Ransomware, credential theft, and cloud intrusions continue to dominate headlines. Enterprises across sectors are disrupted and operations brought to a halt due to malicious activities. According to 2024 global threat landscape insights from CrowdStrike, adversaries are now breaking out within minutes once inside a network. That speed leaves security teams little room for error.
Many organisations invest in endpoint tools, SIEM platforms, and threat intelligence feeds. And yet we see alerts pile up, teams struggle with skill shortages and critical signals often get missed.
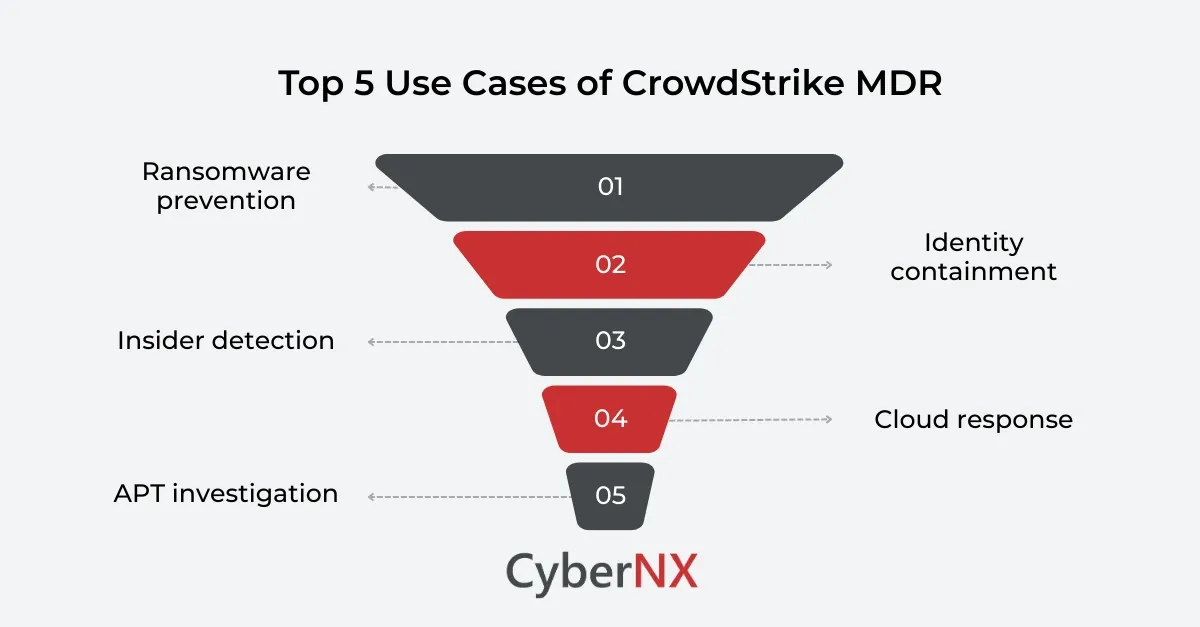
This is where CrowdStrike MDR use cases become highly relevant. Managed Detection and Response combine advanced telemetry, threat intelligence, and expert analysts to detect, investigate, and contain threats before they escalate.
In this blog, we explore practical CrowdStrike MDR use cases through real-world attack scenarios and show how enterprises reduce risk with a managed, proactive approach.
Understanding CrowdStrike MDR in enterprise security
Before diving into specific CrowdStrike MDR use cases, it helps to understand what MDR delivers in practice.
CrowdStrike MDR builds on the CrowdStrike Falcon Platform. It integrates endpoint detection, identity monitoring, cloud visibility, and threat intelligence. More importantly, it adds a team of seasoned analysts who investigate suspicious activity and respond on your behalf.
Our experience shows that technology alone does not solve alert fatigue. Skilled interpretation makes the difference. CISOs and IT leaders, when discussing MDR, should focus on strengthening internal capability with 24/7 expert support.
Let us look at real-world scenarios.
1. Stopping ransomware before encryption
Ransomware remains a top concern for boards and executive teams. Industry research from IBM indicates that ransomware incidents continue to drive significant breach costs, often disrupting operations for weeks.
How the attack unfolds
Majority of times, an attack unfolds when:
- An employee clicks a malicious attachment.
- The attacker gains initial access through a loader.
- Lateral movement begins using stolen credentials.
- Data is exfiltrated before encryption starts.
Traditional controls may detect the malware file. But sophisticated actors use legitimate tools to move quietly.
How MDR changes the outcome
One of the most common CrowdStrike MDR use cases is pre-encryption detection.
The MDR team monitors behavioural indicators such as unusual PowerShell execution, credential dumping attempts, and abnormal administrative activity. Analysts correlate signals across endpoints and identity systems.
Instead of waiting for encryption to trigger alarms, the MDR team isolates affected systems early. They block malicious processes and contain lateral movement. Small timing differences matter. Stopping an attack before encryption avoids operational shutdown and ransom negotiation.
2. Containing identity-based attacks
Identity has become the new perimeter. Attackers target credentials, not just devices. According to Microsoft threat intelligence reporting, identity-driven attacks are rising sharply, with password spray and token theft becoming common entry methods.
Typical enterprise scenario
An attacker gains access to a low-privilege account through phishing. They escalate privileges by exploiting misconfigurations and move into cloud workloads or sensitive databases. Security tools often treat identity and endpoint events separately. This creates blind spots.
MDR-driven response
Among critical use cases is identity threat detection.
The MDR team monitors suspicious login patterns, impossible travel events, and privilege escalation behaviour. Analysts validate whether activity aligns with legitimate business use. If risk is confirmed, access is revoked immediately. In addition, sessions are terminated and compromised credentials are reset.
We often advise clients to combine MDR insights with stronger access governance. Together, they reduce long-term exposure.
3. Detecting insider threat activity
Not all threats come from outside. Since last few years, whether malicious or accidental, insider activity can expose intellectual property or sensitive data.
Real-world pattern
Here is a pattern that we have observed over and over: A departing employee downloads large volumes of files. Data is copied to personal cloud storage and sensitive documents leave the environment unnoticed. Standard monitoring may not flag this if the user has legitimate access.
Role of MDR
Another important example in CrowdStrike MDR use cases involves behavioural analytics. The MDR team evaluates anomalies in file access patterns, data transfer volumes, and unusual login times. They cross-reference HR signals such as resignation status where available.
If suspicious intent is detected, access can be restricted quickly. Investigations begin before data loss becomes public. This approach protects brand reputation and customer trust.
4. Responding to cloud workload intrusions
Cloud adoption has expanded the attack surface dramatically. Misconfigured storage buckets, exposed APIs, and vulnerable containers create new risks. The Cloud Security Alliance continues to highlight misconfiguration as a leading cause of cloud breaches.
How attackers exploit cloud environments
They scan for open services, exploit weak authentication controls and also deploy crypto miners or establish persistent backdoors. Cloud attacks often move faster than traditional response processes.
MDR in cloud environments
Cloud visibility is a growing focus within CrowdStrike MDR use cases.
The MDR team monitors runtime activity in workloads. They detect suspicious container execution, unauthorised API calls, and unusual network traffic between cloud assets. Immediate containment actions can include revoking API keys, isolating workloads, or blocking malicious IP addresses. For organisations scaling rapidly in the cloud, this oversight provides reassurance and control.
5. Investigating advanced persistent threat activity
Some threats are subtle and long-term. These actors move slowly and aim for strategic data. Nation-state activity often involves stealthy techniques that bypass traditional detection.
Typical characteristics includes:
- Low and slow lateral movement.
- Use of legitimate administrative tools.
- Encrypted command and control channels.
How MDR supports advanced investigations
Among the more strategic use cases is proactive threat hunting.
MDR analysts search for indicators of compromise based on global intelligence. The backing of CrowdStrike Intelligence adds context to suspicious behaviours. Instead of reacting only to alerts, the team looks for hidden adversaries already inside. For highly regulated sectors such as finance or healthcare, this capability is essential for long-term resilience.
Key benefits for CISOs and security leaders
Across these use cases, certain patterns emerge.
- First, speed improves dramatically. Detection and response cycles shorten from days to minutes.
- Second, visibility expands. Endpoint, identity, and cloud signals are analysed together.
- Third, internal teams gain breathing room. Instead of chasing every alert, they focus on strategic initiatives.
We often tell clients that effective MDR is about partnership. Your team retains control. The MDR team extends your capability. That combination strengthens governance, improves compliance posture, and reassures executive stakeholders.
Conclusion
The reality facing enterprises is clear. Threat actors move quickly. Attack surfaces expand across endpoints, identities, and cloud workloads.
These CrowdStrike MDR use cases show how managed detection and response prevents ransomware encryption, stops identity abuse, mitigates insider risks, secures cloud environments, and uncovers advanced threats.
CyberNX is a trusted and reliable CrowdStrike services partner. The rich experience of managing Falcon Complete platform equips our team to help you assess, implement, and optimise CrowdStrike MDR tailored to your risk profile. If you want to strengthen detection maturity without overwhelming your internal resources, connect with our experts for CrowdStrike Consulting.
CrowdStrike MDR use cases FAQs
How does CrowdStrike MDR differ from traditional SOC services?
CrowdStrike MDR combines platform telemetry with expert-driven investigation and active response. Traditional SOC services often focus on alert monitoring without deep threat hunting or containment authority.
Is CrowdStrike MDR suitable for mid-sized enterprises?
Yes. Mid-sized organisations benefit significantly because MDR compensates for limited in-house expertise and provides 24 by 7 monitoring without building a full internal SOC.
Can CrowdStrike MDR integrate with existing security tools?
CrowdStrike MDR integrates with various identity providers, cloud platforms, and third-party tools to enhance visibility and streamline response workflows.
How quickly can incidents be contained using MDR?
Containment often occurs within minutes of confirmed malicious behaviour, depending on predefined response policies and environment complexity.