The cybersecurity landscape is in constant flux, with cyberattacks growing in sophistication and frequency. We have moved beyond simple malware to face threats that adapt and evolve in real-time.
Artificial intelligence (AI), while offering incredible potential for defensive cybersecurity, is also being weaponised by malicious actors. This necessitates a new breed of defence: AI Penetration Testing.
This blog post will explore this crucial security mechanism and guide CISOs on navigating this new frontier.
The Changing Face of Cybersecurity
Cyberattacks are no longer simple smash-and-grab operations. They’re intricate, targeted and often leverage the very technologies we rely on.
AI plays a dual role in this landscape. While security teams are exploring AI-driven threat detection and response, attackers are also harnessing its power for more effective and evasive attacks.
This makes AI Penetration Testing, a proactive approach to identifying vulnerabilities in AI-powered systems and defences against AI-driven attacks, more critical than ever.
In 2026, it’s helpful to understand what “AI Penetration Testing” actually means – because the term covers two distinct activities:
- The first is using AI to do pentesting faster: automating reconnaissance, chaining vulnerabilities and accelerating report generation.
- The second is testing AI systems themselves: probing your LLMs, agents, and RAG pipelines for vulnerabilities like prompt injection, data leakage, and agent overreach.
Both of these matters to CISOs. The scale of AI adoption also reflects the urgency: according to a 2025 SANS Institute survey, 67% of red team operators now use at least one AI-assisted tool during active engagements compared to just 18% in 2023.
Understanding the Blend of AI and Penetration Testing
Let us demystify some key concepts about AI Pen testing here.
- Artificial Intelligence, in its simplest form, is about enabling computers to perform tasks that typically require human intelligence.
- Within AI, Machine Learning (ML) focuses on algorithms that allow computers to learn from data without explicit programming.
- Deep Learning (DL) uses complex neural networks to analyse vast amounts of data.
Traditional penetration testing involves simulating cyberattacks to identify vulnerabilities in systems and networks. However, traditional methods often struggle to keep pace with the speed and adaptability of AI-powered attacks.
This is where AI comes into play. AI is transforming penetration testing by automating tasks, enhancing analysis and simulating more realistic attack scenarios.
The Surging Demand for AI Penetration Testing
The rise of AI-powered attacks is a serious concern. Malicious actors are using AI for:
- Automated vulnerability discovery: AI can scan systems for weaknesses far faster and more comprehensively than humans.
- Adaptive malware: AI-powered malware can learn and adapt to security measures in real-time, making it harder to detect and neutralize.
- Social engineering attacks: AI can craft highly personalized and convincing phishing emails or social media scams.
- AI-targeted attacks on AI systems: Attackers now exploit the AI systems organisations deploy. They use prompt injection to hijack AI agents, poison knowledge bases connected to RAG systems, and abuse over-privileged tool-calling runtimes to take unauthorised actions.
Traditional security solutions and penetration testing methods, designed for more conventional attacks, are often ill-equipped to handle these AI-driven threats.
AI Pen testing offers a proactive defence, enabling organizations to identify and mitigate these vulnerabilities before they can be exploited, leading to a surge in its demand.
Read: Top 10 AI Pentesting Tools: Reviewed by Experts (2025)
AI Penetration Testing: A Deep Dive
AI Pen testing focuses on identifying vulnerabilities in AI-powered systems and defences against AI-driven attacks. It goes beyond traditional penetration testing by incorporating AI techniques to simulate and counter these advanced threats.
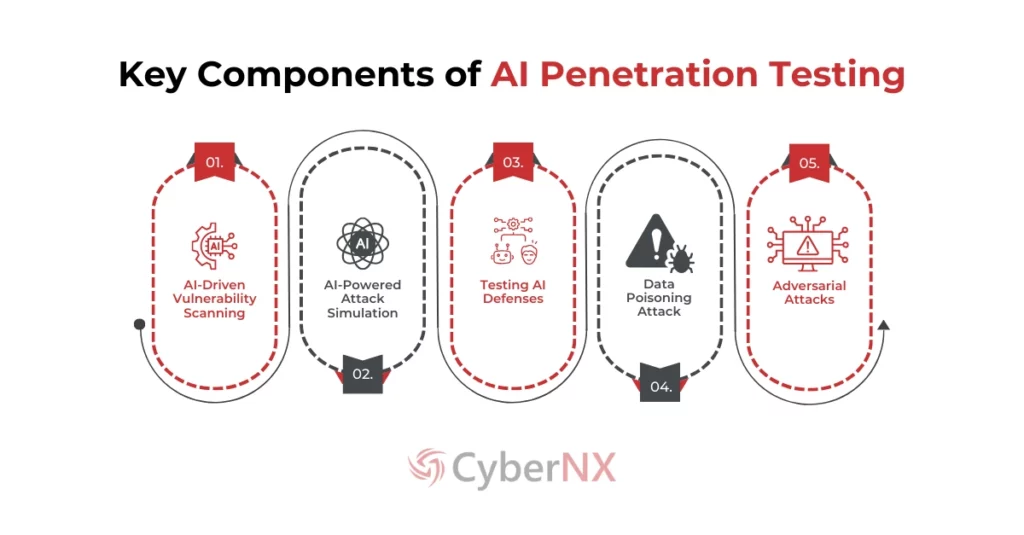
Key Components of an AI Penetration Test:
- AI-Driven Vulnerability Scanning: AI automates vulnerability scanning by identifying patterns and anomalies that traditional tools miss. This involves reasoning about an application’s behaviour and chaining vulnerabilities together rather than just matching known signatures.
- AI-Powered Attack Simulation: AI can simulate realistic attacks, including those that leverage AI techniques like adversarial attacks and data poisoning, providing valuable insights into an organization’s resilience.
- Testing AI Defences: AI Pentesting evaluates the effectiveness of existing AI-based security solutions, ensuring they can detect and respond to AI-driven threats.
- Data Poisoning Attacks: AI Pentesting assesses an organization’s vulnerability to data poisoning attacks, where malicious data is injected into training datasets to manipulate AI models.
- Adversarial Attacks: These attacks subtly manipulate input data to fool AI systems. AI Pentesting checks for robustness against such adversarial examples.
- Agentic AI and Tool Abuse Testing: AI agents with access to enterprise tools like ticketing, cloud consoles, CRM can be forced to take unauthorised actions. AI pentesting now explicitly tests agent permission boundaries, tool-calling runtimes, and MCP integrations for overreach and unsafe execution.
Benefits of AI Pentesting
All things said, what benefits does AI Pen testing offer to your business? Find the answer below:
- Enhanced Vulnerability Discovery: AI can uncover hidden vulnerabilities that might be missed by traditional methods.
- Proactive Risk Mitigation: Identifying and addressing vulnerabilities before they are exploited minimizes potential damage.
- Improved Security Posture: AI Pentesting strengthens the overall security posture of an organization.
- Regulatory Compliance: Specific frameworks now explicitly require adversarial AI security testing – the EU AI Act for high-risk AI systems, NIST AI RMF for governance and risk management, and India’s DPDPA for AI systems processing personal data. AI pentesting provides the audit-ready evidence these frameworks expect.
Conclusion: Embracing the Future of Cybersecurity
AI Penetration Testing is no longer a luxury but a necessity in today’s threat landscape. As organisations start using LLMs, AI agents, RAG systems, and MCP integrations across business workflows, the attack surface has expanded beyond what traditional testing was designed to cover.
CyberNX offers end-to-end AI penetration testing and red teaming across every layer of your AI stack – models, applications, RAG and knowledge systems, agent and tooling layers, and MCP integrations. Our three-phase method covers scope and threat modelling (1–2 weeks), hands-on AI pentest and red team exercises. Findings are mapped to OWASP LLM Top 10 (2025) and MITRE ATLAS, and compliance evidence is generated for DPDPA, EU AI Act, NIST AI RMF, and ISO 42001 as applicable.
Contact CyberNX Technologies – Your CERT-IN Empanelled Penetration Testing Partner today for a free consultation or security assessment. Let’s discuss your AI Penetration Testing needs.
FAQs
What is the difference between traditional penetration testing and AI pentesting?
Traditional pentesting relies on manual techniques and tools to identify vulnerabilities. AI penetration testing leverages artificial intelligence to automate tasks, enhance analysis, and simulate more realistic, AI-driven attacks. It specifically focuses on identifying weaknesses in AI systems and defences against AI-powered attacks.
Why is AI penetration testing necessary?
Traditional security measures often struggle to keep pace with the speed and sophistication of AI-powered attacks. AI pentesting provides a proactive approach to identify and mitigate vulnerabilities before they can be exploited by malicious actors using AI.
What types of vulnerabilities does AI penetration testing uncover?
AI pen test can uncover a range of vulnerabilities, including weaknesses in AI models, data poisoning vulnerabilities, susceptibility to adversarial attacks, and vulnerabilities in AI-based security systems themselves. It also assesses the effectiveness of your defences against AI-driven attack vectors.
What skills are required for AI pen testing?
AI pentesting requires a combination of cybersecurity expertise, knowledge of AI and machine learning, and familiarity with specialized tools and techniques. It’s best performed by experienced professionals with expertise in both areas.
How much does AI pen test cost?
The cost of an AI pen test varies depending on the scope and complexity of the assessment. Factors influencing the cost include the number of systems being tested, the depth of the analysis, and the expertise of the penetration testing team. Contact CyberNX for a tailored quote.
Can AI pentesting be automated entirely?
While AI can automate many aspects of penetration testing, human expertise remains crucial. Interpreting results, designing sophisticated attack simulations, and developing effective remediation strategies require human judgment and creativity. AI is a powerful tool to augment, not replace, human pen testers.