CrowdStrike NG-SIEM combines log management, detection, investigation and response into a unified cloud-native, AI-powered platform. For security teams evaluating it, understanding the architecture and real-world capabilities is critical.
We have worked with organisations across sectors as a CrowdStrike services partner. Our experience shows that the platform delivers strong outcomes when deployed with the right design, data strategy and operational alignment. In this guide, we break down the architecture and key capabilities of CrowdStrike NG-SIEM in simple, practical terms.
What is CrowdStrike NG-SIEM?
CrowdStrike NG-SIEM is a next-generation security information and event management platform built on the CrowdStrike Falcon cloud. It is designed to ingest, analyse and correlate large volumes of security data in real time.
Unlike traditional SIEM systems that rely on complex on-premise infrastructure, CrowdStrike NG-SIEM is cloud-native. It scales automatically. It supports high-speed search. It integrates deeply with endpoint, identity and cloud telemetry.
Most importantly, it reduces operational friction for modern SOC teams.
Mapping the architecture of CrowdStrike NG-SIEM
To use CrowdStrike NG-SIEM effectively, teams need to understand how it is structured. The architecture is built around three core pillars.
1. Cloud-native data ingestion layer
The foundation of CrowdStrike NG-SIEM is its cloud-native ingestion framework.
It collects telemetry from:
- Falcon endpoint agents
- Cloud environments
- Identity providers
- Network devices
- Third-party security tools
Data is ingested at scale without requiring customers to manage storage infrastructure. The system supports structured and unstructured log data.
Because the platform is built in the cloud, it eliminates traditional capacity planning headaches. You do not need to size hardware. You focus on use cases instead.
2. Unified data lake and high-speed search
At the heart of CrowdStrike NG-SIEM sits a unified data lake. This architecture allows:
- Centralised storage of telemetry
- Real-time indexing
- Fast, large-scale search queries
- Cross-domain correlation
Security analysts can run complex queries across endpoint, identity and cloud data without switching tools. The search engine is optimised for speed, which dramatically reduces investigation time.
From our experience, this capability alone changes how teams operate. Investigations that previously took hours can often be reduced to minutes.
3. Detection, analytics and automation engine
The third layer focuses on intelligence and response. CrowdStrike NG-SIEM uses:
- Pre-built detection rules
- Behavioural analytics
- Threat intelligence integration
- AI-assisted investigation workflows
- Automation via Falcon Fusion
This architecture enables detection across multiple telemetry sources with context already attached. Analysts see the full story, not isolated alerts.
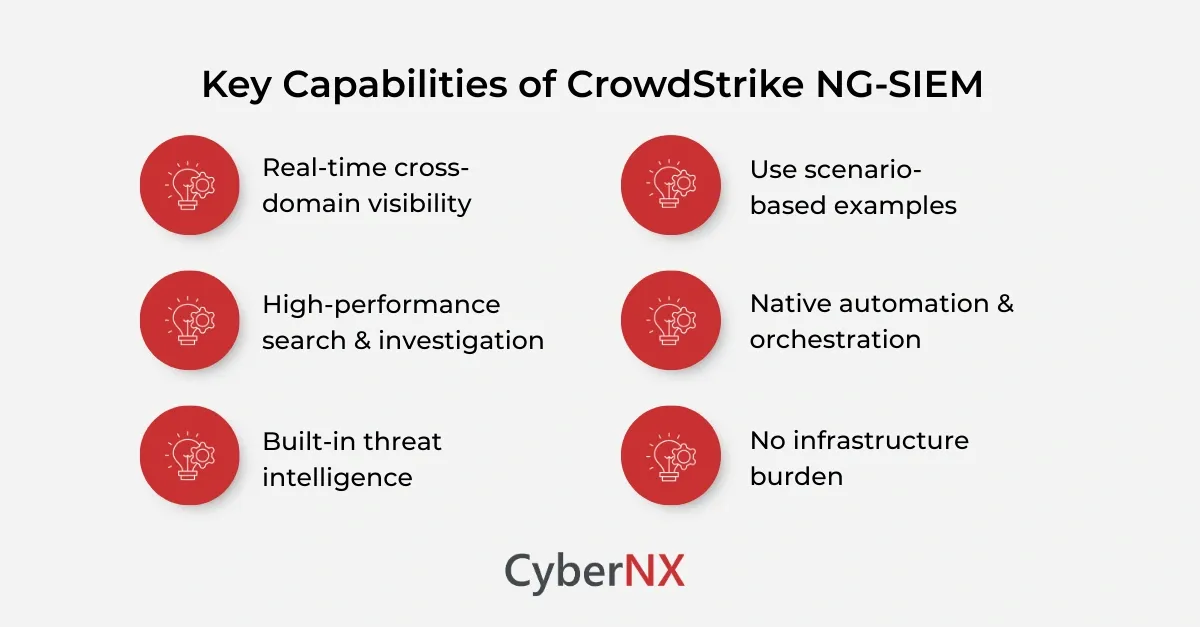
Key capabilities of CrowdStrike NG-SIEM
Now that we understand the architecture, let us explore the core capabilities that matter most to security teams.
1. Real-time cross-domain visibility
CrowdStrike NG-SIEM provides unified visibility across:
- Endpoints
- Identities
- Cloud workloads
- SaaS applications
- Network logs
Because it integrates natively with the Falcon platform, endpoint telemetry is already deeply enriched. This reduces the need for complex correlation rules.
Security teams gain contextual detection. Not just log aggregation.
2. High-performance search & investigation
Traditional SIEM tools often slow down as data grows. CrowdStrike NG-SIEM was engineered for high-speed search at scale.
Analysts can:
- Run advanced queries
- Pivot across data types
- Reconstruct attack timelines
- Investigate historical data quickly
This capability is essential during active incidents. Speed directly affects containment.
In many deployments we have led, SOC teams reported measurable reductions in mean time to investigate within weeks of implementation.
3. Built-in threat intelligence
CrowdStrike NG-SIEM integrates with CrowdStrike’s global threat intelligence.
This allows:
- Attribution insights
- Adversary behaviour mapping
- Indicator enrichment
- Proactive threat hunting
Instead of reacting to alerts, teams can hunt for attacker tradecraft based on real-world intelligence. This strengthens both detection maturity and board-level confidence.
4. AI-assisted workflows
Modern SOCs face alert fatigue. Automation and AI support are no longer optional.
CrowdStrike NG-SIEM includes AI-driven assistance for:
- Alert summarisation
- Incident correlation
- Investigation guidance
- Recommended response steps
This does not replace analysts. It supports them. It reduces repetitive manual effort and allows teams to focus on higher-value decisions.
5. Native automation & orchestration
Through Falcon Fusion integration, CrowdStrike NG-SIEM enables automated response playbooks.
Examples include:
- Isolating compromised endpoints
- Disabling user accounts
- Blocking malicious IP addresses
- Triggering ticketing workflows
Automation reduces dwell time. It also enforces consistency in response actions.
6. No infrastructure burden
One of the most practical benefits of CrowdStrike NG-SIEM is operational simplicity.
There is:
- No hardware to maintain
- No database tuning
- No patching cycles
- No scaling exercises
This allows security teams to shift focus from maintaining SIEM infrastructure to improving detection use cases. For organisations with limited SOC headcount, this is a major advantage.
How CrowdStrike NG-SIEM supports modern cyberattack defence
Attackers move laterally. They exploit identity gaps. They blend into cloud workloads. A siloed SIEM struggles to detect this. CrowdStrike NG-SIEM supports modern defence by enabling:
- Identity-based detections
- Behaviour-driven analytics
- Cross-domain correlation
- Rapid investigation workflows
- Automated containment
For example, consider a compromised identity used to access a cloud workload. CrowdStrike NG-SIEM can correlate login anomalies, endpoint telemetry and cloud API calls into a single detection narrative. That context changes response speed and accuracy.
Deployment considerations for security teams
While CrowdStrike NG-SIEM is powerful, outcomes depend on deployment strategy. From our experience as a services partner, successful implementations focus on:
- Clear detection use cases
- Data onboarding prioritisation
- Log normalisation planning
- Role-based dashboard design
- SOC workflow alignment
Many teams attempt to ingest everything at once. This creates noise. Instead, we recommend a phased rollout aligned with business risk.
Small changes can make a big difference in security. Prioritising identity logs and endpoint telemetry often delivers quick wins.
Common challenges and how to avoid them
Even advanced platforms require thoughtful execution.
- Over-collection of low-value logs: Not all data is useful. Start with high-risk domains.
- Alert overload: Tune detection rules early. Customise to your environment.
- Lack of SOC training: Technology alone does not improve detection maturity. Analysts need structured enablement.
- Misaligned automation: Avoid automating high-risk response actions without testing.
Why CrowdStrike NG-SIEM appeals to enterprise & mid-market teams
Large enterprises benefit from scalability and unified telemetry. Mid-sized organisations benefit from reduced infrastructure overhead. Both benefit from:
- Faster detection
- Reduced complexity
- Strong integration with existing Falcon deployments
- Improved SOC efficiency
The platform bridges the gap between legacy enterprise SIEM complexity and lightweight log tools that lack detection depth.
Conclusion
CrowdStrike NG-SIEM represents a shift in how security teams approach detection and response. Its cloud-native architecture, unified data lake and AI-assisted workflows give modern SOCs the speed and visibility they need.
However, success depends on strategy, configuration and ongoing optimisation.
As a CrowdStrike services partner, we help organisations design, deploy and fine-tune CrowdStrike NG-SIEM to align with real operational goals. If you are evaluating the platform or planning expansion, our team can support architecture planning, detection engineering and SOC alignment.
Speak with us for a CrowdStrike Consulting to maximise your CrowdStrike NG-SIEM investment and strengthen your security operations with confidence.
CrowdStrike NG-SIEM FAQs
How is CrowdStrike NG-SIEM different from traditional SIEM platforms?
CrowdStrike NG-SIEM is cloud-native and deeply integrated with Falcon telemetry. Traditional SIEM systems often require on-premise infrastructure and complex maintenance.
Can CrowdStrike NG-SIEM replace an existing SIEM?
Yes, in many cases it can consolidate log management and detection use cases. However, migration planning and phased onboarding are important.
Does CrowdStrike NG-SIEM support compliance reporting?
Yes. It supports log retention, reporting and dashboard creation aligned to regulatory requirements, though customisation may be required based on industry.
What skills are required to manage CrowdStrike NG-SIEM?
Security analysts familiar with log analysis and detection engineering can manage it effectively. Training on query language and automation workflows is recommended.