Periodic security scans are useful, but they reveal weaknesses only at a given point in time. Today, your digital environments do not stay the same for long. New assets appear, cloud services expand and your employees integrate new tools in their workflows. This gives attackers the opportunity to move quickly and scan the internet for exposed systems within minutes.
The gap between scanning cycles creates blind spots. A vulnerability discovered weeks after it appears may already be exploited. Continuous digital risk monitoring addresses this challenge. Instead of snapshots, it provides ongoing visibility into an organisation’s external attack surface. Security teams gain near real-time awareness of risks, misconfigurations and exposed assets before attackers take advantage.
The limitations of periodic security scans
Periodic scans were designed for simpler IT environments. If your network is smaller, the changes happen slowly and your systems sit within a defined perimeter, you may not need continuous digital risk monitoring.
But the world has changed. Modern enterprises, whether big or small, rely on cloud services, APIs, remote workers and third-party integrations. New digital assets can appear every day. In this context, traditional scanning schedules aren’t enough.
Here are some of the major issues that emerge:
- First, risk visibility is delayed. A vulnerability introduced today may remain undetected until the next scheduled scan.
- Second, shadow IT expands unnoticed. Teams often deploy tools or cloud resources outside central oversight.
- Third, exposed services become easy targets. Attackers constantly scan the internet. They do not wait for your next assessment window.
Periodic scanning therefore provides a limited view of digital risk. It captures conditions at one moment rather than the continuous reality of the attack surface.
How modern attack surfaces evolve
Digital infrastructure now changes at a rapid pace. Each new change introduces potential security gaps and several trends contribute to this complexity.
1. Cloud adoption and rapid deployment
Cloud platforms allow teams to deploy services quickly. Development teams can spin up new environments within minutes. While this agility supports business growth, it also increases the chance of configuration errors. A single misconfigured storage bucket or exposed API endpoint can leak sensitive information. Without continuous digital risk monitoring, these exposures may remain visible to attackers for weeks.
2. Expanding external attack surfaces
Organisations often underestimate how many assets are exposed to the internet. Subdomains, forgotten servers, development environments and legacy systems all contribute to the external footprint.
Many of these assets fall outside traditional asset inventories. Continuous digital risk monitoring helps identify these unknown exposures before adversaries discover them.
3. Third party dependencies
Modern businesses depend heavily on vendors, SaaS tools and integrations. While these partnerships enable efficiency, they also introduce additional risk.
A compromised third-party domain, leaked credential or vulnerable integration can affect the wider ecosystem.
Continuous monitoring helps track these risks as they emerge.
What continuous digital risk monitoring does
Continuous digital risk monitoring provides ongoing visibility into an organisation’s external digital presence. Instead of waiting for scheduled assessments, risks are identified as they appear.
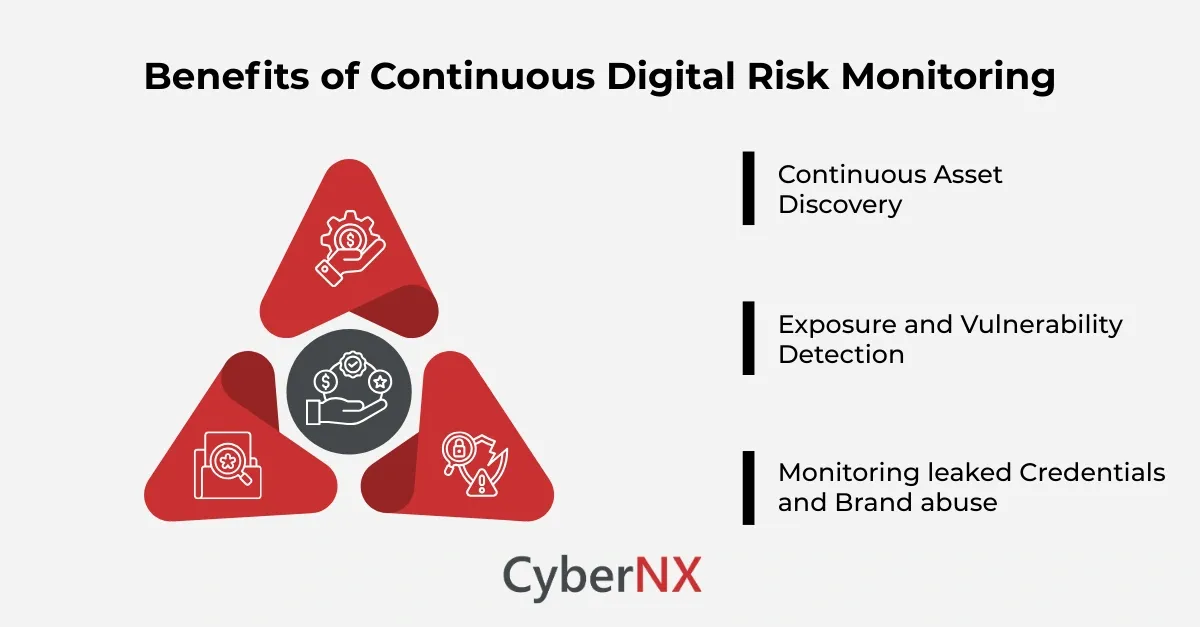
Security teams gain a clearer picture of their real attack surface. Key capabilities typically include asset discovery, exposure detection and threat intelligence monitoring.
1. Continuous asset discovery
Many organisations struggle with incomplete asset inventories. New services, domains or cloud workloads often appear without central documentation.
Continuous digital risk monitoring automatically discovers internet facing assets linked to the organisation. This includes domains, IP addresses, cloud resources and web applications.
The result is a more accurate and constantly updated asset map.
2. Exposure and vulnerability detection
Once assets are discovered, the next step is monitoring them for risk indicators.
Continuous digital risk monitoring identifies exposed services, outdated software, misconfigurations and other weaknesses visible to attackers.
Because monitoring is ongoing, security teams receive alerts soon after an issue appears rather than weeks later. This shortens response time and reduces potential impact.
3. Monitoring leaked credentials and brand abuse
Digital risk extends beyond infrastructure. Stolen credentials, fake domains and phishing campaigns also threaten organisations.
Continuous digital risk monitoring tracks these indicators across open web and dark web sources. Security teams gain early visibility into compromised credentials, impersonation attempts and brand misuse.
Early detection allows faster remediation.
Benefits for enterprise security teams
Adopting continuous digital risk monitoring shifts security from reactive to proactive operations. The advantages extend across several areas.
- Faster risk detection: Security teams identify exposures soon after they appear. This reduces the window of opportunity for attackers.
- Improved attack surface visibility: Unknown or forgotten assets often create serious vulnerabilities. Continuous discovery helps security teams regain control over their external footprint.
- Better prioritisation: Continuous digital risk monitoring highlights the most critical exposures first. Security teams can focus on risks that attackers are most likely to exploit.
- Reduced breach likelihood: When exposures are detected early, they can be resolved before attackers find them. Over time, this significantly lowers breach probability.
Integrating continuous digital risk monitoring
Continuous monitoring works best when integrated into a broader security programme rather than treated as a standalone tool.
- Security teams should begin by mapping their known external assets. From there, automated monitoring systems can expand visibility and track new exposures.
- Next, alerts must be linked with remediation workflows. When a new risk appears, teams should quickly assess severity and assign corrective action.
- Finally, monitoring insights should feed into broader risk management and vulnerability management programmes.
When combined with penetration testing, vulnerability assessments and security awareness programmes, continuous digital risk monitoring strengthens the entire security posture.
Conclusion
Periodic security scans still play an important role. They provide structured assessments and deep technical analysis. Yet they cannot keep pace with the speed of modern digital environments.
Threat actors continuously scan for exposed systems, leaked credentials and misconfigured services. Organisations that rely solely on scheduled assessments risk discovering issues too late.
Continuous digital risk monitoring closes this visibility gap. It enables organisations to track their external attack surface in near real time and respond quickly when risks appear.
At CyberNX, we help organisations gain this visibility while aligning monitoring with practical remediation workflows. The goal is simple. Detect exposures early. Resolve them quickly. Reduce the opportunity for attackers.
Speak with experts to explore how our digital risk monitoring services can strengthen your security posture.
Continuous digital risk monitoring FAQs
How is continuous digital risk monitoring different from vulnerability scanning?
Vulnerability scanning checks known systems for weaknesses at scheduled intervals. Continuous digital risk monitoring focuses on the external attack surface and monitors exposures as they appear across domains, assets and digital infrastructure.
Who should own continuous digital risk monitoring within an organisation?
Typically, security operations or risk management teams oversee it. However, insights should also be shared with IT operations, DevOps and compliance teams to ensure timely remediation.
Can continuous digital risk monitoring help with compliance requirements?
Yes. Many regulations require organisations to maintain visibility over their digital assets and manage vulnerabilities promptly. Continuous monitoring helps demonstrate ongoing oversight and risk management.
How often should organisations review digital risk monitoring findings?
Security teams should review alerts daily and integrate them into incident response workflows. Regular reporting to leadership helps track trends and prioritise remediation efforts.