CrowdStrike has gained strong traction. Its EDR platform offers deep endpoint insights. However, its Managed Detection and Response service goes further. It brings human expertise, continuous monitoring, and rapid response into one solution.
We often see organisations struggle with the decision between EDR and MDR. Both have value. But the right choice depends on your internal capabilities, risk exposure, and business priorities. Let’s break down when CrowdStrike MDR becomes the better option over an EDR-only deployment.
Understanding the difference between MDR and EDR
Before diving into scenarios, it helps to clarify what separates MDR from EDR.
EDR tools focus on detecting and investigating endpoint threats. They generate alerts, provide telemetry, and support response actions. However, they rely heavily on your internal team to interpret and act.
MDR, on the other hand, combines technology with expert-led monitoring and response. It is not just about tools. It is about outcomes. With CrowdStrike MDR, you get:
- 24/7 threat monitoring
- Expert-led threat hunting
- Guided or fully managed response
- Reduced alert fatigue
In simple terms, EDR gives you visibility, whereas MDR gives you action.
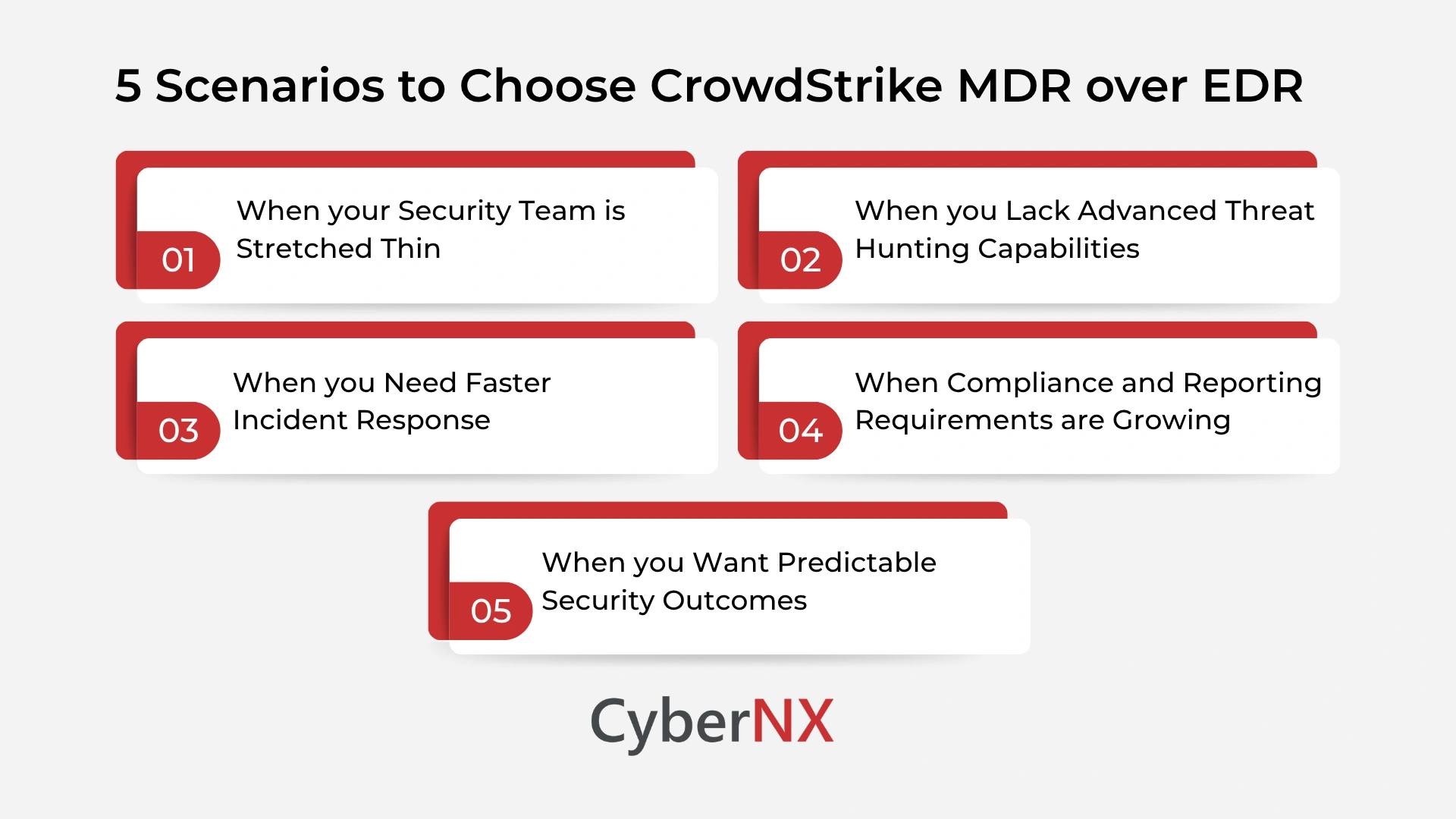
Furthermore, let’s see in which scenarios CrowdStrike MDR is a better option than EDR.
1. When your security team is stretched thin
Many organisations operate with lean security teams. Often, one team handles multiple responsibilities. Monitoring EDR alerts becomes just another task on an already long list. This creates delays. Alerts sit unreviewed. Real threats blend in with noise.
CrowdStrike MDR addresses this gap by acting as an extension of your team. Their analysts monitor, triage, and respond in real time. We have seen organisations reduce response times significantly once MDR is introduced. Instead of reacting late, teams stay ahead of threats. If your team is overwhelmed, EDR alone will not fix the problem. MDR will.
2. When you lack advanced threat hunting capabilities
EDR tools are powerful. But they require skilled analysts to unlock their full value. Threat hunting is not just about running queries. It involves understanding attacker behaviour, spotting subtle anomalies, and connecting multiple signals.
Without this expertise, organisations often miss early-stage attacks. CrowdStrike MDR includes proactive threat hunting driven by experienced analysts. These experts look beyond alerts. They search for hidden threats before they escalate.
This is especially useful for organisations without a mature security operations centre. If your team cannot actively hunt threats, MDR fills that gap effectively.
3. When you need faster incident response
Speed matters. Attackers move quickly once they gain access. Delays in response increase the impact. With EDR-only setups, response depends on internal workflows. Teams must investigate, decide, and act. This takes time.
CrowdStrike MDR accelerates this process. Their team can take immediate action, such as isolating endpoints or stopping malicious processes. This reduces dwell time. It also limits damage.
In our experience, organisations using MDR often contain incidents before they spread. That makes a significant difference during ransomware attacks. If response speed is critical for your business, MDR offers a clear advantage.
4. When compliance and reporting requirements are growing
Regulatory pressure is increasing across industries. Organisations must demonstrate continuous monitoring, incident response readiness, and audit trails.
EDR tools provide data. But turning that data into meaningful reports requires effort. CrowdStrike MDR simplifies this process. It delivers structured reporting, incident summaries, and clear visibility into security posture. This helps security leaders communicate effectively with stakeholders and auditors. It also ensures that compliance requirements are met without adding extra workload.
If your organisation faces strict regulatory demands, MDR can ease that burden.
5. When you want predictable security outcomes
One of the biggest challenges with EDR-only deployments is inconsistency. Results depend on team skill, availability, and processes. Even strong tools can underperform without the right people behind them.
MDR shifts the focus from tools to outcomes. With CrowdStrike MDR, you are not just deploying technology. You are investing in a managed service that delivers consistent monitoring, detection, and response. This creates predictability. Security becomes more reliable.
Conclusion
Choosing between EDR and MDR is not about which is better. It is about what your organisation needs right now.
EDR works well for mature teams with strong internal expertise. But many organisations struggle to keep up with the demands of modern threat landscapes. CrowdStrike MDR bridges this gap. It combines advanced technology with expert-driven operations. It reduces pressure on internal teams while improving response speed and threat visibility.
CyberNX is a partner of CrowdStrike. This gives us expertise to assess your current security posture and recommend the right approach. If you are evaluating CrowdStrike MDR or EDR, our CrowdStrike Consulting services will surely put you at an advantageous position and help you make the right decision and implement it effectively.
When should you choose CrowdStrike MDR over EDR FAQs
Is CrowdStrike MDR suitable for small security teams?
Yes. It is especially beneficial for small teams that lack resources for continuous monitoring and incident response.
Can MDR replace an internal SOC completely?
In some cases, yes. However, many organisations use MDR to complement their existing SOC rather than replace it entirely.
Does MDR reduce false positives compared to EDR?
Yes. MDR includes expert analysis, which helps filter out noise and focus on real threats.
How quickly can CrowdStrike MDR respond to incidents?
Response times are significantly faster than EDR-only setups, often in real time depending on the threat severity.