In 2021, attackers launched a phishing campaign that impersonated Microsoft’s login pages using lookalike domains. Thousands of users entered their credentials before the domains were taken down.
The system behind the attack existed publicly for days before the campaign escalated.
For many organisations, this is the reality of modern cyber threats. The signals appear early – fake domains, impersonation profiles, credential leaks – but they go unnoticed because monitoring programs are not designed to detect them.
Understanding the common gaps in digital risk monitoring programs is quite important as it helps security teams close these visibility gaps and identify external threats before they turn into large-scale incidents.
What digital risk monitoring programs are designed to achieve
Digital risk monitoring focuses on identifying cyber threats across an organisation’s digital footprint.
This includes monitoring environments such as:
- social media platforms
- domain registrations
- phishing websites
- dark web forums
- data breach repositories
- mobile app stores
The goal is to detect risks that affect brand reputation, customer trust and organisational security before they escalate into incidents.
But even mature security teams often neglect important aspects of external threat monitoring.
This is where the common gaps in digital risk monitoring programs begin to appear.
Why digital risk monitoring programs fail to deliver full visibility
Digital ecosystems are huge and constantly changing. Threat actors exploit multiple platforms simultaneously, which makes it difficult for organisations to maintain complete visibility.
Many monitoring programs are built around specific tools or isolated intelligence sources. Without a unified approach, security teams struggle to correlate signals and identify emerging threats.
Recognising the common gaps in digital risk monitoring programs is the first step toward building a more effective external threat intelligence strategy.
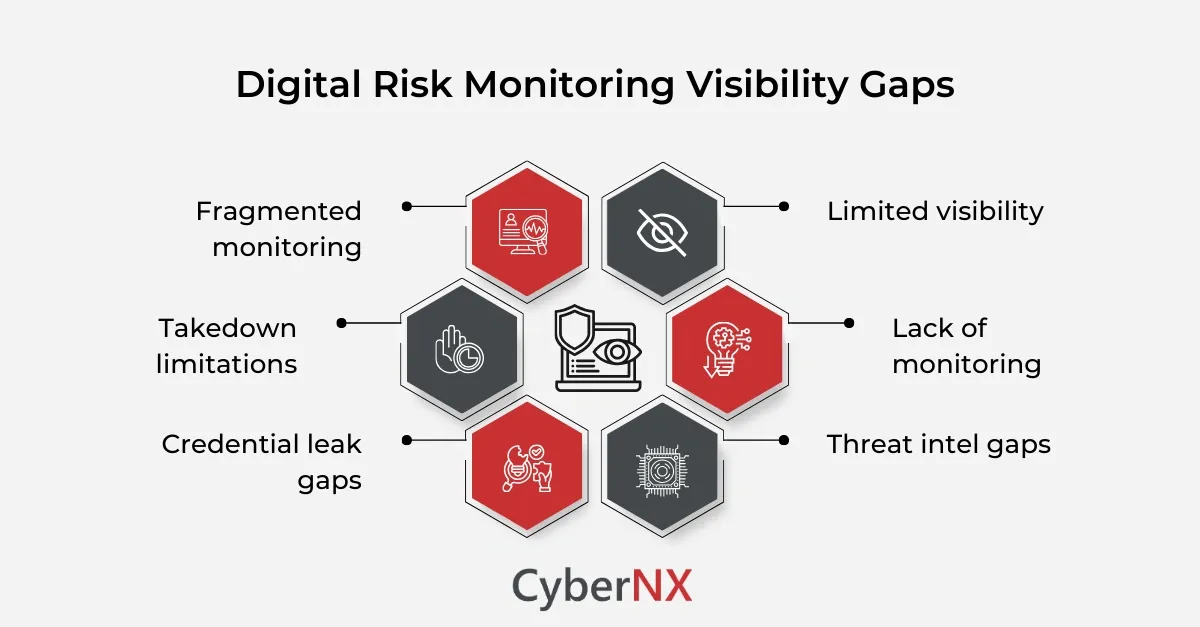
Common gaps in digital risk monitoring programs
Several weaknesses frequently appear when organisations evaluate their monitoring capabilities.
Below are some of the most common gaps security teams encounter:
1. Limited visibility across digital environments/Limited visibility
Many monitoring programs focus only on dark web forums or breach databases.
However, threats frequently originate in other environments such as:
- social media platforms
- phishing infrastructure
- fraudulent mobile applications
- cloned websites
Without visibility across these platforms, organisations may detect attacks only after customers report them. Limited monitoring scope remains one of the most common gaps in digital risk monitoring programs.
2. Lack of brand impersonation monitoring/Lack of monitoring
Brand impersonation has become a major attack vector for cybercriminals.
Threat actors frequently create:
- fake domains resembling legitimate brands
- social media accounts impersonating executives
- fraudulent customer support channels
These impersonation campaigns are often used to conduct phishing attacks or financial fraud. When organisations fail to monitor brand misuse across digital platforms, attackers can exploit brand trust for extended periods.
3. No integration with threat intelligence workflows/Threat intel gaps
Monitoring tools generate alerts but alerts alone do not provide actionable intelligence.
Without proper integration into security workflows, organisations struggle to:
- validate alerts quickly
- correlate multiple threat signals
- prioritise high-risk exposures
This operational gap often prevents security teams from acting on early warning signals. As a result, important threats remain unresolved.
4. Inadequate monitoring of credential leaks/Credential leak gaps
Credential exposure remains one of the most common causes of security incidents. Employee credentials often appear in:
- breach datasets
- cybercrime marketplaces
- underground forums
Without monitoring these sources, organisations may remain unaware that attacker groups already have their access credentials.
Therefore, it’s a key component of digital risk monitoring. Failure to implement it represents one of the most common gaps in digital risk monitoring programs.
5. Lack of takedown capabilities/Takedown limitations
Detecting threats is only part of the response process. Organisations must also remove malicious infrastructure quickly.
This includes:
- phishing domains
- impersonation websites
- fraud social media profiles
- malicious applications
Without coordinated takedown support, organisations may detect threats but be unable to mitigate them.
6. Fragmented monitoring across multiple tools/Fragmented monitoring
Many organisations depend on multiple monitoring tools to track different threat environments.
For example:
- one tool monitors dark web activity
- another monitors domain registrations
- another monitors social media impersonation
Without unified intelligence analysis, these signals remain disconnected. Fragmented monitoring makes it difficult to identify coordinated attack campaigns.
How security teams can strengthen digital risk monitoring
Addressing the common gaps in digital risk monitoring programs requires a structured monitoring strategy. Security leaders should focus on improving visibility across the entire digital ecosystem.
This includes monitoring:
- open web environments
- deep web repositories
- social platforms
- cybercrime forums
Unified monitoring systems help organisations correlate signals and prioritise response actions effectively.
Why closing monitoring gaps matters for enterprises
External cyber threats evolve faster than traditional security controls. Attackers exploit exposed digital environments to conduct fraud, impersonation and data theft campaigns.
Organisations that fail to address the common gaps may experience:
- reputational damage
- customer fraud incidents
- credential compromise
- regulatory scrutiny
Closing these gaps help organisations to detect threats earlier and reduce their overall risk exposure.
Conclusion
Cyber threats today don’t always originate within the corporate network. They emerge across social platforms, phishing infrastructure, data leak repositories and cybercrime marketplaces.
Digital risk monitoring helps companies detect these threats. But many monitoring programs still suffer from limited visibility, fragmented tools and incomplete intelligence workflows. Understanding these gaps allows security leaders to improve their monitoring strategy and improve external threat detection.
We address the key challenges faced by firms, help with advanced threat analysis and provide ongoing protection. Our DRP Services are designed for regulated, consumer-facing & high-trust industries where brand misuse causes immediate harm.
If you want to understand the common gaps in digital risk monitoring programs affecting your organisation, connect with us and protect your brand from growing cyber risks.
Common gaps in digital risk monitoring programs FAQs
What are digital risk monitoring programs?
Digital risk monitoring programs track external threats affecting an organisation’s digital footprint. It includes brand impersonation, credential leaks, phishing infrastructure and dark web exposure.
Why do digital risk monitoring programs often fail?
Programs often fail due to limited monitoring scope, fragmented intelligence tools and lack of integration with incident response workflows.
What types of threats should digital risk monitoring detect?
Effective monitoring programs detect phishing campaigns, brand impersonation, credential leaks, fraud schemes and malicious infrastructure targeting customers or employees.
How can organisations improve digital risk monitoring?
Organisations can improve monitoring by adopting unified intelligence frameworks, expanding coverage across digital environments, and integrating monitoring with security operations workflows.
How often should digital risk monitoring be performed?
Monitoring should be continuous because cyber threats emerge across digital platforms at all times.