In 2026, some of the most damaging cyber incidents are not just breaches of infrastructure but breaches of trust. This is because harmful interactions aren’t happening only inside your network but outside. Look at these examples:
- Your customer reaching out to what appears to be your official support account on LinkedIn.
- A fake Instagram page using your brand name promoting a “limited-time offer”.
- A direct message shares a login link that looks legitimate.
All of these interactions can severely impact your business.
Attackers have shifted their focus to environments where customers already trust your brand and social media has become one of the most exploited channels. This is why social media monitoring has become so important now.
For CISOs and security leaders, the goal is not just visibility, but early detection of impersonation, fraud and any other harmful activity before it reaches customers.
What is social media monitoring?
It is the constant process of analysing and responding to brand-related activity across social platforms. It includes identifying malicious behaviour, detecting impersonation attempts and understanding how attackers exploit brand trust in digital conversations.
In a security context, social media monitoring focuses on identifying risks early, before they escalate into customer-facing incidents.
Social media platforms were never designed with enterprise security in mind. They were built for engagement, speed and accessibility. These same characteristics make them highly attractive to attackers.
A fake profile can be created in minutes, and a phishing link can spread within seconds. This shift has fundamentally changed how companies must think about risk.
Security is no longer confined to just endpoints or apps. It now extends to every interaction your brand has with customers online. This is where social media monitoring plays a critical role. It provides visibility into environments where traditional security tools have no reach.
How modern social media threats unfold
Most organisations assume social media threats are isolated incidents. But in reality, they follow structured attack patterns.
An attacker may begin by creating a lookalike account using your brand identity. This account starts engaging with customers, often targeting those who publicly raise queries or complaints.
Once trust is established, the attacker might redirect the conversation and move the user to a private channel. They might share a false or harmful link or even request sensitive information. And at absolutely no point does the attacker need to breach your systems. The entire attack happens in plain sight, yet outside your control.
This is why social monitoring must focus not just on detection, but on understanding behaviour patterns and intent.
Common threats detected
Attackers keep getting more creative with their techniques and attack methods continuously evolve. But there are some patterns that are consistent across all the industries:
- Impersonation and fake accounts: Attackers replicate brand profiles or executive identities to build trust and initiate fraudulent conversations.
- Phishing through social channels: Links shared via comments, messages or posts redirect users to fake login pages or malicious sites.
- Fraudulent customer support: Fake support accounts respond faster than official channels, and in this way, they exploit urgency and trust.
- Brand misuse in campaigns: Attackers run fake promotions or ads using brand identity to mislead customers and collect payments.
These threats highlight why social media monitoring must be continuous and intelligence-driven.
Why traditional monitoring approaches fail
Many organisations still depend on manual tracking or marketing-led monitoring which can create a dangerous gap. Marketing teams can identify brand mentions, but they are not equipped to validate threats or investigate malicious behaviour. Security teams, on the other hand, lack visibility into social platforms. The result is scattered awareness.
Threats remain undetected until customers report fraud or reputational damage becomes visible. Effective monitoring demands a unified approach that combines visibility and response within a security framework.
How to build an effective social media monitoring strategy
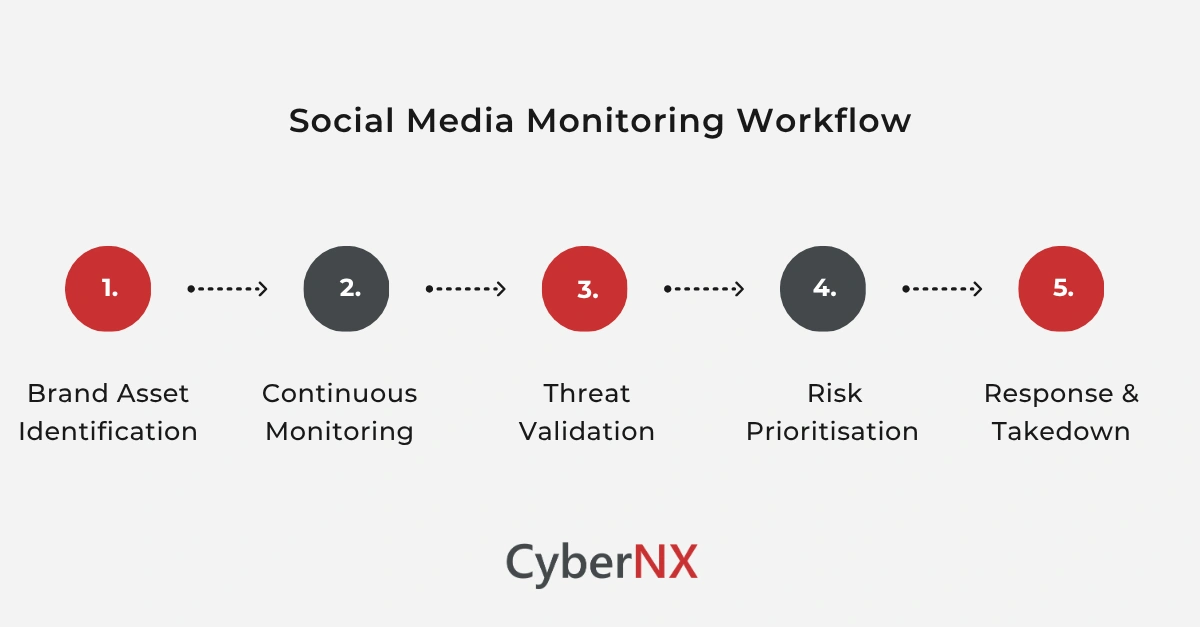
A structured approach helps organisations move from reactive detection to proactive defence:
Identify brand assets and exposure/Brand asset identification
Understanding your digital footprint is the foundation. Without clarity on official accounts, regional profiles and overall presence, detecting impersonation becomes difficult.
Monitor continuously across platforms/ Continuous monitoring
Threats can arrive at any point of the day. Continuous monitoring makes sure that threats are detected as fast as possible.
Validate and analyse threats/ Threat validation
Not every signal is malicious. The ability to distinguish between noise and real risk is what defines effective monitoring.
Prioritise based on impact/ Risk prioritisation
Security teams must focus on threats that directly affect customers, financial risk, or brand trust.
Execute rapid response/ Response and takedown
Detection without action is of no use. Fast takedowns and response measures are extremely critical to minimise impact.
The real business impact of poor social media monitoring
The results of weak monitoring are not immediate – but they are always cumulative. Customer fraud incidents increase gradually and trust erodes over time. Support teams face rising volumes of complaints linked to issues they cannot trace internally. In many cases, organisations realise the scale of the problem only after patterns begin to appear.
This delayed visibility is one of the biggest risks in modern cybersecurity. Effective social media monitoring changes this by providing early signals and allows organisations to act before incidents scale.
Conclusion
Social media has become one of the most active and vulnerable layers of the enterprise attack surface. Attackers are not trying to break in anymore. They are trying to blend in – impersonating brands and targeting customers directly.
Without good social media monitoring, these threats remain invisible until they cause real damage.
At CyberNX, we provide digital risk protection services that help uncover threats at the source to disrupt abuse before it reaches business or the public eye. We work alongside your team to address your key challenges like brand impersonation and phishing abuse. If you are looking to strengthen your social media monitoring strategy, connect with us to build a strong defence against modern social media threats.
Social media monitoring FAQs
What is social media monitoring?
Social media monitoring is the process of tracking and analysing brand-related activity on social platforms to detect engagement, risks, and potential threats.
What is social media monitoring used for in cybersecurity?
It is used to detect impersonation, phishing campaigns, fraud, and brand misuse across social platforms.
How does social media monitoring help prevent fraud?
It identifies malicious accounts and campaigns early, allowing organisations to take action before customers are affected.
Which industries need social media monitoring the most?
Banking, fintech, e-commerce, healthcare, and technology sectors benefit significantly due to high exposure to customer-facing threats.
How often should social media monitoring be performed?
Monitoring should be continuous because threats can emerge at any time.