To understand why dark web monitoring is important for your business, you will have to first understand the environment being monitored, which is dark web.
The dark web refers to parts of the internet that are intentionally hidden and inaccessible through standard browsers. Access requires specialised software such as Tor. These networks are designed to provide anonymity, both for users and for hosted services.
While anonymity has legitimate uses, it also creates space for cybercrime ecosystems. Stolen data, malware kits, access credentials and insider information are frequently traded there.
Why hackers love the dark web (and why your data ends up there)
From an attacker’s perspective, the dark web offers three advantages.
- First, anonymity reduces the risk of identification.
- Second, decentralised marketplaces make takedowns harder.
- Third, trusted forums allow repeat transactions between criminals.
For businesses, this means that early warning signs of attacks often appear in places traditional security tools cannot see. The most common data linked to organisations includes employee login credentials, customer databases, payment details, intellectual property, internal documents and VPN or remote access credentials. Once exposed, this data rarely stays contained. It is copied, resold and reused across multiple threat campaigns.
How hackers move sensitive info to dark web market
Understanding how data reaches the dark web helps organisations reduce exposure at the source.
Phishing and credential harvesting
Phishing remains one of the most common entry points. When users enter credentials into fake portals, those details are often sold or shared within hours. Many credential dumps originate from automated phishing campaigns targeting cloud email and collaboration tools.
Malware and infostealers
Infostealer malware silently collects browser data, saved passwords, cookies and tokens. Once exfiltrated, this information is packaged and sold in bulk. These logs often include access to corporate email, VPNs and internal applications.
Third-party breaches
Your data does not always leak from your own systems. Suppliers, service providers and partners can become the weak link. When they are breached, your information may surface alongside thousands of other organisations in underground markets.
Insider activity
Disgruntled or compromised insiders sometimes sell access or data directly. These cases are harder to detect internally and often first appear in closed forums. Dark web monitoring can provide early signals before damage escalates.
What is dark web monitoring in practical terms?
Dark web monitoring is the continuous process of searching hidden online sources for information linked to your organisation. This includes domains, brand names, employee emails, credentials, customer identifiers and proprietary data.
The goal is early detection. Not just knowing that data has leaked but knowing it before attackers exploit it at scale.
Unlike surface web searches, this monitoring focuses on underground forums, encrypted messaging channels, paste sites and dark web marketplaces where cybercriminals operate.
The mechanics of dark web monitoring
Dark web monitoring is not a single scan or tool. It is a layered capability.
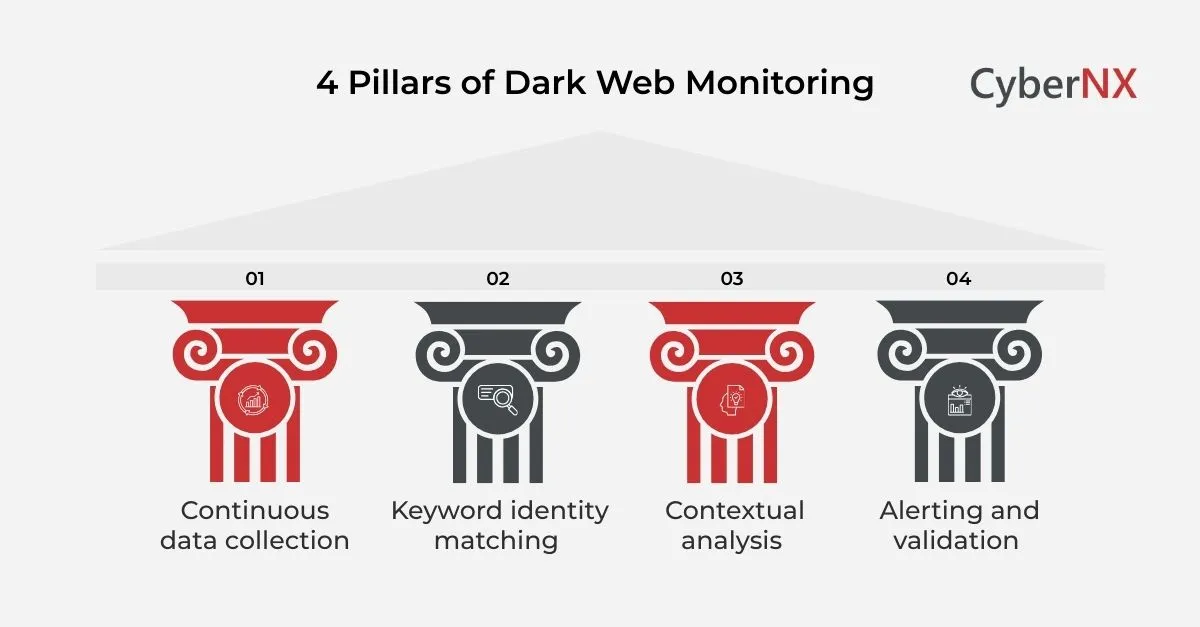
Continuous data collection
Specialised crawlers and intelligence feeds gather content from thousands of dark web sources. These include marketplaces, forums, chat groups and leak sites. Because many platforms restrict access, this process often relies on long-term intelligence collection rather than simple scraping.
Keyword and identity matching
Collected data is analysed for matches linked to your business. This could be email domains, brand names, IP ranges, document fingerprints or executive identities. Advanced platforms go beyond exact matches. They look for variations, misspellings and partial identifiers that attackers commonly use.
Contextual analysis
Not all mentions represent risk. Effective dark web monitoring analyses context. Is the data fresh? Is it being sold, shared or simply discussed? Is the source credible within criminal communities? This reduces noise and helps teams focus on real threats.
Alerting and validation
When relevant findings emerge, alerts are generated for security teams. High-quality services validate findings before escalation to reduce false positives. This is where human expertise still matters.
Why dark web monitoring matters for businesses today
Many organisations still view dark web monitoring as optional intelligence. That view is changing.
Credential-based attacks keep rising
Stolen usernames and passwords remain one of the easiest ways into corporate systems. Once credentials appear on the dark web, attackers often automate their use across cloud services, VPNs and email platforms. Early detection allows forced resets, access reviews and containment before exploitation.
Breaches now have long tails
A single breach can expose data that circulates for years. Even if the initial incident is contained, reused data can trigger future compromises. Dark web monitoring helps identify ongoing exposure long after the original event.
Regulatory and reputational pressure is real
Data exposure has legal, financial and reputational consequences. Being unaware of leaked data does not remove responsibility. Monitoring provides evidence of due diligence and supports faster incident response.
Attackers collaborate openly
Threat actors share techniques, tools and access. Discussions about vulnerabilities or misconfigurations often precede attacks. Dark web monitoring can surface intent, not just outcomes.
Business use cases for dark web monitoring
Dark web monitoring is not limited to security operations teams. Its value spans the organisation.
- Incident response and breach detection: When alerts indicate exposed data, response teams can validate scope, notify stakeholders and initiate containment. This shortens dwell time and limits damage.
- Identity and access management support: Monitoring exposed credentials informs identity teams about weak passwords, reused credentials and high-risk accounts. This data strengthens authentication policies and access reviews.
- Brand and executive protection: Executive impersonation, fraud campaigns and brand misuse often start on underground channels. Monitoring helps detect these risks early, protecting leadership and customers.
- Third-party risk visibility: Leaked data sometimes originates from suppliers or partners. Monitoring can reveal exposure beyond direct corporate systems. This supports more informed vendor risk management.
Dark web monitoring versus traditional security controls
It is important to understand what dark web monitoring is and is not.
- Not a replacement for prevention: Firewalls, endpoint protection and email security remain essential. Dark web monitoring does not block attacks directly. Instead, it provides intelligence about failures that have already occurred or are about to.
- Complementary to SIEM and SOC operations: Security information and event management systems focus on internal telemetry. Dark web monitoring looks outward. Together, they provide a fuller picture of risk.
- Different from vulnerability scanning: Vulnerability scans identify weaknesses. Dark web monitoring identifies exploitation evidence.
Dark web monitoring tools: what exists today
Dark web monitoring tools vary widely in capability and maturity.
Standalone monitoring platforms
These tools focus exclusively on discovering leaked data and underground mentions. They often provide dashboards, alerts and reports tailored to identity exposure and brand risk.
They work well for organisations seeking targeted visibility but may require integration effort.
Threat intelligence platforms with dark web coverage
Many threat intelligence platforms include dark web monitoring as one component. This allows correlation with broader threat data, such as malware campaigns or actor profiles.
This approach suits organisations with mature security operations.
Managed dark web monitoring services
Some organisations prefer a fully managed model. Here, specialists handle collection, analysis and reporting.
This is often effective for teams that lack time or in-house expertise to interpret findings.
Our experience shows that the right model depends on internal capability, not organisation size.
The other confirms it.
What to look for in a dark web monitoring solution
Choosing a dark web monitoring capability is not about ticking feature boxes. It is about how effectively it reduces uncertainty and supports timely decisions.
Before evaluating vendors, it helps to be clear about what value you expect the solution to deliver.
Depth and credibility of source coverage
Many tools claim dark web coverage, but in practice they monitor a limited set of public paste sites or well-known marketplaces.
A strong solution should monitor a broad mix of sources, including closed forums, invite-only communities, ransomware leak sites, underground chat channels and credential dumps. Depth matters more than volume. The ability to observe trusted criminal spaces often delivers more value than scanning hundreds of low-quality sources.
Look for transparency on where intelligence comes from and how access is maintained over time.
Ability to detect business-relevant exposure
Not all leaked data is equally dangerous. A good solution focuses on what actually affects your organisation.
This includes employee and contractor credentials, customer data, internal documents, VPN access details, API keys, cloud tokens and references to internal systems. Advanced monitoring goes beyond simple keyword matching and identifies contextual clues that point to genuine exposure.
This is where dark web monitoring becomes practical rather than theoretical.
Context, prioritisation and risk scoring
Raw alerts are rarely useful on their own. Security teams need to understand urgency and impact.
Effective solutions enrich findings with context. They explain whether data is newly leaked or recycled, whether the source is reputable, and whether there are signs of active exploitation. Risk scoring helps teams decide what to act on first, especially when resources are limited.
Human-led intelligence and validation
Automation is powerful, but it has limits. Criminal language is vague by design, and intent is rarely explicit.
The most effective dark web monitoring services combine technology with human analysts who understand underground behaviour. Validation reduces false positives and helps interpret ambiguous findings.
This balance is critical for decision-makers who rely on clarity, not speculation.
Integration with security operations
Dark web monitoring should fit naturally into existing workflows.
Alerts should integrate with SIEM, SOAR or incident response platforms. Reporting should support executive communication as well as technical response. Without integration, intelligence often stays unused.
AI in dark web monitoring
Artificial intelligence is increasingly shaping how dark web monitoring works, but expectations must be realistic.
Pattern recognition at scale
AI helps analyse vast amounts of unstructured data. It identifies patterns, relationships and anomalies that humans would miss. This improves detection speed, especially for large enterprises.
Language and sentiment analysis
AI models can interpret slang, abbreviations and coded language used by threat actors. This improves contextual understanding and reduces missed signals. However, human oversight remains essential for nuance.
Predictive insights
Some platforms use AI to infer likely outcomes, such as whether exposed data is likely to be exploited soon. These insights support prioritisation but should inform, not replace, judgement. AI enhances dark web monitoring. It does not remove the need for experience.
Common challenges with dark web monitoring
Despite its benefits, dark web monitoring presents real challenges that leaders should understand.
- Noise and false positives: Without proper tuning and validation, alerts can overwhelm teams. Generic mentions or recycled data often trigger unnecessary concern. High-quality monitoring reduces this by focusing on relevance and freshness.
- Interpreting criminal intent: Threat actors rarely state plans clearly. Posts are fragmented, coded or deliberately misleading. Understanding intent requires experience and context, not just automated analysis.
- Legal and ethical boundaries: Reputable monitoring avoids participation in criminal activity. It observes and analyses without engaging. Organisations should ensure providers follow strict ethical and legal standards.
- Acting on intelligence: The hardest part is often response. Discovering exposed data is only useful if teams know what actions to take next. This is why monitoring should be paired with clear playbooks and ownership.
Latest trends shaping dark web monitoring
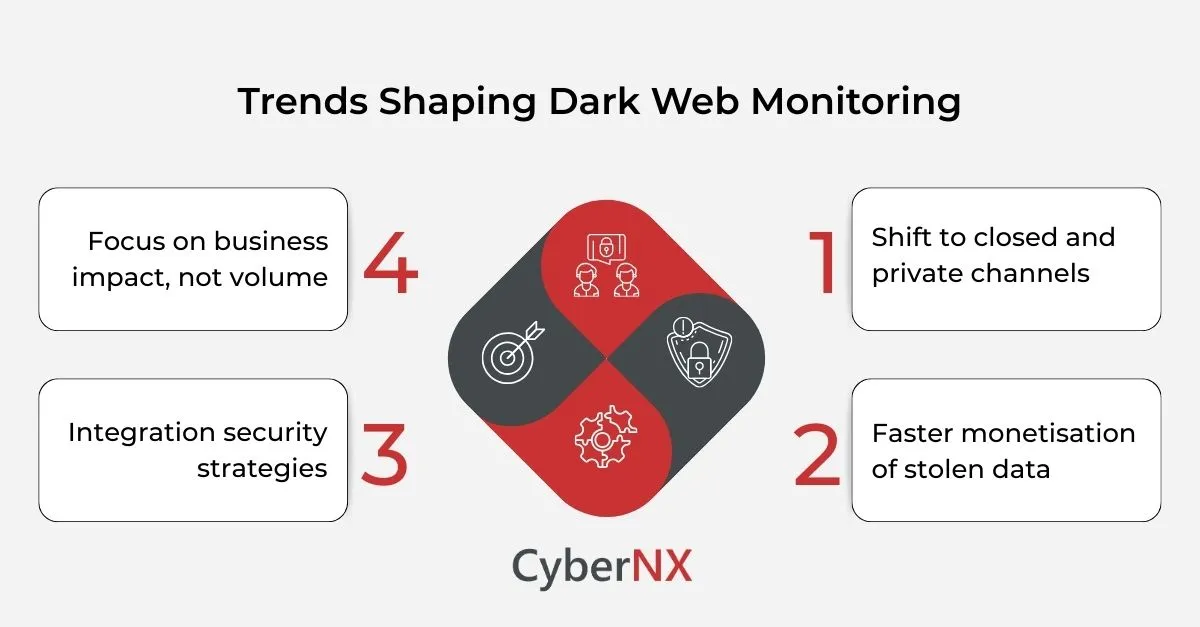
Dark web monitoring continues to evolve alongside attacker behaviour.
1. Shift to closed and private channels
Threat actors increasingly operate in private forums and encrypted messaging platforms. Access requires trust and long-term presence.
This makes sustained intelligence collection more valuable than one-off scans.
2. Faster monetisation of stolen data
Attackers now move from compromise to resale in days, sometimes hours. This shortens response windows significantly. Early detection has become a competitive advantage in security.
3. Integration with identity security strategies
Dark web monitoring is increasingly linked with identity governance and access management. Exposed credentials trigger automated reviews and resets. This convergence improves resilience.
4. Focus on business impact, not volume
Security leaders are shifting focus from how much data is found to what actually matters. Modern dark web monitoring aligns intelligence with business risk, not just technical exposure.
Conclusion
Dark web monitoring has moved from niche intelligence to practical necessity. As businesses expand digital footprints, the likelihood of data exposure increases. Attackers know this and act fast.
Understanding dark web monitoring and using it effectively gives organisations a critical advantage. It provides early warning, supports faster response and reduces uncertainty in an increasingly opaque threat landscape.
If you want to understand what is being said about your organisation in places you cannot see, we can help. Talk to our experts about our dark web monitoring capabilities and how it can be integrated into your security strategy and gaining clearer visibility into hidden risks.
Dark web monitoring FAQs
Can dark web monitoring prevent breaches?
Dark web monitoring does not stop breaches at the point of attack. It works differently. Its value lies in early visibility after data exposure occurs. When credentials, customer data or internal documents appear on the dark web, monitoring helps security teams detect the issue quickly. This allows actions such as forced password resets, access reviews, session revocation and incident investigation before attackers fully exploit the data. In many cases, this early response significantly limits the scale and impact of a breach, even if it cannot prevent the initial compromise.
How often should dark web monitoring run?
Dark web monitoring should run continuously, not periodically. Underground forums and marketplaces update constantly. New data appears every day, often within hours of being stolen. One-time scans or monthly checks leave large blind spots and increase the risk of delayed detection. Continuous monitoring ensures organisations are alerted as soon as relevant exposure is identified, giving teams the shortest possible response window.
Is dark web monitoring relevant for small businesses?
Yes. Small and mid-sized businesses are frequently targeted, often more than large enterprises. Attackers see smaller organisations as easier entry points due to limited security resources, reused passwords and slower detection. Compromised accounts from small businesses are commonly resold or used to access larger supply chains. Dark web monitoring helps smaller organisations detect exposure early, even when they lack large internal security teams.
Does dark web monitoring involve illegal activity?
Reputable dark web monitoring services operate within legal and ethical boundaries. They do not participate in criminal transactions or encourage illegal behaviour. Instead, they observe, collect and analyse publicly available or accessible underground information for intelligence purposes. Organisations should always choose providers that follow strict compliance standards and clearly define how intelligence is gathered and handled.