According to a FICCI-EY Risk Survey 2026, 51% of senior business leaders see data breaches as the biggest risk to organisational performance for companies in India. And rightly so. Data breaches have moved from rare occurrences to operational realities. Yet many organisations still struggle with what to do when one occurs. The DPDP Act brings much-needed clarity.
Organisations must strengthen technical defences while ensuring legal compliance. Both need to work together. This blog breaks down what the data breach prevention under DPDP Act requires and how your organisation can build a practical, compliant, and resilient approach to protecting sensitive data.
What DPDPA says about data breaches
The DPDP framework focuses on accountability. It places clear responsibility on Data Fiduciaries to protect personal data and act swiftly when incidents occur.
A personal data breach is broadly understood as any unauthorised access, disclosure, alteration, or loss of personal data. Once such an event is detected, organisations must move fast. There is little room for delay or ambiguity.
The Act expects businesses to prepare in advance and keep prevention, detection, and response processes of equal priority.
Prevention and safeguards under rule 6 of DPDP Act
Before a breach even happens, Rule 6 outlines what organisations must do to reduce risk. These are not optional recommendations but enforceable requirements.
1. Core security controls businesses must implement
The foundation of data breach prevention under DPDP Act lies in strong technical controls. Organisations must implement:
- Encryption, masking, or tokenisation to protect sensitive data
- Obfuscation techniques to reduce data exposure
- Secure storage and transmission practices
These controls ensure that even if data is accessed, it is not easily usable.
2. Access control and monitoring requirements
Limiting access is critical. Rule 6 requires strict access management and hence businesses must:
- Define role-based access controls
- Restrict access to authorised personnel only
- Continuously monitor systems for unauthorised activity
Alongside this, maintaining audit trails is mandatory. These logs must clearly show who accessed data, when, and what actions were performed.
3. Log retention and resilience measures
Logs are not just for investigation but a compliance requirement. Organisations must retain logs for at least one year. This ensures traceability during audits or breach investigations. In addition, businesses must implement:
- Disaster recovery systems
- Verified backup mechanisms
- Business continuity planning
These measures ensure operations can continue even after an incident.
4. Vendor and processor accountability
Your security posture is only as strong as your weakest vendor. Rule 6 mandates that Data Processors must follow the same safeguards. This means:
- Contracts must clearly define security obligations
- Vendors must implement equivalent controls
- Regular assessments should validate compliance
We often see organisations overlook this area. Yet, third-party breaches are one of the most common entry points for attackers.
Breach notification requirements under rule 7 of DPDP Act
Even with strong controls, breaches can still happen. What matters next is how quickly and transparently you respond.
1. Notification to individuals under Rule 7(1)
The DPDP Act requires businesses to notify affected individuals immediately and without undue delay. The notification must be clear and concise. It should not confuse or overwhelm the recipient. It must include:
- Description of the breach, including nature and timing
- Likely risks and potential consequences
- Measures already taken or planned
- Steps individuals should take to protect themselves
- Contact details for further assistance
This level of transparency builds trust. It also reduces panic and misinformation.
2. Notification to Data Prevention Board under Rule 7(2)
The reporting process to the Data Prevention Board is structured and time-bound.
Step 1: Immediate intimation
Businesses must send an initial report as soon as the breach is identified. This includes:
- What happened
- Type of data affected
- Number of records involved
- Likely impact
Step 2: Detailed report within 72 hours
Within 72 hours, a full report must be submitted. This includes:
- Detailed sequence of events
- Root cause analysis
- Identification of responsible entities or gaps
- Confirmation that affected individuals were notified
This two-step approach ensures both speed and depth in reporting.
Enforcement and penalties: what is at stake
The Data Prevention Board operates with the authority of a civil court. This is not symbolic. It has real enforcement power. Failure to comply with data breach prevention under DPDP Act can result in penalties of up to INR 250 Crores per instance.
Read: Penalties Under the DPDP Act: How to Avoid Costly Mistakes
Delays in reporting, weak safeguards, or incomplete disclosures can all trigger penalties. For leadership teams, this shifts cybersecurity from a technical concern to a board-level priority.
Operational challenges businesses must prepare for
While the rules are clear, implementation is not always simple. One key challenge is assessing the “likely impact” during an active breach. This requires:
- Rapid analysis
- Cross-team coordination
- Accurate risk estimation under pressure
For many organisations, especially SMEs, this creates operational strain. Another challenge is meeting the 72-hour reporting window. Without a pre-defined process, delays are almost inevitable.
Achieving data breach prevention under DPDP Act
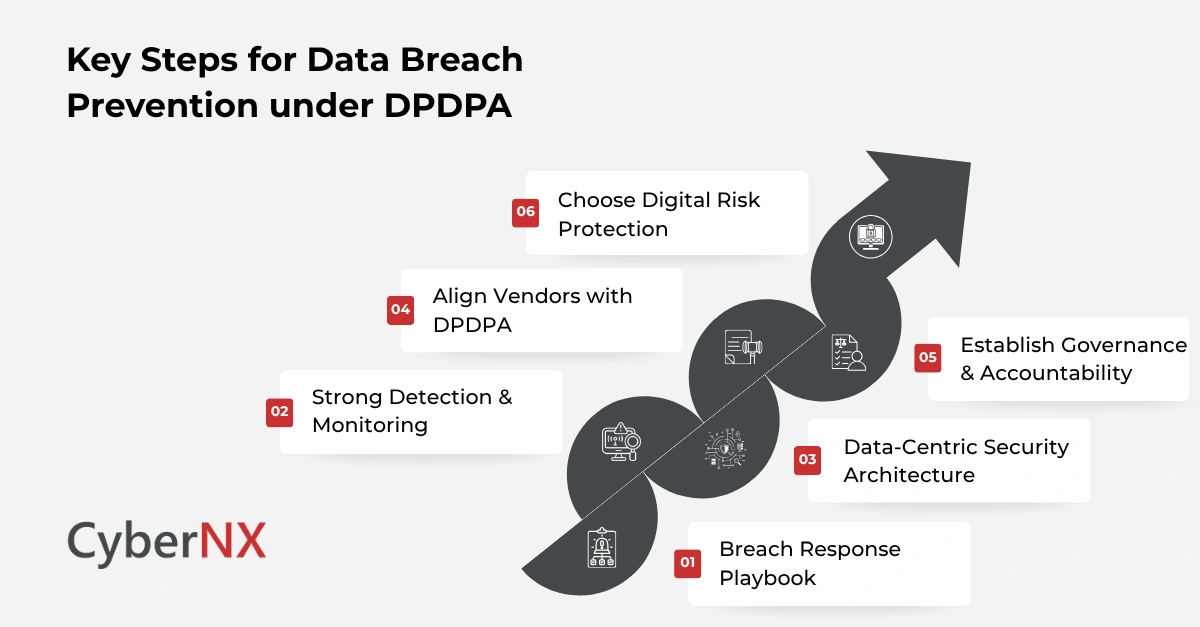
DPDPA compliance requires a structured and proactive approach. Here’s how you can achieve data breach prevention under the Act.
1. Breach response playbook
A well-defined incident response plan, aligned with DPDPA, is essential. This playbook should include clear roles and responsibilities, escalation paths and pre-approved communication templates. It should also align with the immediate notification and 72-hour reporting requirements. We often advise organisations to run simulation exercises. These reveal gaps before real incidents occur.
2. Strong detection & monitoring
Early detection reduces impact. Businesses should invest in security monitoring tools, threat detection systems, centralised logging platforms and real-time visibility that helps teams act quickly and confidently.
3. Data-centric security architecture
Instead of focusing only on network security, shift towards data prevention. This includes data classification, encryption at rest and in transit and tokenisation for sensitive datasets. When data is protected at its core, breach impact is reduced.
4. Align vendors with DPDPA
Third-party risk must be actively managed. Organisations should conduct vendor risk assessments, include DPDP-specific clauses in contracts and monitor vendor compliance regularly. This ensures your ecosystem remains secure.
5. Establish governance & accountability
Strong governance ties everything together. Define:
- A Data Prevention Officer or equivalent role
- Internal audit mechanisms
- Regular compliance reviews
When accountability is clear, execution improves.
6. Choose digital risk protection
Many breaches are first detected outside the organisation, not within internal systems. This is where Digital Risk Protection (DRP) becomes critical, extending visibility into attacker-controlled environments.
DRP helps monitor risks such as leaked credentials, phishing domains, and exposed data across public platforms. It combines detection with action, enabling faster mitigation and takedowns.
This strengthens data breach prevention under DPDP Act by helping organisations:
- Detect breaches earlier
- Assess “likely impact” faster under Rule 7
- Reduce exposure time of compromised data
In practice, DRP improves response speed and gives teams the context needed to act within strict regulatory timelines.
Conclusion
The data breach prevention under DPDP Act sets a clear expectation. Prevent breaches where possible. Respond quickly when they occur. And stay transparent throughout. For businesses, this is both a compliance requirement and an opportunity. Strong data prevention builds trust. It strengthens reputation. And it reduces long-term risk.
At CyberNX, our DPDPA experts help organisations to translate regulatory requirements into practical security strategies. From implementing safeguards to building incident response playbooks, we help you stay prepared without adding complexity.
If you are assessing your readiness for DPDP compliance, now is the time to act. Contact us to know about our DPDPA compliance services and let us help you build a resilient and compliant security posture.
Also, we provide digital risk protection services, which will help you comply with DPDP Act and secure your business digitally.
Data breach prevention under DPDP Act FAQs
What qualifies as a personal data breach under the DPDP Act?
Any unauthorised access, disclosure, alteration, or loss of personal data is considered a breach under the DPDP framework.
Is encryption mandatory under Rule 6?
Rule 6 requires “reasonable security safeguards,” which include encryption, masking, and tokenisation as recommended measures.
What happens if a company misses the 72-hour reporting deadline?
Delays can lead to regulatory scrutiny and financial penalties, depending on the severity and impact of the breach.
Do small businesses need to comply with all DPDP breach requirements?
Yes, all Data Fiduciaries must comply. However, implementation complexity may vary based on scale and risk exposure.