Ransomware is a devastating malware around, affecting businesses across the world. The dangerous aspect of ransomware is that it rarely begins with an encryption event. Long before systems are locked or data appears on a leak site, attackers discuss tools, trade stolen access, and test new campaigns in hidden corners of the internet.
This activity often happens in areas most organisations never see. Non indexed forums, private messaging boards and hidden services reachable only through specialised browsers. These spaces form a critical part of the cybercrime economy.
Only security teams that monitor dark web and deep web gain an early warning advantage. Ransomware intelligence from the dark web helps organisations track emerging threats before they become incidents. It reveals attacker behaviour, infrastructure, and targets while campaigns are still forming. This intelligence provides something extremely valuable: time. Precious time to patch weaknesses, revoke compromised access, and strengthen defences before a hacker strikes.
In this article, we explore how ransomware intelligence from the dark web works, which environments analysts monitor, and what signals security teams should prioritise.
Dark web: where ransomware intelligence originates
The dark web is often misunderstood. It is not a single location, but a collection of networks and services designed to provide anonymity.
Threat actors favour these environments because they reduce attribution risk and make takedowns difficult. As a result, many stages of ransomware operations unfold here.
To gather ransomware intelligence from the dark web, analysts monitor several types of infrastructure.
1. Hidden services on anonymity networks
Many ransomware groups operate leak portals and communication sites on anonymity networks such as Tor hidden services.
These websites do not appear on traditional search engines and cannot be accessed through standard browsers. Analysts use specialised browsers such as Tor Browser to reach these domains.
Typical intelligence sources include:
- Ransomware leak sites publishing victim data
- Negotiation portals used for ransom discussions
- Announcement pages used by ransomware groups
- Affiliate recruitment pages
Monitoring these sites helps security teams identify newly targeted industries, regions, and companies.
For example, many ransomware groups maintain public victim lists. Analysts track when organisations appear on these pages, often before media coverage begins.
2. Underground forums and cybercrime marketplaces
Another major source of ransomware intelligence comes from underground discussion forums. These forums act as meeting places for threat actors. They are used to exchange techniques, recruit affiliates, and trade compromised access. Common discussion topics include:
- Initial access broker listings
- Vulnerability exploitation methods
- Privilege escalation techniques
- Network access for sale
- Malware builder tools
Access brokers are particularly important signals. These actors sell entry points into corporate networks through VPN credentials, RDP access, or web application vulnerabilities.
When access listings mention specific industries or geographic regions, defenders gain early clues about active targeting patterns.
3. Ransomware affiliate recruitment channels
Modern ransomware groups often operate under a Ransomware-as-a-Service (RaaS) model.
In this model, core developers create the ransomware platform while affiliates conduct attacks. Recruitment and affiliate management frequently occur on dark web forums.
Recruitment posts often reveal:
- Commission structures for affiliates
- Supported attack tools
- Preferred targets such as healthcare or finance
- Restrictions such as avoiding certain countries
Tracking these announcements provides valuable intelligence about how ransomware ecosystems evolve. It also reveals when new ransomware families emerge.
4. Data leak sites and extortion portals
One of the most visible elements of ransomware intelligence from the dark web is the monitoring of leak sites. These portals publish stolen data when victims refuse to pay. However, leak sites provide more than just victim names. They often contain:
- Sample stolen documents
- Evidence of data exfiltration
- Infrastructure details
- Timeline of attacks
- Negotiation status
Analysts track these portals continuously. New victims often appear here before official disclosures. This intelligence helps organisations identify trends across industries and regions.
Technical access methods used by dark web intelligence teams
Accessing the dark web safely requires specialised tools and strict operational practices. Security analysts do not simply open hidden sites from a corporate network. They use controlled environments designed to prevent exposure and maintain anonymity.
1. Specialised browsers for hidden services
Most dark web intelligence collection begins with specialised browsers. The most widely used is Tor Browser, which routes traffic through multiple encrypted nodes. This process hides the user’s location and prevents direct tracing. Other privacy networks sometimes monitored include:
- I2P networks used for peer-to-peer hidden services
- Onion service mirrors used by ransomware leak portals
- Private access gateways shared among cybercrime communities
Analysts rely on these tools to reach sites that are otherwise unreachable from standard internet infrastructure.
2. Non indexed forums and invite only communities
Many high value ransomware discussions occur in communities that are intentionally difficult to join. These environments often include:
- Invite only forums
- Reputation based cybercrime marketplaces
- Encrypted chat channels
- Closed affiliate communities
Security researchers often require months to establish credible identities within these ecosystems. Once inside, analysts can observe discussions related to ransomware tooling, exploits, and victim targeting strategies.
3. Automated monitoring and crawler infrastructure
Manual browsing alone cannot scale to the size of the dark web ecosystem. Threat intelligence teams therefore deploy specialised crawlers that monitor known ransomware infrastructure.
These systems track:
- New leak site victims
- Newly registered onion domains
- Changes to ransomware group portals
- Forum posts mentioning vulnerabilities or companies
Automation allows analysts to detect signals quickly and correlate them with internal threat intelligence data.
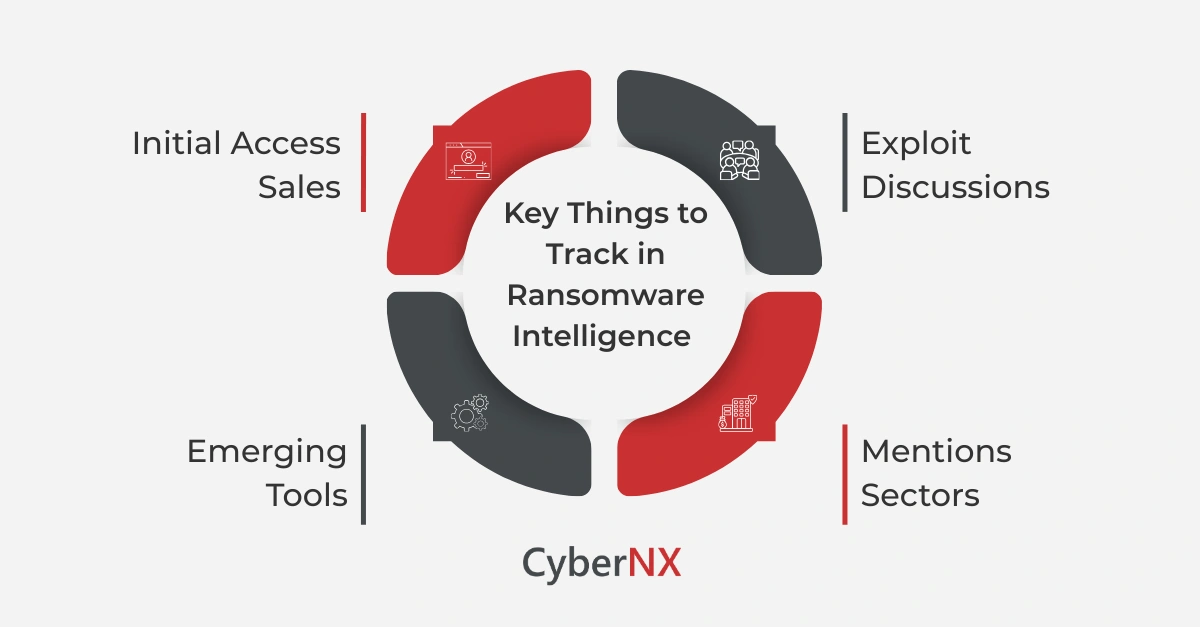
What organisations should track in ransomware intelligence
Collecting ransomware intelligence is only valuable when it leads to actionable insights. Security teams typically prioritise several categories of intelligence.
1. Initial access sales
Listings for compromised corporate access are among the most important signals.
Access brokers frequently advertise:
- VPN credentials
- RDP access
- Citrix gateways
- Remote management platforms
- Cloud tenant credentials
When a company appears in such listings, it often indicates an active compromise. Early detection allows organisations to rotate credentials, patch exposed services, and investigate intrusion activity.
2. Exploit discussions
Ransomware operators constantly search for exploitable vulnerabilities. Forums often reveal which vulnerabilities are being weaponised before large scale attacks begin. Monitoring discussions around enterprise software such as VPN appliances, remote desktop gateways, backup management systems and identity platforms help defenders prioritise patching and mitigation.
3. Mentions of specific companies/sectors
Threat actors often discuss targets before launching attacks. These discussions may include:
- Requests for network access within a specific sector
- Requests for insiders willing to sell credentials
- Interest in companies with large data stores
- Discussions about vulnerabilities in industry platforms
Tracking these signals helps security teams anticipate campaigns against their sector.
4. Emerging ransomware groups/tools
The ransomware ecosystem changes constantly. New groups appear, rebrand, or split into rival factions. Dark web monitoring helps analysts detect:
- New ransomware strains
- Affiliate programmes
- Updated encryption tools
- New extortion strategies
These signals allow organisations to update threat models and detection strategies.
Why ransomware intelligence matters for security leaders
Ransomware intelligence from the dark web shifts the focus earlier in the attack lifecycle. It allows security teams to detect threats during stages such as:
- Access brokerage
- reconnaissance
- tool development
- affiliate recruitment
- victim selection
This intelligence strengthens several areas of security operations.
- First, it improves threat hunting. Analysts know what techniques attackers are discussing and can search internal logs for related activity.
- Second, it improves patch prioritisation. Security teams understand which vulnerabilities attackers actively exploit.
- Third, it enhances incident response readiness. Organisations can prepare for emerging ransomware families before attacks escalate.
Our experience working with enterprise security teams shows a simple pattern. The earlier you see attacker activity, the more options you have to stop it.
Conclusion
Ransomware attacks rarely happen without warning. Clues appear long before systems are encrypted. Hidden forums discuss vulnerabilities. Access brokers advertise compromised networks. Leak portals reveal patterns of targeting. Monitoring these environments provides powerful early insight.
Ransomware intelligence from the dark web helps organisations detect threats earlier, understand attacker behaviour, and strengthen defences before damage occurs.
At CyberNX, we transform threat intelligence into practical action. From dark web monitoring to vulnerability assessments and incident response readiness, we help organisations stay one step ahead of ransomware operators.
If you want to understand how dark web monitoring can strengthen your security strategy, our team is ready to support you.
Ransomware intelligence for dark web FAQs
How do security teams safely access dark web ransomware infrastructure?
Security teams use isolated research environments, specialised browsers such as Tor, and monitored networks to access hidden services safely. This prevents attribution and protects corporate systems.
How early can dark web intelligence reveal ransomware attacks?
In many cases, signals appear weeks before attacks occur. Access brokers may advertise compromised networks long before ransomware operators deploy payloads.
Can organisations detect if their company appears on dark web forums?
Yes. Dark web monitoring platforms and threat intelligence teams track mentions of company domains, credentials, and leaked data across underground forums and marketplaces.
Is dark web intelligence useful for smaller organisations?
Yes. Many ransomware groups target mid-sized companies because they often lack dedicated monitoring. Intelligence monitoring helps detect early signals of targeting.