“Attackers don’t break in anymore. They log in.” – Kevin Mitnick, Cybersecurity Expert
And often, they start their work long before a security team notices. For example, your employee’s credentials quietly appearing in a breach forum or a malicious mobile app mimicking your brand.
These threats don’t simply originate inside your corporate network. They begin in external digital environments that most organisations do not actively monitor.
This is where security teams start asking an important question:
Should we focus on dark web monitoring or digital risk monitoring, and which one actually protects our organisation better?
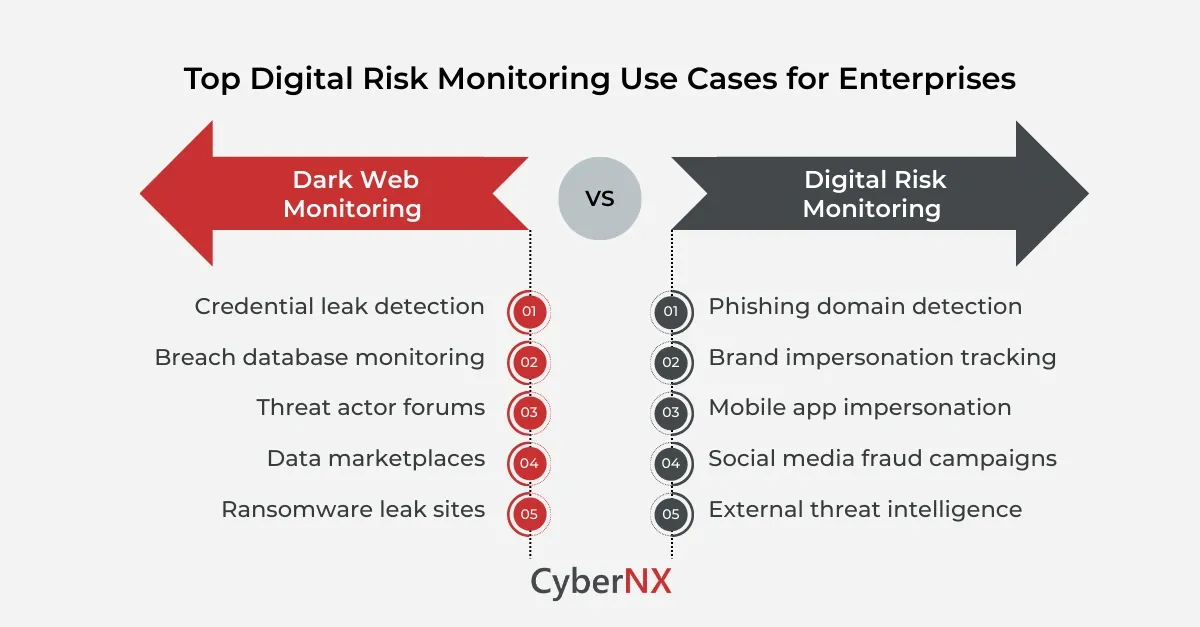
While both approaches help detect external threats, they serve different purposes. One focuses on intelligence from hidden cybercrime communities. The other monitors a broader digital ecosystem where attackers impersonate brands, target customers and leak sensitive information.
Understanding the difference between dark web monitoring vs digital risk monitoring helps you design a stronger external threat visibility strategy.
What is dark web monitoring?
The main focus of dark web monitoring is identifying security risks within hidden internet environments like underground forums, cybercrime marketplaces and breach databases.
These locations are mostly used by threat actors to exchange stolen data, discuss vulnerabilities or sell access to compromised systems.
Security teams typically monitor dark web environments for:
- Stolen employee credentials
- Leaked corporate databases
- Threat actor discussions about specific organisations
- Sale of network access or stolen data
- Ransomware leak site disclosures
Dark web monitoring provides valuable threat insights because it shows what attackers are doing with stolen information after a breach.
But it does not cover the broader digital ecosystem where many attacks begin.
What is digital risk monitoring?
Digital risk monitoring expands visibility beyond hidden forums to include the entire external digital environment where an organisation’s brand, employees and customers may be targeted.
Instead of focusing only on cybercrime communities, digital risk monitoring tracks threats across:
- Domain registrations
- Social media platforms
- Mobile application stores
- Phishing infrastructure
- Cloud-hosted fraud websites
- Public breach datasets
This approach helps companies detect threats earlier, often before stolen data appears in dark web marketplaces.
When evaluating dark web monitoring vs digital risk monitoring, the main difference is scope.
Dark web monitoring focuses on underground intelligence. Digital risk monitoring focuses on broader external threat exposure.
Dark web monitoring vs digital risk monitoring: Key differences
Both support threat intelligence, but they address different stages of the attack lifecycle.
Dark web monitoring identifies threats after data exposure. Digital risk monitoring focuses on detecting threats before customers or employees are impacted.
When organisations should prioritise dark web monitoring
Dark web monitoring becomes more valuable after or during a suspected breach.
Security teams rely on it to understand:
- Whether stolen credentials are circulating online
- If sensitive corporate data is being traded
- Whether attackers are selling network access
- If ransomware groups have leaked company data
These insights help incident response teams understand the scope of compromise.
For many organisations, dark web monitoring acts as a post-breach intelligence capability that supports investigations and remediation.
When organisations need digital risk monitoring
Digital risk monitoring is designed to detect threats before they escalate into security incidents.
Modern attackers frequently impersonate firms on digital platforms to conduct fraud campaigns or steal credentials.
Examples include:
Phishing infrastructure detection
Attackers register domains that resemble legitimate corporate websites to collect credentials.
Brand impersonation on social media
Fraudsters create fake accounts to run scams targeting customers or partners.
Fake mobile applications
Malicious apps disguised as official products steal user data.
Credential exposure monitoring
Security teams detect employee credentials appearing in breach datasets.
These threats exist across the public internet, which is why dark web monitoring vs digital risk monitoring should not be treated as mutually exclusive strategies.
Why enterprises adopt both approaches
Security leaders combine both capabilities to achieve full visibility into external digital risks.
- Dark web monitoring provides intelligence about criminal activity in underground communities.
- Digital risk monitoring detects early signals of attacks that are happening across public digital ecosystems.
Together, they help security teams:
- Detect credential exposure faster
- Identify phishing campaigns earlier
- Protect brand reputation
- Track emerging threat actor behaviour
This kind of strategy ensures organisations do not depend on a single intelligence source.
Real-world examples of external digital risks
The importance of monitoring external environments becomes clearer when looking at real attack scenarios.
- A phishing campaign impersonates a banking brand. Attackers register dozens of fake domains and send fraud emails to customers.
- A software company discovers employee credentials in a breach dataset. The credentials originated from a compromised third-party service.
- An e-commerce brand identifies fake mobile apps that steal payment information from users.
In each of these situations, organisations detected the threat through monitoring external environments rather than internal security alerts.
This is why dark web monitoring vs digital risk monitoring has become a common strategic discussion among security leaders.
How organisations operationalise digital risk monitoring
Implementing monitoring skills requires more than buying threat intelligence tools. Organisations must integrate monitoring insights into their security operations.
A structured process usually includes the following steps.
- Map the firm’s external digital footprint
- Monitor external ecosystems continuously
- Validate potential threat signals
- Prioritise high-risk exposures
- Initiate takedown or remediation actions
Conclusion
External threats rarely begin inside the corporate network.
Attackers impersonate brands, leak credentials and launch phishing campaigns across digital ecosystems long before organisations detect the activity internally.
This is why security leaders increasingly measure dark web monitoring vs digital risk monitoring when designing their external threat visibility strategy.
At CyberNX, we help organisations improve their security through advanced digital risk protection and dark web monitoring capabilities.
If your organisation is evaluating dark web monitoring vs digital risk monitoring, our experts can help you identify the right strategy to monitor brand abuse, detect data leaks and disrupt fraud campaigns before they can impact your business.
Dark Web Monitoring vs Digital Risk Monitoring FAQs
What is the difference between dark web monitoring and digital risk monitoring?
Dark web monitoring focuses on hidden cybercrime communities where stolen data is traded, while digital risk monitoring tracks threats across broader digital ecosystems such as domains, social platforms, and mobile apps.
Which is more important for enterprises?
Both are important. Dark web monitoring helps detect stolen data after breaches, while digital risk monitoring detects threats earlier across public digital environments.
Can digital risk monitoring prevent cyberattacks?
It does not prevent attacks directly but helps organisations detect phishing campaigns, brand impersonation, and credential exposure before major damage occurs.
Do small organisations need digital risk monitoring?
Yes. Small and mid-sized organisations are frequently targeted through phishing and credential theft campaigns.
How often should digital risk monitoring be performed?
Monitoring should be continuous because external digital threats evolve rapidly.