Note: This blog discusses brand monitoring tools designed for cybersecurity and risk mitigation. It does not address digital marketing or social media analytics tools, which are often confused with security-focused brand protection solutions.
Your brand is one of your most trusted assets. It is also one of the most exploited. Attackers rely on familiar names to lower defences. A trusted logo or domain is often all it takes to trigger phishing, fraud or credential theft. For security teams, the challenge is visibility. Most brand abuse happens far outside the corporate perimeter.
This is where brand risk monitoring tools play a critical role. Built for cybersecurity use cases, they help organisations identify malicious brand activity early and act before real damage occurs.
What is a cybersecurity brand risk monitoring tool?
A cybersecurity brand risk monitoring tool continuously monitors the internet for unauthorised or malicious use of an organisation’s brand, identity and digital assets. These tools are designed for security teams, not marketing functions. Their focus is threat detection, not engagement or sentiment.
To know in-depth about what this cybersecurity monitoring means, read our blog Brand Risk Monitoring Guide.
1. External threat visibility
Brand monitoring tools scan the open web, dark web and underground sources where attackers register domains, build phishing infrastructure and trade stolen data. This external visibility closes a gap that most internal security controls cannot cover.
2. Brand abuse detection
They identify lookalike domains, spoofed email infrastructure, cloned websites and fake mobile applications using brand elements. The aim is early discovery before customers or partners are targeted at scale.
3. Risk-driven context
Mature tools add context to alerts by linking brand abuse to known campaigns, infrastructure or threat actors. This helps security teams prioritise real risk instead of chasing noise.
Why brand monitoring tools matter in cybersecurity
Brand abuse is no longer an edge case. It is one of the most reliable entry points for modern cybercrime.
- Trust exploitation as an attack vector: Attackers use trusted brands to bypass scepticism. Users click links, share credentials and approve payments because the brand feels familiar. No malware is required. No system needs to be breached directly.
- Limited visibility with traditional controls: Firewalls, EDR and email security focus inward. Brand abuse operates outward. Without brand monitoring tools, security teams often learn about attacks only after impact.
- Reduced business and regulatory risk: Early detection limits fraud, reduces customer harm and supports faster incident response. For leadership teams, this directly lowers reputational and compliance exposure.
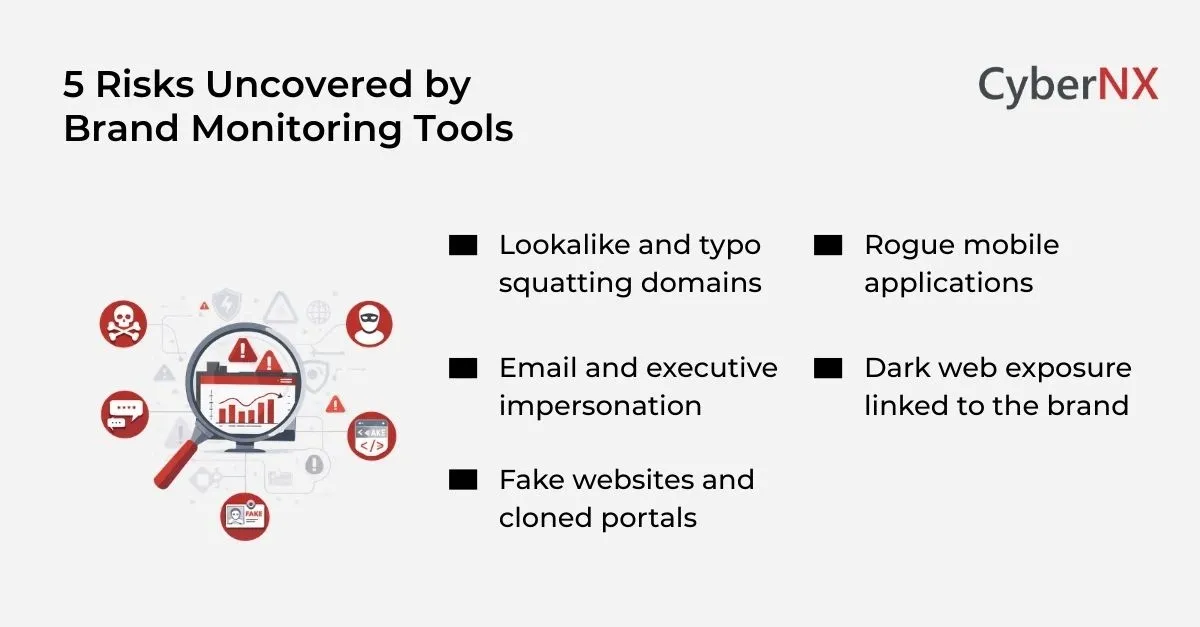
Common risks uncovered by brand monitoring tools
Brand monitoring tools surface risks that typically remain hidden until customers complain or fraud occurs.
1. Lookalike and typo squatting domains
Attackers register domains that closely resemble legitimate brand URLs. These domains are used for phishing, malware delivery or fake login portals. Early discovery allows security teams to act before campaigns scale.
2. Email and executive impersonation
Spoofed sender infrastructure is used to impersonate executives, finance teams or suppliers. These attacks often lead to invoice fraud or credential theft. Brand monitoring tools detect this infrastructure before emails reach targets.
3. Fake websites and cloned portals
Threat actors clone customer portals, payment pages or support sites. These replicas are visually convincing and designed to harvest credentials silently. Monitoring tools identify these sites through content similarity and hosting indicators.
4. Rogue mobile applications
Fake mobile apps abusing brand names and logos are increasingly common. These apps may remain active for weeks, harvesting credentials unnoticed. Brand monitoring tools help identify and report these apps early.
5. Dark web exposure linked to the brand
Some platforms monitor underground forums and marketplaces for stolen credentials, leaked data or brand-related discussions. This intelligence helps security teams understand intent and prioritise response.
Top cybersecurity brand monitoring tools evaluated by enterprises
Organisations evaluate brand monitoring tools based on visibility, intelligence depth and operational fit. The following platforms are frequently reviewed.
- Recorded Future Brand Intelligence: offers brand monitoring as part of its threat intelligence platform. It tracks phishing infrastructure, domain abuse and dark web activity tied to brand impersonation. Its contextual risk scoring appeals to intelligence-led security teams.
- ZeroFox Digital Risk Protection: focuses on external digital risk, including brand impersonation across domains, social platforms and mobile ecosystems. It is often selected by organisations with large customer bases and high exposure to fraud.
- Cyble Vision: combines brand risk monitoring with dark web and fraud ecosystem intelligence. Its strength lies in identifying leaked credentials and early signals of brand-linked criminal activity.
How to select the right brand monitoring tool
Selecting from the best brand monitoring tools requires clarity on risk, not just feature comparisons.
1. Start with your threat profile
Understand how your brand is most likely to be abused. Consumer brands often face phishing and fake apps. B2B organisations see invoice fraud and executive impersonation.
2. Evaluate coverage depth
Effective tools monitor domains, email infrastructure, mobile apps and underground sources. Partial coverage creates blind spots.
3. Assess integration and workflow fit
Alerts should flow into existing SOC processes. Integration with SIEM, SOAR and case management systems reduces friction and response time.
4. Consider response support
Detection without remediation slows action. Some tools assist with domain takedowns and abuse reporting, which shortens the attack lifecycle.
Are there AI brand risk monitoring tools yet?
Yes, but with realistic expectations.
Many of the best AI brand monitoring tools use machine learning to detect patterns that manual or rule-based approaches miss. This includes identifying lookalike domains, logo misuse and phishing content variations.
AI is particularly effective in scaling discovery and prioritisation. However, it does not eliminate false positives. Human validation remains essential for accurate response.
The most effective platforms use AI to speed up detection while keeping analysts in the loop for decision-making.
Where brand monitoring fits in a modern security programme
Brand monitoring tools complement email security, identity protection and threat intelligence functions. They extend visibility beyond the network and into the spaces attackers actually operate.
When integrated properly, they act as early warning systems for phishing, fraud and data exposure. This allows security teams to respond proactively rather than reactively. We often see better outcomes when brand risk ownership is clearly defined across security, legal and customer teams, supported by clear response playbooks.
Conclusion
Brand abuse has become a frontline cybersecurity risk. It enables phishing, fraud and trust erosion without breaching internal systems.
The right brand monitoring tools give organisations the visibility and time needed to stop attacks early. Tooling alone is not enough. Integration, ownership and response discipline matter just as much.
At CyberNX, we work alongside security leaders to assess brand risk exposure, evaluate the best brand monitoring tools and embed them into everyday security operations.
If brand impersonation, phishing or digital fraud is a growing concern, speak with our experts to know about our brand risk monitoring services. We help organisations design and operationalise cybersecurity-focused brand monitoring programmes that deliver measurable risk reduction.
Brand monitoring tools FAQs
How is cybersecurity brand monitoring different from social media or marketing brand monitoring?
Cybersecurity brand monitoring is designed to detect malicious activity such as phishing domains, impersonation emails, fake websites and fraud infrastructure. Marketing or social media monitoring focuses on engagement, reach and sentiment. The tools, data sources and response actions are fundamentally different.
Can brand monitoring tools actually prevent phishing and fraud?
Brand monitoring tools do not stop attacks on their own, but they play a critical prevention role. By detecting malicious infrastructure early, security teams can initiate takedowns, block domains and warn users before phishing campaigns gain scale. This significantly reduces financial and reputational impact.
How do brand monitoring tools fit alongside email security and EDR?
Email security and EDR protect internal users and endpoints. Brand monitoring extends visibility outside the organisation, identifying attacker infrastructure before it reaches those controls. Together, they create a more complete defence by covering both external preparation and internal execution stages of attacks.
Are brand monitoring tools relevant for organisations with limited customer exposure?
Yes. B2B organisations are frequently targeted through executive impersonation, supplier fraud and invoice manipulation. Even without a large consumer base, brand abuse can lead to direct financial loss and contractual disputes.