Cyber threats move fast. Security teams often do not. Attackers automate their campaigns, blend into normal traffic, and exploit gaps before most organisations can react. According to IBM Cost of a Data Breach Report 2023, the average time to identify and contain a breach was 277 days. That is almost nine months of hidden risk.
In this blog, part of our CrowdStrike MDR blog series, we explore How CrowdStrike MDR Handles Incident Detection and Response and what it means for modern enterprises. We will break down how detection works, how response is executed, and how organisations can reduce dwell time with a managed approach.
Why incident detection and response struggle is real
Incident detection and response sound simple. Spot the threat, stop the threat and in the end fix the damage. But in reality, it is layered and complex.
Security teams face three main challenges.
- First, alert overload. Modern tools generate thousands of alerts each day. Many are false positives. Teams waste time chasing noise.
- Second, skills shortage. Experienced analysts are hard to hire and retain. According to ISC2, the global cybersecurity workforce gap remains in the millions.
- Third, attacker sophistication. Threat actors use fileless malware, living off the land techniques, and stolen credentials. They look like normal users.
The result is slow detection and fragmented response. This is where managed detection and response becomes critical.
Why CrowdStrike MDR is a game changer for busy teams
CrowdStrike offers Managed Detection and Response as part of its Falcon platform. The service combines advanced endpoint telemetry, threat intelligence, and a 24/7 expert team. At its core, CrowdStrike MDR monitors, investigates, and responds to threats across endpoints, cloud workloads, and identities. It does not just raise alerts. It acts.
Let us break down how this works in practice.
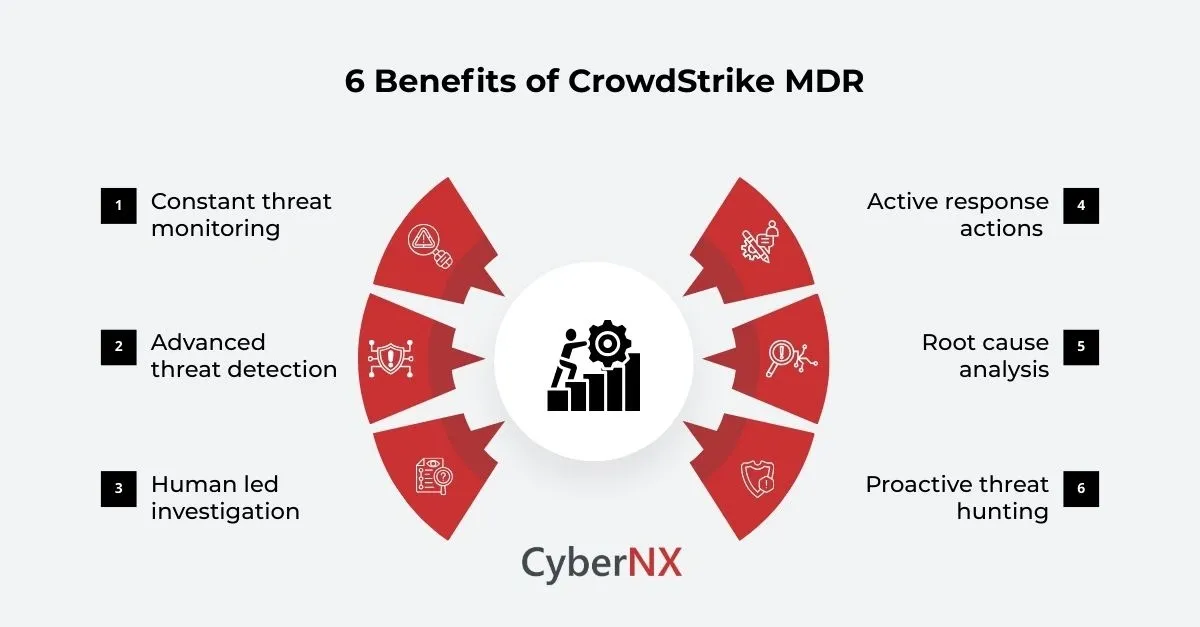
1. Continuous threat monitoring and telemetry collection/Constant threat monitoring
Effective incident detection starts with visibility. Without deep telemetry, detection is guesswork.
CrowdStrike MDR uses lightweight agents deployed across endpoints. These agents collect behavioural data in real time. Instead of relying only on signatures, they monitor process activity, memory usage, registry changes, network connections, and user behaviour.
This behavioural approach allows detection of:
- Fileless malware
- Credential misuse
- Lateral movement
- Command and control communication
All telemetry feeds into the Falcon platform, where it is analysed using machine learning models and threat intelligence.
The result is broad visibility across the attack surface. That visibility is the foundation of strong incident detection and response.
2. Advanced threat detection using intelligence and analytics/ Advanced threat detection
Detection is not about generating more alerts. It is about generating the right ones.
CrowdStrike MDR combines:
- Behavioural analytics
- Indicators of attack
- Global threat intelligence
- Human threat hunting
The Falcon platform uses real time analytics to identify suspicious patterns. At the same time, CrowdStrike’s global threat intelligence team tracks adversaries worldwide.
This intelligence is constantly updated. It includes tactics, techniques, and procedures mapped to the MITRE ATT and CK framework.
When suspicious behaviour matches known attack patterns, alerts are escalated for investigation. This reduces noise and focuses on real threats.
Gartner notes that MDR services help organisations detect threats that internal teams often miss due to limited context or bandwidth. That external perspective is powerful.
3. Human led investigation and validation/Human led investigation
Automation accelerates detection. Humans validate and contextualise it.
CrowdStrike MDR analysts investigate escalated alerts in depth. They review endpoint activity, correlate related events, and determine the scope of impact.
This stage answers key questions:
- Is this a true incident or benign behaviour?
- How far has the attacker moved?
- What assets are affected?
- Is data at risk?
The goal is clarity. Decision makers need accurate information, not raw logs.
Our experience shows that small improvements in validation reduce panic and improve response quality. When executives receive precise impact analysis, they can act decisively.
4. Active containment and response actions/Active response actions
Detection without action is incomplete.
Once an incident is confirmed, CrowdStrike MDR can execute response measures. These may include:
- Isolating compromised endpoints from the network
- Killing malicious processes
- Removing persistence mechanisms
- Blocking malicious hashes and domains
Endpoint isolation is especially powerful. It prevents lateral movement while allowing forensic investigation to continue.
In severe cases such as ransomware, rapid containment can stop encryption from spreading across the network.
This is how CrowdStrike MDR handles incident detection and response in a coordinated way. Detection flows directly into containment, without long internal approval chains.
5. Root cause analysis and remediation guidance/Root cause analysis
Stopping the attack is only part of the story.
After containment, CrowdStrike MDR provides detailed reporting and root cause analysis. This includes:
- Initial entry point
- Attack timeline
- Tools used by the adversary
- Impacted systems
- Recommended remediation steps
This level of insight helps organisations close gaps. It also supports compliance and board level reporting.
According to the UK National Cyber Security Centre, effective incident response must include lessons learned and system improvements. Without that, the same weakness may be exploited again.
We often advise clients to treat each incident as a maturity checkpoint. If you do this well, security posture improves steadily.
6. Proactive threat hunting
Beyond reactive detection, CrowdStrike MDR includes proactive threat hunting.
Threat hunters search for hidden adversaries who may have bypassed automated controls. They use hypothesis driven techniques based on emerging intelligence.
This proactive layer reduces dwell time significantly. The difference is subtle but important. Traditional monitoring waits for alerts. Threat hunting assumes compromise and looks for weak signals. That mindset shift strengthens incident detection and response capabilities across the organisation.
How CrowdStrike MDR reduces business risk
Let us connect this to business impact.
Effective incident detection and response leads to:
- Reduced dwell time
- Lower financial impact
- Faster operational recovery
- Stronger regulatory compliance
- Improved stakeholder confidence
IBM’s research shows that organisations with mature detection and response capabilities reduce breach costs by millions compared to those without.
For CISOs and CXOs, this is not only a technical advantage. It is a governance advantage.
When boards ask, “How quickly can we detect and contain an attack?” you need a confident answer.
Where CyberNX fits in
Technology alone does not solve security challenges. Integration, alignment, and optimisation matter just as much.
At CyberNX, we work closely with organisations implementing CrowdStrike MDR. We assess existing controls, align detection rules with business risk, and ensure incident response playbooks reflect real operational priorities.
We also help clients:
- Integrate MDR with SIEM and SOAR platforms
- Define escalation workflows
- Conduct tabletop exercises
- Strengthen identity and cloud monitoring
Our approach is practical and collaborative. We strengthen your internal team while leveraging CrowdStrike’s global expertise.
Conclusion
Understanding how CrowdStrike MDR handles incident detection and response helps organisations see beyond marketing claims. It is about continuous monitoring, intelligent detection, expert validation, rapid containment, and long-term improvement.
When these elements work together, dwell time drops and confidence rises.
If you want to strengthen your detection and response strategy, we can help. At CyberNX, we guide you through evaluation, deployment, and optimisation of CrowdStrike Falcon platform, so your security operations become faster, sharper, and more resilient.
Connect with us for CrowdStrike consulting services and explore how we can elevate your security program.
FAQs on How CrowdStrike MDR Handles Incident Detection and Response
How does CrowdStrike MDR differ from traditional SOC services?
CrowdStrike MDR combines advanced endpoint telemetry, global threat intelligence, and active response capabilities. Traditional SOC models often focus on alert monitoring without direct containment authority.
Can CrowdStrike MDR support hybrid and multi cloud environments?
Yes. CrowdStrike MDR extends visibility across endpoints, cloud workloads, and identities, making it suitable for hybrid and distributed infrastructures.
How quickly can incidents be contained using CrowdStrike MDR?
Containment time depends on the attack type and environment complexity. However, automated isolation and 24 by 7 monitoring significantly reduce response time compared to manual internal processes.
Is CrowdStrike MDR suitable for organisations with existing security teams?
Absolutely. Many enterprises use CrowdStrike MDR to augment internal SOC teams, reduce alert fatigue, and strengthen advanced threat hunting capabilities.