As part of our ongoing blog series on CrowdStrike NG-SIEM, we now turn our focus to compliance. Specifically, how CrowdStrike NG-SIEM for compliance enables regulated organisations to align with RBI, SEBI and CERT-In mandates.
Financial institutions, capital market entities and critical service providers in India now operate under strict oversight, which is destined to become stringent in the near future. Already, firms under BFSI sector must collect, retain and monitor logs. In addition, they must detect incidents quickly and demonstrate control effectiveness during audits.
So, how does CrowdStrike NG-SIEM helps? It combines modern log management, real-time detection and unified visibility to support these obligations.
For CISOs and compliance leaders in BFSI, the platform offers a practical path to meet regulatory expectations without building fragmented monitoring stacks.
Nuances of India’s regulatory expectations
From a compliance perspective, regulatory guidance in India matured rapidly. While different regulatory bodies like RBI, SEBI and CERT-In has its frameworks, they share common expectations from regulated entities. For example, visibility, accountability and swift incident reporting are common themes that run across the mandates. That’s why we will explore how CrowdStrike NG-SIEM helps compliance after we address the current regulatory landscape and the mandates.
1. RBI cybersecurity and IT framework requirements
The RBI mandates continuous monitoring, log retention, incident response capability and board level reporting. The banks and NBFCs have to:
- Maintain centralised log management
- Monitor user activities and privileged access
- Detect anomalies in near real time
- Report incidents within defined timelines
- Preserve logs for forensic investigations
As digital revolution covers and penetrates the farthest parts of India, manual log reviews isn’t preferred because it cannot bear positive results anymore. What about traditional SIEM tools? They also struggle with cloud telemetry. In this context, CrowdStrike NG-SIEM simplifies this through unified telemetry across endpoints, cloud workloads and identities.
2. SEBI cyber resilience framework
SEBI requires regulated entities such as stock exchanges, brokers and asset managers to:
- Implement real-time monitoring
- Conduct periodic audits and vulnerability assessments
- Maintain audit trails
- Ensure data integrity and access controls
Compliance teams must show evidence during inspections. And that’s a challenge because generating that evidence and that too in quick time is not everyone’s cup of tea. Here, CrowdStrike NG-SIEM comes to the rescue. It provides searchable, centralised logs with automated correlation. This shortens audit preparation cycles and reduces dependency on manual compilation.
3. CERT-In incident reporting mandate
CERT-In mandates reporting of specific cyber incidents within six hours of noticing them. Just imagine the chaos it can cause among security teams. That tight timeline resulting in detection delays could ultimately lead to compliance risk. Well, CrowdStrike NG-SIEM has a solution. It enables rapid detection and contextual investigation. Automated alerting and AI-driven correlation help security teams identify incidents faster, which supports timely reporting.
The traditional SIEM struggle for compliance
One question that can come up is “why CrowdStrike?” And “why not traditional SIEM tools?” First, many enterprises deployed legacy SIEM platforms years ago. Over time, these tools became expensive, complex and noisy. Common pain points include:
- High ingestion costs
- Slow query performance
- Alert fatigue
- Limited cloud-native visibility
- Lengthy integration cycles
This makes compliance reactive. Secondly, the security teams scramble during audits and reports take days to generate. On the other hand, CrowdStrike NG-SIEM addresses these issues with a cloud-native architecture and integrated threat intelligence. Instead of stitching tools together, organisations operate from a unified security data layer.
How CrowdStrike NG-SIEM for Compliance enables regulatory readiness
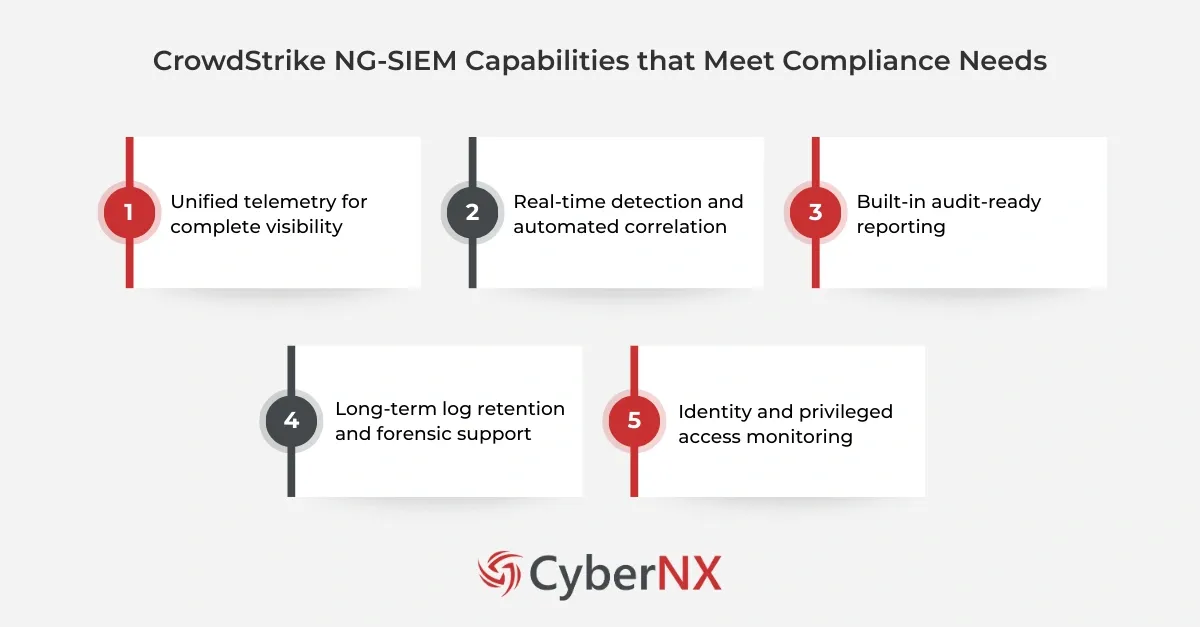
Now, let us come into the gist of the matter and examine the core capabilities of CrowdStrike NG-SIEM that align with RBI, SEBI and CERT-In requirements.
1. Unified telemetry for complete visibility
Comprehensive monitoring is something that regulatory bodies expects. So, gaps in logs could create blind spots.
CrowdStrike NG-SIEM ingests telemetry from endpoints, cloud workloads, identities, network devices and third-party tools. This unified view strengthens audit trails and simplifies investigations.
From a compliance perspective, this means:
- Clear evidence of monitoring controls
- Faster reconstruction of security events
- Reduced reliance on siloed log repositories
2. Real-time detection and automated correlation
Timely detection is a critical aspect CERT-In touches upon. Slow detection would mean regulatory exposure.
CrowdStrike NG-SIEM leverages behavioural analytics and AI-driven correlation. It identifies suspicious activity across multiple data sources in near real time.
This improves:
- Mean time to detect
- Mean time to respond
- Accuracy of incident classification
For compliance teams, improved detection translates into faster notification and more confident reporting.
3. Built-in audit-ready reporting
This is perhaps the most important thing: audit preparation. It often consumes weeks and teams manually extract logs, filter data and create reports.
CrowdStrike NG-SIEM simplifies it for you. It provides structured dashboards and searchable logs. You can generate evidence aligned to regulatory controls without rebuilding data sets.
This capability supports:
- RBI audit submissions
- SEBI inspections
- Internal board reporting
- Third-party audit assessments
Our experience shows that structured visibility reduces last-minute compliance stress.
4. Long-term log retention and forensic support
Log retention for defined periods is a must-have, according to regulatory guidelines. But storage costs and performance trade-offs often limit the retention strategies. CrowdStrike NG-SIEM offers scalable cloud-based retention. Teams can store and query historical logs efficiently.
This ensures:
- Forensic readiness
- Compliance with log preservation mandates
- Support for regulatory investigations
Long-term data access also strengthens threat hunting initiatives.
5. Identity and privileged access monitoring
If you look deep into RBI and SEBI mandates, they emphasise access governance and monitoring of privileged users. CrowdStrike NG-SIEM integrates identity telemetry, paving way for correlation of login events, privilege escalations and suspicious behaviour. This enables:
- Detection of insider threats
- Monitoring of administrative activities
- Stronger evidence of access controls
Conclusion
Using CrowdStrike NG-SIEM for compliance enables Indian organisations to meet RBI, SEBI and CERT-In expectations with confidence. It centralises visibility, accelerates detection and simplifies audit reporting. More importantly, it transforms compliance from a periodic burden into an ongoing strength.
If you are preparing for regulatory audits or strengthening incident reporting frameworks, we can help you design and implement a compliance-driven security monitoring strategy. Connect with us for a CrowdStrike Consultation and let’s build a system that satisfies regulators while empowering your security team.
CrowdStrike NG-SIEM for compliance FAQs
1. How does CrowdStrike NG-SIEM for Compliance help with six-hour CERT-In reporting?
It provides real-time detection and contextual investigation, enabling faster identification and classification of reportable incidents.
2. Can CrowdStrike NG-SIEM for Compliance replace legacy SIEM platforms?
Yes, many organisations adopt it as a modern alternative due to its cloud-native architecture, lower operational overhead and unified telemetry.
3. Does CrowdStrike NG-SIEM for Compliance support cloud and hybrid environments?
It ingests telemetry from cloud workloads, on-premise infrastructure and endpoints, making it suitable for hybrid enterprises.
4. How does it support RBI board-level reporting requirements?
It offers dashboards and structured reporting capabilities that align technical events with governance and risk metrics.