Social media reputation monitoring has shifted from just a marketing activity to a core cybersecurity function. A single post, leak, or impersonation attempt can trigger real business damage within hours. For security leaders, this creates a new challenge. You are now responsible for protecting perception, trust, and digital identity.
Over the past decade, social platforms have grown in scale and complexity. At the same time, threat actors have become more strategic. They exploit social channels to spread misinformation, launch phishing campaigns, and damage brand credibility.
In this blog, we do a deep dive into the changing dynamics of social media monitoring in the cybersecurity context and how organisations can adapt with a security-first approach.
How cybercriminals exploit social media platforms
Social media platforms have unmistakably become an integral part of running a business. However, it has also become powerful tools for modern attackers. Highprofile cases in recent years have shown how criminals exploit social networks’ features and human trust to inflict financial and reputational harm.
Here are few concrete examples:
- In July 2020 hackers used a phone spear‐phishing scheme to breach Twitter’s internal tools and hijack celebrity accounts, broadcasting a Bitcoin scam and stealing roughly $118,000.
- In another case, Chinese cyberfraudsters deployed SilentFade malware on user browsers to steal Facebook ad credentials and drain about $4 million from advertising budgets.
- August 2025 saw celebrity Instagram profiles hacked to pump a “meme coin” on Solana, which spiked to $900K market cap before crashing 98% (netting the attacker ~$49K).
These incidents illustrate common patterns (phishing, account takeovers, fake ads) and varied motivations like financial gain and propaganda. It is therefore important to assess and understand different attack types and review mitigation strategies and lessons.
Social media reputation monitoring must include technical controls such as multifactor authentication, limited admin access and humancentric measures like training and vetting contacts.
Classification of social media attack types
Socialmedia attacks can be grouped by technique and exploited feature. Common categories include:
1. Account Takeover (ATO)
Cyber criminals compromise legitimate accounts (via phishing or credential reuse) and use them for scams or propaganda. The British Army hack is the best example where hackers rebranded verified accounts for NFT scams).
Similarly, a UK ministers’ Twitter hack led to publishing of offensive or spam content). Celebrity Instagram hacks, as discussed earlier was done to pump crypto. Platform features abused include verified badges (lending credibility to scams) and follower networks.
2. Social engineering & phishing
Attackers use platform channels (DMs, comments) to trick users or employees. For example, the 2020 Twitter breach used phone spearphishing of Twitter staff to gain admin tool access.
Recent LinkedIn campaigns used convincing messaging to deploy malware. Attackers often gather personal info from LinkedIn, Twitter and other such platforms to craft believable lures.
3. Malware/Browser exploits
Hackers are now delivering malware via websites and ads with the aim of targeting social logins. Facebook’s SilentFade installed on users’ browsers stole access tokens without touching Facebook servers. Exploited features included advertising interfaces and API access. Plus, the malware used the Graph API to hijack ad campaigns.
4. Ad Fraud & Malvertising
This form of attack has gained traction in recent times. In this technique, hackers use social media platform ad systems to defraud companies and promote scams. Again, SilentFade’s is a prime example where operators ran unauthorized ads on compromised accounts.
There was a TikTok Business scheme, where criminals used hijacked accounts to serve malvertising. Attackers exploit ad targeting tools and payment methods attached to accounts.
5. Brand Impersonation and Spam
Creating fake profiles or hijacking brands to phish is also prevalent now. Scammers created phony Twitter/Instagram accounts or posts impersonating known entities (e.g. fake “Apple” bitcoin giveaway tweets, crypto lottery scams). Users often trust messages from recognized brands or friends and end up being scammed.
Mitigation and detection measures
As you can you see, it is now almost a must-have to include mitigation and detection capabilities in your social media reputation monitoring strategy. Here’s how you can undertake this initiative:
1.Platformlevel defences
First of all, social media companies must tighten internal controls. Twitter, for instance, responded to the 2020 breach by severely limiting access to internal tools and requiring stronger authentication for employee accounts. Facebook has sued known fraudsters and upgraded its adplatform monitoring after SilentFade.
Recommended platform measures include mandatory multifactor authentication for all accountmanagement staff, granular admin permissions, and anomaly detection on posts (e.g. alert on sudden highvalue Bitcoin giveaways). Instagram and Twitter now proactively scan for malicious links and unauthorized login locations.
2. Organisational policies
Companies and agencies should treat social channels as sensitive assets. Best practices include: never reusing social media passwords, enforcing MFA on official and employee accounts, and monitoring account activity for anomalies.
Employee training is crucial: staff should learn to verify any unusual request via social media (e.g. whether a colleague’s sudden request for credentials is genuine). Organizations can deploy userbehaviour analytics to flag unexpected posts (e.g. a government Twitter account suddenly tweeting giveaways).
For corporate accounts (like TikTok Business or LinkedIn Company Page), organizations should restrict the number of users with posting rights and keep strict logs of access.
3. Userlevel precautions
Individual users must harden their own accounts. Standard advice applies: use unique, strong passwords and enable MFA on every social platform. Beware of unsolicited messages or links, even from known contacts; verify outofband (a phone call) if asked for credentials. Users should regularly check for spoof or clone accounts impersonating their brand (report and take down any fakes immediately).
4. Technical detection
Deploy dedicated threat intelligence and social media reputation monitoring. Security teams can subscribe to socialmedia monitoring services to detect mentions of their brand or domain on shadier platforms. Antiphishing solutions and web filters should be extended to cover social links. Incident response plans should include social media scenarios: e.g. procedures to rapidly suspend or reclaim compromised accounts.
Lessons Learned and Best Practices
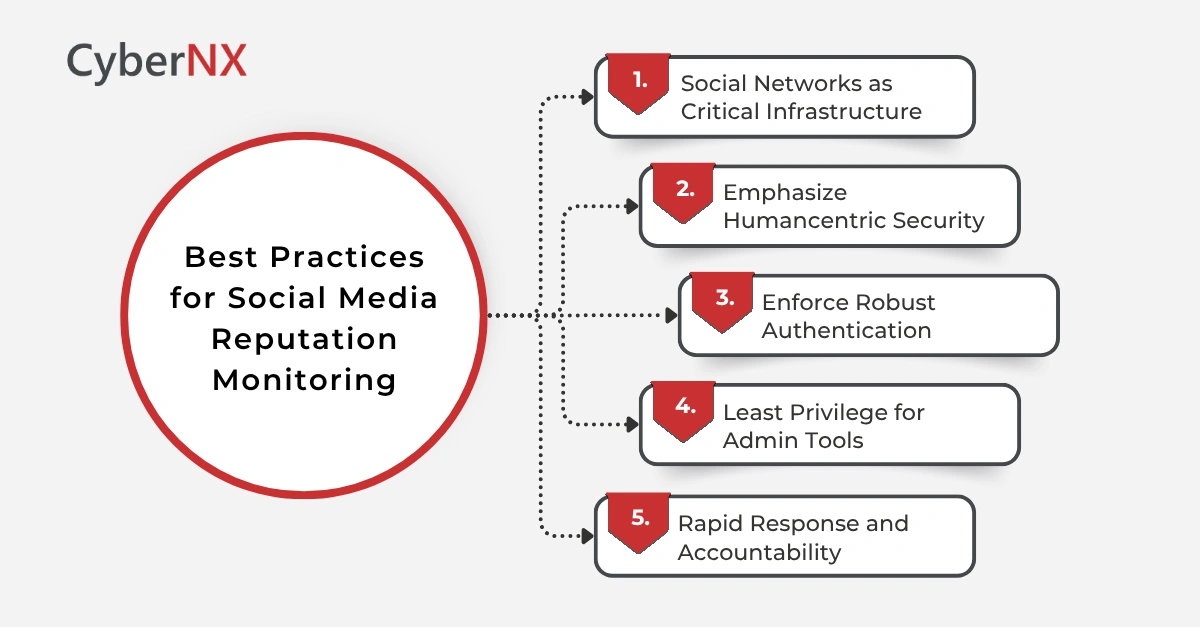
From these cases we derive several key lessons:
1. Social networks as critical infrastructure
Just as banks are regulated for security, social platforms must be assumed to be highvalue targets. Experts on the Twitter hack emphasize that social media reach “affects markets and national security.” Therefore, oversight to enforce strong cybersecurity on these networks is essential. Platforms should undergo regular security audits and comply with industry standards.
2. Emphasize humancentric security
No attack above relied on novel zeroday exploits. They exploited human trust. Experts note that attackers are now “hacking people” more than systems. Organizations must therefore deepen socialengineering defences: continuous training, periodic phishing tests even via LinkedIn/Twitter messages, and simulated “help desk” attacks to test staff vigilance.
3. Enforce robust authentication
The weakest link is often a single account without MFA. All cases with account takeover point to missing or bypassed multifactor. For example, Bitdefender observed that the British Army’s social team likely lacked 2FA. Mandatory MFA on all user and admin social media logins including privileged platform tools is non-negotiable.
4. Least privilege for admin tools
The Twitter 2020 hack succeeded because a midlevel employee’s credentials gave a path to powerful tools. Social media companies should adopt strict procedures.
For example, even when credentials are phished, employees should need secondary approvals to access account management tools. Segregating duties (so no one person has both publishing and admin rights) can limit damage.
5. Rapid response and accountability
Platforms must be able to quickly suspend anomalous activity. Public transparency and swift action build trust. Organizations should publicly report incidents and cooperate with law enforcement. In the discussed examples, the U.S. and UK authorities swiftly charged the Twitter hackers and Facebook litigated the SilentFade perpetrators.
Conclusion
The best defence is a layered one, where you combine technology like MFA, anomaly detection, policy (least privilege, incident playbooks), and people (training). Each attack teaches that trust on social media is easily exploited. So, the countermeasure has to be culture of “trust, but verify.” Organisations must adapt to this new reality. Threats are faster, more sophisticated, and more damaging than before.
A proactive, intelligence-led approach, in the current scenario, can make a real difference. With the right strategy, businesses can detect threats early, respond quickly, and protect both their brand and their stakeholders. At CyberNX, we collaborate with security leaders to strengthen monitoring capabilities and build resilient defence strategies. If you are looking to enhance your social media reputation monitoring, connect with our experts today to know our full range of digital risk protection capabilities.
Social media reputation monitoring FAQs
How is social media reputation monitoring different from traditional threat detection?
It focuses on external threats like impersonation, phishing, and misinformation. Unlike internal security tools, it tracks risks emerging on public platforms that can impact brand trust.
What are early signs of a social media cyber attack?
Watch for fake accounts, sudden spikes in mentions, unusual posts, or suspicious links shared from official profiles. These often signal ongoing or planned attacks.
How can social media monitoring fit into security operations?
It can be integrated with threat intelligence and incident response workflows. Alerts should be treated like any other security event for faster action.
Why is employee awareness important in social media security?
Most attacks exploit human behaviour, not just systems. Training employees to spot and report suspicious activity helps prevent account compromise and wider damage.