Stolen credentials sit at the centre of most major breaches, and they are cheap to buy, easy to use, and difficult to trace. Many security leaders invest heavily in perimeter controls, endpoint tools, and identity platforms. Yet attackers often walk in through the front door using valid usernames and passwords. That is the uncomfortable truth.
We have seen organisations with mature controls still fall victim to credential abuse. The difference often lies in visibility. Specifically, visibility into where their credentials surface outside the corporate network.
In this blog, we unpack how dark web monitoring helps detect stolen credentials early and respond accordingly.
The rising value of stolen credentials
Stolen credentials are the backbone of modern cybercrime. Attackers no longer need complex exploits when they can simply log in. Credentials are harvested from multiple sources such as data breaches, phishing campaigns, malware such as infostealers and even third-party vendors.
Once collected, these credentials are traded openly across underground forums and marketplaces.
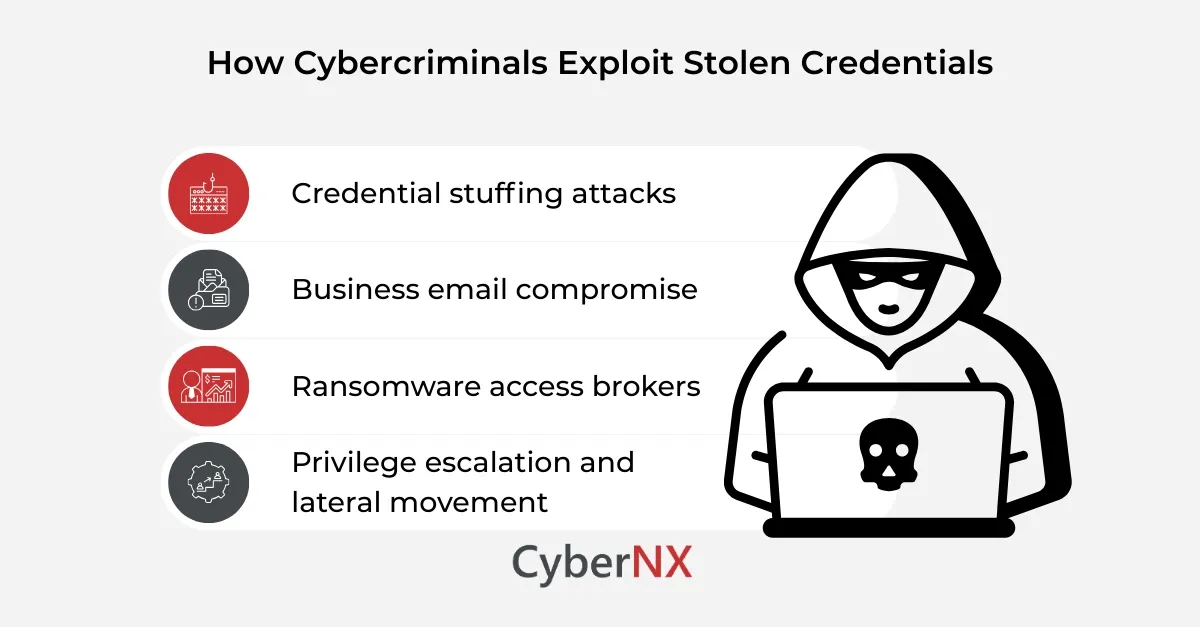
1. Credential stuffing attacks
Attackers use automated tools to test stolen usernames and passwords across multiple platforms. This is known as credential stuffing. Many users reuse passwords across personal and corporate accounts. A breach on a retail site can therefore expose access to corporate email or cloud applications. A single reused password can unlock sensitive systems.
2. Business email compromise
Stolen credentials are frequently used for business email compromise attacks. Once inside an email account, attackers monitor conversations. They study payment cycles. Then they strike. Fake invoices are sent. Payment details are changed. Finance teams act in good faith. The result can be significant financial loss within hours.
3. Ransomware access brokers
Ransomware groups increasingly rely on access brokers. These brokers specialise in gaining and selling access to corporate networks.
Valid credentials for VPN, RDP, or SaaS platforms are sold to the highest bidder. The ransomware operator then deploys encryption payloads. This model has lowered the technical barrier for large scale attacks.
4. Privilege escalation and lateral movement
Even low privilege credentials have value. Attackers use them as a foothold. From there, they escalate privileges, move laterally, and identify crown jewels. What begins as a simple login can end in full domain compromise.
Why traditional controls often miss early signals
Most organisations focus primarily on monitoring activity within their own IT environment using tools such as SIEM alerts, identity and access logs, and endpoint detection systems. This means they often detect threats only after suspicious behaviour occurs internally rather than identifying risks that emerge outside their perimeter.
These are critical. However, they only detect activity once an attacker attempts to use the credentials internally. By that stage, the damage may already be underway. The real early warning sign appears outside the organisation. It appears when credentials are listed, shared, or sold in underground communities. Without visibility into those spaces, organisations operate with a blind spot.
How dark web monitoring is the saviour
Dark web monitoring refers to the continuous scanning of underground forums, marketplaces, paste sites, and closed communities to identify exposed organisational data. This includes employee email addresses, usernames, passwords, API keys, and other sensitive information.
The aim is simple. Detect exposure before attackers exploit it.
1. Continuous intelligence gathering
Dark web monitoring tools collect data from multiple hidden sources. These include Tor based forums, encrypted messaging channels, and breach dumps. Advanced services use both automated crawling and human analysts. This hybrid approach improves accuracy and reduces false positives.
2. Correlation with organisational assets
Raw data alone is not useful. Effective monitoring correlates discovered credentials with the organisation’s domain names, executive accounts, privileged users, and critical applications. This context allows security teams to prioritise high risk exposures.
3. Real time alerts and validation
When credentials are identified, alerts are generated quickly. However, mature services also validate findings. They check whether credentials appear authentic, recent, and relevant. This avoids unnecessary panic. The goal is actionable intelligence, not noise.
How early detection changes the game
Early detection creates options. And options reduce impact.
1. Forced password resets
If exposed credentials are detected quickly, organisations can enforce password resets before attackers attempt access. This small step can break the attack chain.
2. MFA enforcement and policy review
Exposure often reveals patterns. For example, executives without multi factor authentication enabled. Security leaders can use these insights to strengthen identity controls across high-risk accounts.
3. Threat hunting and anomaly detection
When credentials appear on underground forums, security teams can proactively hunt for suspicious login attempts. Instead of reacting to an incident, teams shift into preventive mode.
4. Third party risk visibility
Many breaches originate from suppliers. Dark web monitoring can reveal whether a vendor’s compromised credentials are circulating. This insight supports stronger third-party risk management discussions.
Building an effective dark web monitoring programme
Technology alone is not enough. Organisations need clear processes for validation, escalation, and remediation. Alerts must translate into defined actions. Security teams should also:
- Regularly review privileged and high-risk accounts
- Enforce strong password and MFA policies
- Integrate monitoring outputs with SOC workflows
- Conduct tabletop exercises based on credential exposure scenarios
Most importantly, leadership must recognise that identity is the new perimeter. When credentials are compromised, the perimeter dissolves.
Conclusion
Stolen credentials remain one of the simplest and most effective attack vectors. Attackers exploit trust in identity systems rather than breaking through technical defences.
Dark web monitoring provides early visibility into that hidden threat landscape. It allows organisations to act before access is abused, before ransomware spreads, and before reputational damage escalates.
We work closely with security leaders to embed threat intelligence, identity protection, and continuous monitoring into daily operations. If you want to reduce credential-based risk and gain early warning against underground exposure, our team is ready to support you.
Speak to our experts to know about our dark web monitoring services and how to strengthen your visibility beyond the perimeter.
FAQs
How often should organisations review dark web monitoring alerts?
Alerts should be reviewed in real time or at least daily. Rapid response is critical to prevent credential misuse.
Does dark web monitoring replace identity and access management tools?
No. It complements IAM systems by identifying external exposure, while IAM controls internal access governance.
Can dark web monitoring detect insider threats?
Indirectly, yes. If insider credentials are leaked or shared externally, monitoring can reveal unusual exposure patterns.
What types of data beyond passwords can be detected on the dark web?
Monitoring can identify API keys, database dumps, personal data, intellectual property references, and confidential documents.