Previously, we covered the CrowdStrike MDR deployment guide and implementation checklist to help organisations plan their rollout. However, even with a structured approach, enterprises face real-world obstacles that slow progress or reduce impact. It can be hidden gaps in asset visibility, endpoint coverage, integration maturity and internal readiness.
In this blog, we explore the common challenges during CrowdStrike MDR implementation, including general and technical hurdles associated with deploying the CrowdStrike Falcon Complete platform. We also share practical insights to help CISOs and security leaders plan smarter.
Complexity behind CrowdStrike MDR deployment
Before diving into specific challenges, it is important to understand what the deployment involves. CrowdStrike MDR Falcon Complete is not just an endpoint tool. It is a fully managed service layered on top of the Falcon platform. It requires endpoint agents, policy configuration, API integrations, workflow alignment and clear escalation models.
Many enterprises underestimate this complexity.
1. Misaligned expectations between leadership & security teams
One of the most overlooked challenges is unrealistic expectations.
Leadership often expects instant visibility and immediate risk reduction. However, MDR platforms need tuning time. False positives must be reduced. Asset inventories must be reconciled. Policies must be optimised.
Without clear communication, this gap creates frustration. We often see CISOs under pressure to prove ROI within weeks. In reality, the first 30 to 60 days focus heavily on stabilisation and tuning.
Tip: Define success metrics early. Agree on measurable outcomes such as mean time to detect and mean time to respond rather than vague improvement goals.
2. Incomplete asset visibility before deployment
Another major factor is poor asset hygiene. If your CMDB is outdated or shadow IT is widespread, the Falcon agent rollout becomes uneven. Devices may remain unprotected. Servers might be missed. Remote assets could fall outside coverage.
This creates blind spots.
Many organisations struggle with accurate asset inventory, which directly impacts detection capability. You cannot protect what you cannot see.
Before deploying Falcon Complete, organisations must validate:
- Endpoint inventory accuracy
- Operating system compatibility
- Network segmentation mapping
Our experience shows that small improvements in asset management dramatically improve MDR outcomes.
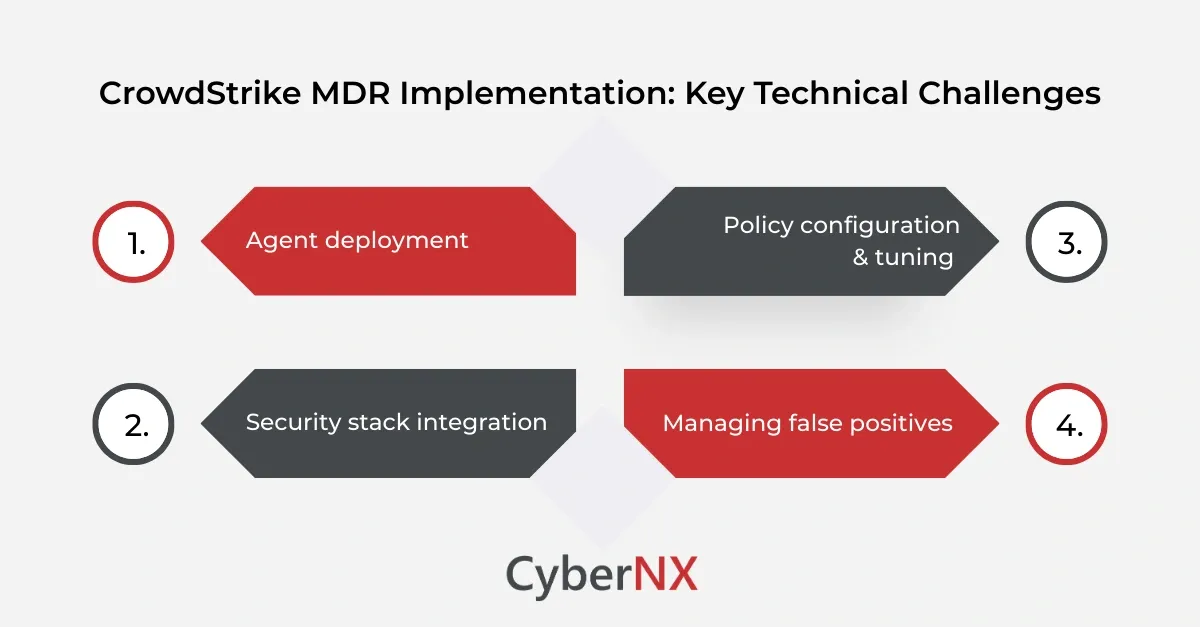
Core technical challenges during CrowdStrike MDR implementation
Technical depth matters here. Security teams often face specific engineering hurdles while rolling out the Falcon Complete platform.
1. Agent deployment
Agent rollout seems simple. It rarely is.
Large enterprises operate hybrid environments across cloud, on premise and remote endpoints. Deploying the Falcon sensor consistently across thousands of endpoints introduces friction.
Common issues include:
- Conflicts with legacy antivirus tools
- Bandwidth constraints in remote offices
- Endpoint performance concerns
- User resistance during deployment windows
If the agent is not deployed uniformly, detection gaps appear. That directly contributes weakens your security posture. A phased deployment plan with pilot groups often reduces risk. It allows performance testing before full rollout.
2. Security stack integration
Many CISOs assume CrowdStrike MDR will seamlessly integrate with existing SIEM, SOAR or ticketing systems. Integration is possible, but it demands planning.
Falcon APIs must be configured correctly. Log ingestion pipelines must be validated. Data mapping errors can cause alert duplication or loss of visibility.
Security teams frequently struggle with:
- Inconsistent log normalisation
- Alert fatigue due to duplicate alerts
- Workflow misalignment between MDR team and in-house SOC
These integration gaps represent one of the critical technical challenges during CrowdStrike MDR implementation. To mitigate this, define data flow architecture before enabling full alert streaming.
3. Policy configuration & tuning
Falcon Complete provides strong default policies. Yet enterprise environments differ widely. Overly aggressive prevention policies may disrupt legitimate applications. Overly permissive settings reduce protection.
Security teams must tune:
- Prevention policies
- Detection thresholds
- USB control and device policies
- Exclusion lists for business-critical applications
Policy misconfiguration leads to user complaints and business disruption. This can erode executive confidence early in the project. We recommend structured policy workshops before final enforcement. It avoids reactive firefighting later.
4. Managing false positives
During initial rollout, detection noise increases. That is normal.
However, without structured triage processes, security teams feel overwhelmed. One of the recurring challenges during implementation is balancing detection sensitivity with operational stability.
Even with Falcon Complete managing detection, internal teams must understand:
- Escalation thresholds
- Containment authorisation policies
- Communication channels during incidents
A clear RACI matrix helps reduce confusion.
Operational and governance challenges
Technical implementation is only part of the journey. Governance and operational maturity shape success.
1. Role clarity between internal SOC and MDR provider
Falcon Complete delivers managed detection and response. Yet internal teams remain accountable for risk.
One of the significant challenges is unclear ownership. Who authorises containment? Who communicates to business leaders? Who handles forensic follow-up?
Without defined playbooks, response slows down. We advise clients to document:
- Escalation procedures
- Containment approval flows
- Communication protocols
- Post-incident review process
Clarity removes friction during live incidents.
2. Compliance and data residency considerations
Global enterprises must consider regulatory constraints.
Falcon platform data storage and telemetry transfer may raise questions for organisations operating under GDPR or region-specific regulations.
Security leaders should verify:
- Data storage regions
- Retention policies
- Cross-border data transfer implications
Ignoring these details becomes one of the regulatory challenges, especially in financial services and healthcare sectors.
3. Change management and cultural resistance
Technology adoption always triggers behavioural friction.
Employees may resist endpoint changes. IT teams may feel threatened by managed services. Internal SOC analysts might worry about role displacement. Change management is often underestimated. Yet it strongly influences implementation success. Leadership must communicate that MDR enhances internal capability rather than replacing it. Collaboration builds trust.
How to reduce risk during CrowdStrike MDR implementation
To successfully navigate the common challenges during CrowdStrike MDR implementation, organisations should:
- Conduct a pre-deployment readiness assessment
- Clean and validate asset inventory
- Pilot deployment with controlled endpoint groups
- Align integration architecture with existing tools
- Establish clear incident response governance
- Define measurable success metrics
At CyberNX, we work alongside your team to map these elements before activation. Our experience shows that proactive alignment shortens stabilisation time and accelerates value.
Conclusion
CrowdStrike MDR implementation challenges are rarely caused by the technology itself. They stem from gaps in planning, integration, asset visibility and governance clarity. When organisations approach Falcon Complete as a strategic transformation rather than a simple tool deployment, outcomes improve dramatically.
If you are preparing for a CrowdStrike MDR rollout or facing friction in your current deployment, we can help. As a CrowdStrike services partners, we provide CrowdStrike consulting which will help you with a structured readiness assessments, integration planning and post-deployment optimisation. Speak with our experts and ensure your MDR investment delivers measurable security improvement.
Common challenges during CrowdStrike MDR implementation FAQs
How long does CrowdStrike MDR implementation typically take?
Implementation timelines vary based on environment size and complexity. Mid-sized enterprises may complete deployment within four to eight weeks, including stabilisation and tuning.
Does CrowdStrike Falcon Complete replace an internal SOC?
No. Falcon Complete complements internal teams. It reduces detection and triage workload while internal teams retain strategic control and governance responsibility.
What prerequisites are required before deploying CrowdStrike MDR?
Organisations should ensure accurate endpoint inventory, network architecture visibility, defined incident response workflows and executive alignment on containment authority.
Can CrowdStrike MDR support hybrid and multi-cloud environments?
Yes. The Falcon platform supports endpoints across on premise, cloud and remote environments. However, integration planning is required for complete visibility and workflow alignment.