulnerability exists, or it does not.
Traditional pentesting is mature, standardised and mapped to frameworks like OWASP Top 10, CVSS scoring and MITRE ATT&CK.
But AI systems introduce a fundamentally different class of risk.
What is AI penetration testing?
AI penetration testing evaluates how large language models, AI agents, retrieval systems and connected tools behave under adversarial conditions.
Unlike traditional systems, AI systems can be manipulated through language.
AI pentesting examines:
- Prompt injection and indirect prompt injection
- Jailbreak resilience and policy bypass
- RAG data poisoning and retrieval manipulation
- Sensitive data leakage from prompts, embeddings or logs
- Over-privileged agent tool execution
- Insecure output handling leading to downstream compromise
- Multi-stage abuse paths across AI and enterprise systems
The attack surface is not just code. It is behaviour.
This is the core shift in AI penetration testing vs traditional pentesting.
Infrastructure focus vs behavioural attack surface
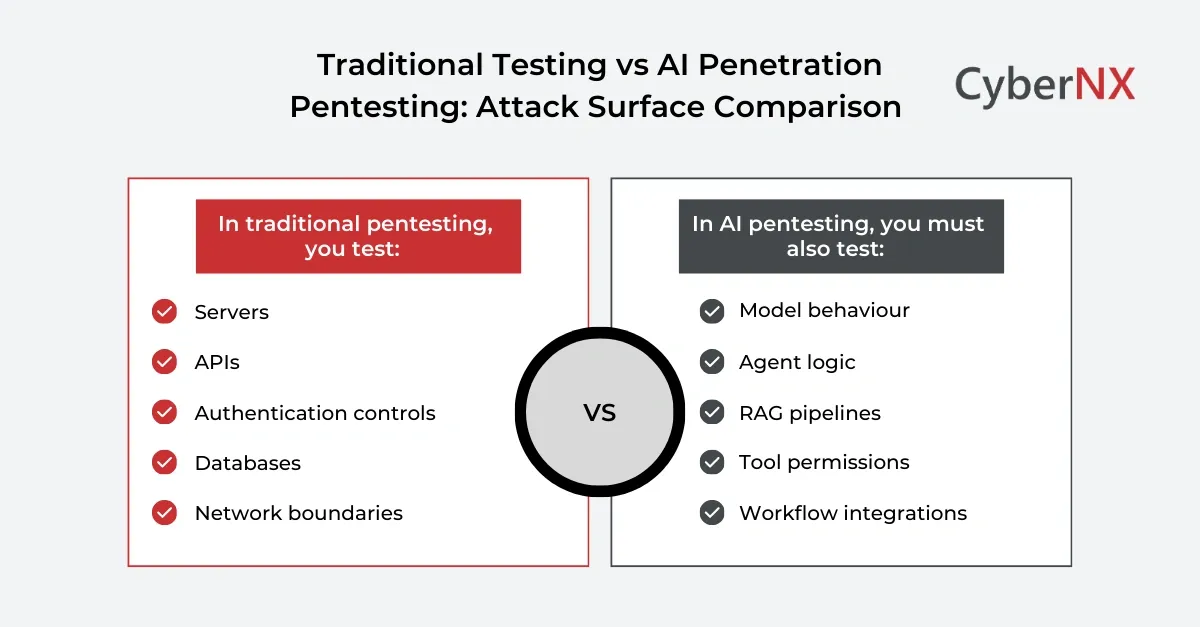
Traditional pentesting focuses mainly on infrastructure and application layers. AI systems expand the attack surface into behavioural and workflow layers.
In traditional environments, you test:
- Servers
- APIs
- Authentication controls
- Databases
- Network boundaries
In AI environments, you must also test:
- Model behaviour under adversarial prompts
- Agent decision-making logic
- RAG knowledge ingestion pipelines
- Tool permissions and execution boundaries
- Workflow integrations with enterprise systems
AI security extends beyond infrastructure into behaviour, context and decision execution.
Unlike traditional systems, an AI assistant integrated with CRM, cloud consoles, or ticketing systems can be manipulated into performing legitimate actions in unintended ways.
Deterministic systems vs probabilistic systems
Traditional applications are deterministic. The same input produces the same output.
AI systems are very probabilistic. Outputs change based on context, phrasing and hidden instructions.
This introduces three implications:
- Exploitability may not be consistently reproducible but still be real
- Security validation requires adversarial simulation at scale
- Risk scoring must incorporate behavioural uncertainty
In traditional pentesting, one successful exploit proves a vulnerability. In AI penetration testing, repeated adversarial testing validates resilience.
Testing methodology must adapt accordingly.
Tool exploitation vs tool abuse
In traditional environments, exploitation involves:
- Remote code execution
- Injection flaws
- Authentication bypass
- Privilege escalation
In AI environments, exploitation often involves tool abuse.
An AI agent connected to financial systems, IT automation scripts and HR workflows may execute legitimate tools in unintended ways if guardrails are weak.
The risk lies in:
- Over-privileged tool scopes
- Weak authorization boundaries
- Missing contextual validation
- Lack of monitoring for anomalous tool usage
This requires scenario-driven adversarial testing, not just vulnerability scanning.
Infrastructure compromise vs business workflow compromise
Traditional pentesting measures system compromise.
AI penetration testing measures business impact.
Consider the difference:
- Traditional scenario: An attacker exploits a vulnerable web server and gains database access.
- AI scenario: An attacker manipulates an AI agent to retrieve confidential financial projections from an internal knowledge base and email them externally without breaching infrastructure.
The infrastructure remains intact, but the business risk materialises. That distinction is key to understanding AI penetration testing vs traditional pentesting.
Compliance and board-level implications
Traditional pentesting supports compliance with:
- ISO 27001
- PCI-DSS
- SOC 2
- RBI cybersecurity guidelines
AI systems introduce additional governance scrutiny:
- Data protection obligations under DPDPA
- AI documentation and auditability requirements
- Evidence of adversarial resilience
- Control mapping to emerging AI frameworks
Boards are increasingly asking:
Have we validated that our AI systems cannot be manipulated into unsafe decisions? Traditional pentesting alone cannot answer that question.
Testing methodology differences
The execution model differs significantly between the two approaches.
Traditional pentesting involves:
- Scoping systems
- Automated scanning
- Manual exploitation
- Privilege escalation attempts
- Reporting and remediation
AI penetration testing requires:
- AI-specific threat modelling
- Prompt injection fuzzing
- RAG poisoning simulations
- Agent tool abuse scenarios
- Workflow manipulation testing
- Governance and logging validation
- Behavioural retesting after hardening
It combines technical exploitation with behavioural simulation and business logic abuse testing.
This demands cross-functional coordination across security, AI engineering, product and governance teams.
Where traditional pentesting still matters
AI penetration testing does not replace traditional VAPT.
You still need to validate:
- The application hosting the AI interface
- APIs and authentication layers
- Cloud configurations
- Data storage systems
AI pentesting extends coverage into behavioural risk domains. The most mature organisations integrate both into a unified offensive security program.
When should CISOs prioritise AI penetration testing
You should prioritise AI penetration testing when:
- Deploying AI chatbots that interact with customers
- Enabling RAG over sensitive internal knowledge bases
- Integrating AI agents with enterprise systems
- Automating financial or operational decisions
- Operating in regulated sectors
- Preparing for AI governance audits
If AI connects to decision workflows, your risk exposure increases significantly.
Conclusion
The discussion around AI penetration testing vs traditional pentesting is not about replacement. It is about evolution.
Traditional pentesting protects infrastructure, whereas AI penetration testing protects behaviour, workflows and decision integrity.
Organisations deploying AI at scale need structured AI security assessments, adversarial testing across model and agent layers and audit-ready reporting aligned to governance expectations.
Our deep expertise in penetration testing with cutting-edge knowledge of AI-specific attack vectors helps to provide advanced AI penetration testing services. We align AI security testing to India’s evolving governance and privacy expectations, plus global frameworks if you operate internationally.
If AI is entering your production environment, now is the time to validate how it behaves under pressure.
Connect with our team to understand the nuances in AI Penetration Testing vs Traditional Pentesting, initiate a structured AI security assessment and figure out your real AI exposure.
AI penetration testing vs traditional pentesting FAQs
What is the main difference between AI penetration testing and traditional pentesting?
Traditional pentesting focuses on technical vulnerabilities in infrastructure and applications. AI penetration testing evaluates behavioural manipulation, prompt injection, agent tool abuse and workflow compromise risks unique to AI systems.
Can traditional pentesting tools detect AI-specific vulnerabilities?
No. Traditional scanners are not designed to detect prompt injection, RAG poisoning or AI agent abuse paths. AI systems require specialised adversarial testing techniques.
Does AI penetration testing replace regular VAPT?
No. AI penetration testing complements traditional VAPT. Infrastructure and application security must still be validated.
How often should AI systems be tested?
Before production deployment, after major architecture changes, and periodically as integrations evolve.
Who should be involved in AI penetration testing engagements?
Security leaders, AI engineers, product stakeholders, compliance teams, and executive sponsors to make sure alignment with business risk.