The economy is digitised today. Businesses launch customer portals, mobile apps, SaaS tools, APIs, cloud workloads, and partner integrations. Employees work from anywhere. Critical data and brand assets live far beyond the corporate firewall. This change explains why Digital Risk Protection (DRP) matters.
It wasn’t so a decade and a half ago.
the early days of enterprise IT, most information lived inside the corporate network. Naturally, information security focused on building strong perimeters. Firewalls, endpoint controls, and SIEM platforms were enough because threats came from outside and attacks tried to break in.
But as soon as businesses moved beyond network, threats followed this shift. Attackers now exploit fake domains, leaked credentials, impersonated executives, exposed cloud storage, counterfeit apps, and stolen brand assets. Many never touch a vulnerability. They simply log in using valid credentials purchased on underground markets.
To counter this, digital risk protection focuses on identifying, reducing, and mitigating risks that exist outside the organisation’s internal environment, before they cause financial, operational, or reputational damage.
What is digital risk protection?
Digital risk protection is like a radar which continuously identifies and handles cyber risks that could emerge from an organisation’s external digital presence.
Rather than monitoring internal systems alone, digital risk protection looks outward across the internet. It focuses on where attackers plan, trade, and prepare attacks long before any alert appears inside the network.
Digital risk protection typically addresses risks such as:
- Exposed or stolen credentials
- Brand impersonation and phishing infrastructure
- Data leaks and ransomware extortion activity
- Shadow IT and unknown digital assets
- Third-party and supply chain compromise
The primary objective is early visibility. The earlier a risk is detected, the easier it is to contain.
What is DRP security and how does it work?
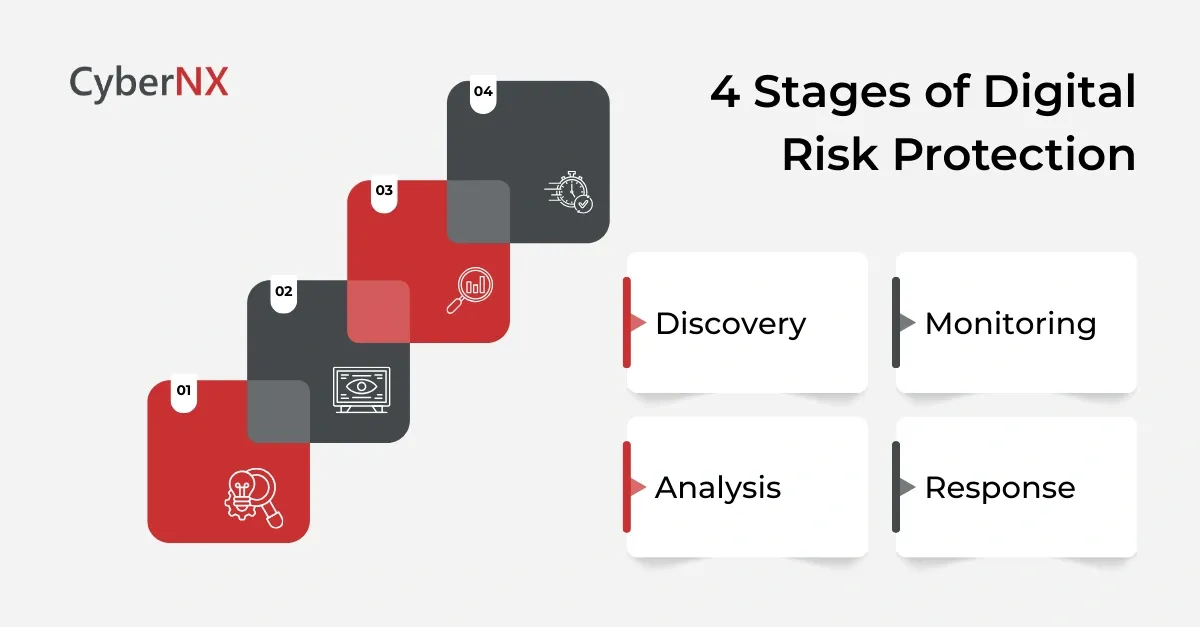
DRP security refers to the technologies, platforms, and managed services used to operationalise digital risk protection. Most DRP security programmes follow a continuous four-stage cycle.
1. Discovery
This stage maps the organisation’s full external footprint, including:
- Domains and subdomains
- Cloud assets and exposed services
- Mobile apps and APIs
- Third-party and vendor-linked assets
Many organisations uncover forgotten or unmanaged assets during this phase.
2. Monitoring
Once assets are identified, DRP security tools monitor external sources continuously, such as:
- Dark web marketplaces and forums
- Ransomware leak sites
- Stealer log repositories
- Paste sites and underground channels
- Certificate transparency logs and new domain registrations
3. Analysis
Not all alerts matter. DRP security validates exposed data, checks freshness, and prioritises threats based on real business impact.
4. Response
Response actions may include:
- Forced password resets
- Fraudulent domain and content takedowns
- Blocking malicious indicators
- Escalation to SOC or identity teams
Automation plays a key role in reducing response time.
Dark web monitoring as a core pillar of DRP
Dark web monitoring is one of the most critical components of digital risk protection.
Most credential theft, data trading, and attack planning happens outside the open internet. Attackers sell access, share stealer logs, and discuss targets in underground communities long before an incident occurs.
Dark web monitoring within DRP security focuses on:
- Stolen employee and customer credentials
- Stealer malware logs tied to corporate domains
- Mentions of the organisation on hacker forums
- Data dumps linked to breached vendors
- Ransomware groups advertising stolen data
By detecting compromised credentials early, organisations can reset access before attackers log in, stopping account takeover attempts before they begin.
Brand risk monitoring and impersonation detection
Brand abuse has become a preferred attack method because it targets trust.
Brand risk monitoring within digital risk protection identifies misuse of an organisation’s identity across the digital ecosystem.
This includes monitoring for:
- Typo squatting and lookalike domains
- Fake websites and landing pages
- Malicious mobile apps using brand assets
- Fraudulent social media profiles
- Unauthorised use of logos, trademarks, and executive identities
Phishing domain monitoring is especially valuable. By tracking new domain registrations and SSL certificate issuance, DRP security can detect phishing infrastructure before campaigns launch.
Takedown capabilities ensure these threats are removed quickly, limiting customer exposure and reputational damage.
Threat intelligence and external visibility
Threat intelligence within DRP security is highly contextual.
Rather than consuming generic feeds, DRP security generates intelligence specific to the organisation’s digital footprint.
This intelligence helps teams understand:
- Who is targeting the organisation
- Which credentials or assets are exposed
- How threat actors operate and monetise access
- Where attacks are likely to surface next
This external intelligence complements internal telemetry from SIEM and SOC tools, providing a more complete view of risk.
There are myriad ways in which digital risk protection helps businesses. We will now look at those in the next section.
Managing stakeholder-specific risks with DRP
Digital risks rarely impact just one team. They cut across leadership, legal, finance, HR, and operations. This is why digital risk protection delivers value far beyond the security function.
1. Leadership
Executives and board members are increasingly targeted because of their authority and public visibility. Attackers impersonate CEOs, CFOs, and business heads to authorise fraudulent payments or extract sensitive information. DRP security helps protect executives by monitoring for leaked personal data, impersonated social profiles, fake email domains, and deepfake-enabled fraud attempts. Early detection reduces the risk of high-impact business email compromise incidents.
2. Legal/Compliance
Legal and compliance teams rely on DRP security for early breach intelligence. When sensitive data appears on ransomware leak sites or underground forums, DRP tools help confirm whether the organisation is affected. This supports faster regulatory decision-making, accurate disclosures, and evidence collection for litigation or cyber insurance claims. It also reduces the risk of fines linked to delayed reporting.
3. Finance
Finance teams benefit from monitoring for stolen payment data, fraudulent marketplaces, and brand abuse tied to financial scams. DRP security enables early intervention before losses escalate.
HR and people teams increasingly use DRP insights to detect employee credential exposure, insider threats, or misuse of access following layoffs or role changes. By aligning DRP insights with stakeholder priorities, organisations move from reactive response to proactive risk management across the business.
Supporting digital transformation and cloud adoption
DRP is non-negotiable for businesses pursuing digital transformation and new technologies like cloud.
1. Digitisation
Digital transformation accelerates innovation, but it also expands exposure. Every new cloud workload, SaaS platform, API, and integration increases the number of assets attackers can target.
Digital risk protection helps organisations regain visibility as environments become more distributed. DRP security identifies exposed cloud storage, misconfigured services, leaked access keys, and forgotten assets tied to legacy projects or temporary initiatives. These exposures often sit outside traditional vulnerability scans and remain unnoticed until exploited.
2. Cloud
Cloud identity is another growing risk area. Attackers increasingly target cloud credentials rather than infrastructure flaws. DRP security detects stolen cloud and SaaS credentials on underground markets and stealer logs, allowing teams to revoke access before misuse occurs.
3. Hybrid Work
Hybrid work has added a human layer to digital transformation risks. Impersonated executives, fake collaboration invites, and urgent payment requests are now common. DRP security detects the infrastructure and identity abuse that enables these attacks, rather than relying solely on email filtering.
As organisations modernise, DRP acts as a safety net. It provides continuous external validation that digital growth has not created unseen entry points. This visibility enables teams to innovate confidently, knowing that risks beyond the firewall are actively monitored and reduced.
Mitigating third-party and supply chain risk
Third-party risk has become one of the most unpredictable sources of exposure. Even organisations with strong internal controls can be compromised through vendors, partners, or service providers.
Digital risk protection strengthens supply chain resilience by monitoring beyond contractual boundaries. DRP security tracks ransomware leak sites and underground forums for signs that vendors have been breached. Instead of waiting for vendor disclosures, organisations gain early warning when data begins circulating externally.
Advanced DRP tools allow teams to search within leaked datasets to confirm whether their specific information has been exposed. This avoids overreaction while enabling targeted response when real exposure exists.
Supply Chain Risk
Software supply chains present another risk vector. Compromised developer accounts, poisoned open-source repositories, and malicious updates have become common attack methods. DRP security identifies malware-laden code, suspicious repository activity, and leaked credentials linked to developers before these risks enter production environments.
Supply chain monitoring also supports procurement and vendor risk teams. By combining DRP insights with vendor assessments, organisations can prioritise remediation, renegotiate controls, or disengage from high-risk partners.
Ultimately, DRP security reduces blind trust in the supply chain and replaces it with continuous, evidence-based risk awareness.
DRP tools: what capabilities matter most
Not all DRP tools deliver the same value. The most effective platforms focus on depth, accuracy, and actionability.
- Digital footprint discovery and asset mapping
- Dark web and stealer log monitoring
- Brand and phishing detection
- Data leak and ransomware monitoring
- Automated takedowns and remediation
- Integration with identity, SOC, and response workflows
Some organisations adopt point solutions, while others prefer unified DRP platforms or managed services.
How to find the right DRP vendors
Selecting a DRP vendor requires more than comparing feature lists. The real differentiator lies in coverage, accuracy, and execution.
- Depth of dark web and credential monitoring: Start by evaluating visibility. Ask how deep the vendor’s dark web access goes, how quickly they ingest new data, and how they validate exposed credentials.
- Accuracy and relevance of alerts: Assess alert quality. High volumes mean little if relevance is low. Strong vendors prioritise risks based on business impact and context.
- Speed and effectiveness of takedowns: Takedown capability is essential. Understand how quickly the vendor can remove fraudulent domains, fake profiles, and malicious content, and whether this process is automated or manual.
- Availability of managed services and analyst support: Consider service models. Some organisations prefer self-service platforms, while others benefit from managed DRP services with analyst support.
- Tool Integration: Integration should not be an afterthought. Vendors must fit into existing SOC, identity, and response workflows.
- Transparency: Finally, evaluate transparency. Vendors should clearly explain data sources, monitoring scope, and limitations.
The right DRP vendor acts as an extension of your team, not just a dashboard. The goal is reduced risk, not more alerts.
What is new in digital risk protection in 2026
By 2026, digital risk protection has moved from niche capability to core security function.
- Credential Intelligence: One of the most significant changes is the speed of intelligence. Credential theft data from stealer malware is now ingested and analysed in near real time. This allows organisations to invalidate access within hours, often before attackers act.
- Signal quality: Signal quality has improved dramatically. AI-assisted validation now focuses on business relevance rather than volume. DRP security prioritises risks tied to privileged access, sensitive systems, and brand exposure, reducing alert fatigue.
- Takedowns: Automated takedowns have expanded through direct integrations with registrars, hosting providers, and social platforms. Fraudulent assets can be removed faster and at greater scale.
- Identity protection: Executive protection has grown as deepfake technology matures. DRP security now includes monitoring for voice, video, and identity misuse targeting senior leaders.
- Tech integration: Integration has also improved. In 2026, DRP is embedded into SOC workflows, identity platforms, and response automation. External risk intelligence now triggers internal controls automatically.
Most importantly, DRP is measured by outcomes. Reduced account takeover, faster remediation, and lower fraud losses now define success, not alert counts.
Conclusion
Digital risk protection addresses a reality that traditional security models can no longer ignore. Many of today’s most damaging threats from outside the network, long before internal controls see them.
DRP security gives organisations the visibility to detect external risks early, respond faster, protect their brand, and reduce financial and operational impact.
At CyberNX, we work with your internal team to identify external threats early and reduce real-world risk. If you want to understand where your digital exposure truly lies, now is the right time to start the conversation. Connect with us to know what we offer with our Digital Risk Protection services.
Digital Risk Protection FAQs
How does digital risk protection support incident response after a breach?
Digital risk protection helps incident response teams understand what data is circulating externally after a breach. By tracking how stolen information is shared, sold, or repackaged, teams can assess real-world impact, prioritise remediation, and communicate accurately with regulators, customers, and partners.
Can digital risk protection help measure cyber risk exposure over time?
Yes. DRP programmes provide trend-based insights that show whether external exposure is increasing or decreasing. Metrics such as credential leak frequency, brand abuse volume, and takedown response times help leadership quantify risk reduction and security ROI.
How does digital risk protection differ from attack surface management?
Attack surface management focuses on identifying exposed assets and vulnerabilities. Digital risk protection goes further by monitoring criminal activity, identity abuse, and data misuse related to those assets, providing insight into how attackers actually exploit exposure.
What internal teams should be involved in a DRP programme beyond security?
Effective DRP programmes involve legal, compliance, communications, HR, and finance teams. External risks often impact brand reputation, regulatory obligations, employee safety, and financial operations, making cross-functional collaboration essential.