Are you exploring CrowdStrike NG-SIEM migration from Splunk? If yes, you are reading the right blog.
SIEM migration is not a simple technology switch. It involves rethinking data pipelines, detection rules, integrations and operational workflows. Our experience shows that with the right migration approach, organisations can transition smoothly while strengthening their overall security posture. This guide explains how to plan and execute a migration from CrowdStrike NG-SIEM to Splunk step by step.
Possible reasons for CrowdStrike NG-SIEM migration from Splunk
Many organisations are exploring alternatives for several practical reasons.
Rising SIEM data costs
Splunk pricing often scales with data ingestion. As organisations collect more logs from cloud, identity and SaaS platforms, SIEM costs can grow rapidly. This creates a difficult choice. Either reduce visibility or accept higher operational expenses.
CrowdStrike NG-SIEM introduces a different model. It focuses on optimised data ingestion and unified telemetry within the Falcon platform. This helps security teams maintain visibility without constantly worrying about data limits.
Fragmented security tooling
Most enterprises operate dozens of security tools. Each generates alerts, logs and telemetry. Splunk often becomes the central repository. Yet correlation across tools can still require heavy customisation and complex queries.
CrowdStrike NG-SIEM integrates endpoint, identity, cloud and threat intelligence signals within a single security platform. This reduces complexity while improving investigation speed.
Detection speed and automation
Traditional SIEM architectures depend heavily on log ingestion and search queries. This can delay detection workflows. CrowdStrike NG-SIEM combines telemetry, threat intelligence and behavioural analytics in real time. The result is faster threat identification and automated response capabilities. For security operations centres, this improvement can significantly reduce investigation time.
Read: CrowdStrike NG-SIEM vs Splunk: A Practical Comparison
CrowdStrike NG-SIEM to Splunk: key considerations
A successful migration begins long before technology deployment. Security leaders should assess their current environment carefully. The goal is to understand what must be preserved, replaced or redesigned.
Inventory existing data sources
Start with a full inventory of data sources currently feeding Splunk.
These typically include:
- Endpoint logs
- Firewall telemetry
- Cloud infrastructure logs
- Identity and access systems
- SaaS platforms
- Security tools such as EDR and IDS
Some data sources may already exist within the CrowdStrike ecosystem. Others may require integration planning. Clear visibility into existing data pipelines prevents surprises later.
Review existing detection rules
Many organisations build hundreds of correlation rules within Splunk. These rules often evolve over years. While some remain critical, others become outdated. Before migration, security teams should review:
- Active detection rules
- Custom search queries
- Alert thresholds
- Threat hunting workflows
This review helps determine which detections should be recreated within CrowdStrike NG-SIEM.
Evaluate compliance & retention requirements
Compliance frameworks often require log retention for specific time periods. Examples include RBI, SEBI, CERT-In in India, and PCI DSS, ISO 27001 and GDPR in other countries. While planning a migration, organisations must ensure log retention and audit capabilities remain compliant. Planning archival strategies early avoids regulatory risks.
Map existing integrations
Splunk deployments often integrate with multiple tools such as SOAR platforms, ticketing systems, vulnerability management tools and threat intelligence feeds Security teams should map these integrations carefully. Some may migrate directly to CrowdStrike. Others might require alternative connectors or API configurations.
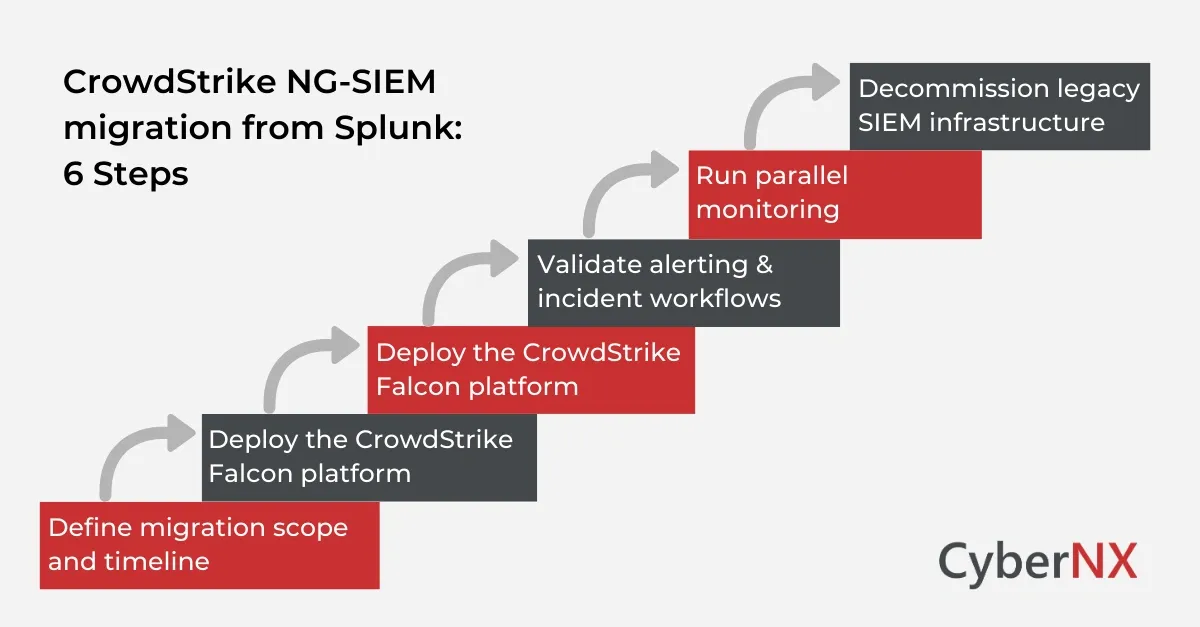
Step-by-step process for CrowdStrike NG-SIEM migration from Splunk
Once planning is complete, organisations can begin the migration process. Breaking the migration into structured phases reduces operational risk.
1. Define migration scope and timeline
Start by defining the scope of the migration.
Key questions include:
- Which use cases will move first?
- Which log sources will be prioritised?
- What timeline is realistic for the SOC team?
Many organisations adopt a phased migration approach. Critical security telemetry moves first, while less important logs migrate later. This approach keeps the security operations centre stable during the transition.
2. Deploy the CrowdStrike Falcon platform
CrowdStrike NG-SIEM operates within the Falcon platform ecosystem.
Deployment typically includes:
- Falcon agents on endpoints
- Cloud workload integrations
- Identity telemetry connections
- Data connectors for security tools
Once telemetry flows into the platform, security teams can begin validating visibility.
This stage ensures the new environment captures the signals required for threat detection.
3. Recreate detection logic
Detection rules must be rebuilt within the CrowdStrike environment. Security teams typically migrate:
- correlation rules
- behavioural detections
- threat hunting queries
- alert workflows
During this stage, teams often discover opportunities to simplify detection logic. Modern platforms frequently reduce the need for complex queries.
4. Validate alerting & incident workflows
Before switching off Splunk monitoring, SOC teams must validate alert behaviour.
Testing should include:
- simulated attack scenarios
- red team exercises
- detection coverage verification
- incident response workflow validation
The goal is simple. Ensure the new SIEM environment detects threats as expected.
5. Run parallel monitoring
Many organisations run Splunk and CrowdStrike NG-SIEM together for a limited period.
This parallel monitoring stage allows security teams to compare:
- alert accuracy
- investigation workflows
- detection coverage
Any gaps can be addressed before full migration.
6. Decommission legacy SIEM infrastructure
After successful validation, organisations can gradually reduce their Splunk footprint.
This typically involves:
- archiving historical logs
- retiring unused integrations
- shutting down unused infrastructure
The end result is a streamlined security monitoring architecture.
Conclusion
Migrating SIEM platforms is a strategic decision. It influences detection capability, operational efficiency and long-term security architecture.
A structured migration enables organisations to modernise their security operations without disrupting existing protections. The key lies in careful planning. Understand existing data pipelines. Rebuild detections thoughtfully. Validate workflows before retiring legacy systems. When done correctly, the result is a streamlined security platform capable of detecting threats faster and supporting modern cloud environments.
At CyberNX, we work closely with organisations planning SIEM modernisation initiatives. Our experts help assess current environments, design migration strategies and ensure security operations remain stable throughout the transition.
If your organisation is considering a CrowdStrike NG-SIEM migration from Splunk, connect with us for a CrowdStrike consultation and our experts will guide you through each stage of the journey.
CrowdStrike NG-SIEM migration from Splunk FAQs
How long does a CrowdStrike NG-SIEM migration from Splunk typically take?
Migration timelines vary depending on data sources and integrations. For large enterprises, the process may take several weeks to a few months, especially when running parallel monitoring.
Can organisations keep historical Splunk data after migration?
Yes. Historical logs can be archived in storage systems or retained within Splunk for compliance and audit purposes while new telemetry flows into CrowdStrike NG-SIEM.
Do SOC analysts require training when moving from Splunk to CrowdStrike NG-SIEM?
Yes. Analysts benefit from training on the Falcon platform interface, query language and investigation workflows to ensure operational efficiency after migration.
Is it possible to run Splunk and CrowdStrike NG-SIEM together?
Yes. Many organisations operate both systems during a transition period to validate detection accuracy and ensure operational continuity.