The IRDAI cybersecurity guidelines 2026 is a much-need push amidst an ecosystem where cyberthreats are swelling in numbers. It gives a better view into how security must be governed, owned, and executed across insurance organisations. It essentially signals a shift towards accountability, operational discipline, and measurable outcomes.
Insurance firms with complex systems already operate in a high-risk environment. Sensitive customer data being a major attraction for cybercriminals. These guidelines offer a structured process and stronger technical controls for better security.
Organisations that act early can build security programmes that are not only compliant but resilient and scalable. Let us break down what truly matters.
Leadership accountability is now clearly defined
One of the most noticeable changes is how responsibilities are distributed across leadership roles. There is less ambiguity and expectations are now explicit.
1. The board steps into cybersecurity ownership
The board now must:
- Allocate a cybersecurity budget aligned to risk appetite
- Approve timelines for closing audit findings
- Ensure remediation happens within 12 months
This shifts cybersecurity from an operational concern to a strategic priority. Budget discussions will now require stronger justification backed by risk context.
2. The CISO gains independence and deeper responsibility
The reporting structure has changed for a reason. CISOs now must not report to the Head of IT and cannot carry business targets. Instead, they need to own scenario-based incident response planning and must ensure alignment with CERT-In guidelines
This separation removes conflict of interest. It also strengthens decision-making during incidents, where speed and clarity matter most.
3. The CTO becomes accountable for execution
The CTO’s role is now tightly linked to implementation. Responsibilities include aligning IT processes with security standards defined by the CISO. Plus, fixing vulnerabilities identified through audits. This closes a long-standing gap. Security defines the “what”. Technology ensures the “how”.
Business leaders are now part of the security chain. Functional heads and business owners are no longer on the sidelines. They must ensure teams follow security policies and work with the CISO to address unit-specific risks
This change recognises a simple truth. Many risks originate within business workflows, not just IT systems.
Operational discipline is no longer flexible
The updated IRDAI cybersecurity guidelines 2026 introduce stricter expectations around governance and execution. Security decisions now require clear ownership, structured approvals, and defined timelines.
1. Exception management becomes structured
Exceptions often start small but tend to linger. The new framework changes that. Approval timelines now depend on the duration of the exception:
- Up to three months requires approval from the CISO
- Between three and twelve months requires the Risk Management Committee
- Beyond twelve months requires Board-level approval and reassessment
This creates accountability at every level. More importantly, it prevents long-standing exceptions from becoming hidden risks.
From our experience, organisations often underestimate how quickly temporary exceptions become permanent vulnerabilities. A structured process forces regular review and reduces this risk significantly.
2. Alignment with the DPDP Act is now mandatory
The integration with the Digital Personal Data Protection Act is a major shift. Insurance organisations must now implement both technical and organisational measures to protect personal data. This includes:
- Stronger controls for data handling
- Clear ownership of data protection responsibilities
- Better visibility into how data flows across systems
For many firms, this will require revisiting data governance frameworks. Data mapping, classification, and access control will need closer attention. Understanding where your sensitive data lives and how it moves is now important. Without that clarity, even the best security tools fall short.
3. Audit timelines are tighter and more transparent
The guidelines introduce stricter timelines for audit reporting. Insurance intermediaries must:
- Submit compliance reports within 30 days of audit completion
- Ensure audits are conducted by CERT-In empanelled firms
This improves transparency across the ecosystem. It also reduces delays that often weaken risk visibility. In practice, this means teams must be audit-ready at all times. Documentation, evidence collection, and remediation tracking need to be continuous rather than reactive.
Technical controls are more practical and outcome-driven
The guidelines move away from checkbox compliance. The focus is now on real-world effectiveness.
1. Infrastructure segregation is now expected
Organisations must ensure clear separation across networks, databases and infrastructure layers. This applies especially to group entities. The goal is simple. Limit lateral movement during a breach.
If one system is compromised, the attacker should not be able to move freely across the environment.
Many organisations assume segmentation is already in place. But in reality, gaps often exist. Reviewing architecture with an attacker mindset can reveal these blind spots.
2. VAPT moves towards deeper testing
There is a clear evolution in VAPT expectations under the new guidelines.
Organisations must now:
- Shift from black box to grey or white box testing
- Conduct testing every six months
- Engage CERT-In empanelled auditors
This reflects how attackers actually operate. They rarely start with zero knowledge. Instead, they exploit partial information to find deeper vulnerabilities.
Testing in non-production environments is still allowed. However, those environments must closely mirror production. Any differences must be formally approved by the Information Security Risk Management Committee.
This is a crucial change. Superficial testing often misses real risks. Deeper testing provides actionable insights that improve security posture.
3. Cloud security expectations are stricter
Cloud adoption is growing fast across the insurance sector. The guidelines respond with stronger controls. Organisations must ensure:
- Use of MeitY empanelled cloud providers
- Valid STQC audit status
- Contractual assurance for complete data removal upon exit
These requirements address a key concern: Vendor risk. Data does not just disappear when contracts end. Without proper controls, residual data exposure remains a serious threat.
4. Preparing for future cryptographic risks
The guidelines introduce early steps towards post-quantum readiness. Organisations must:
- Maintain a clear inventory of cryptographic assets
- Prepare for future transitions in encryption standards
At the same time, resilience expectations are increasing.
- Immutable backups are now required
- Failover systems must be in place for critical infrastructure
These measures ensure that recovery remains possible even during severe attacks such as ransomware. Many firms already have backup strategies. However, not all backups are truly resilient. Testing recovery under realistic conditions is essential.
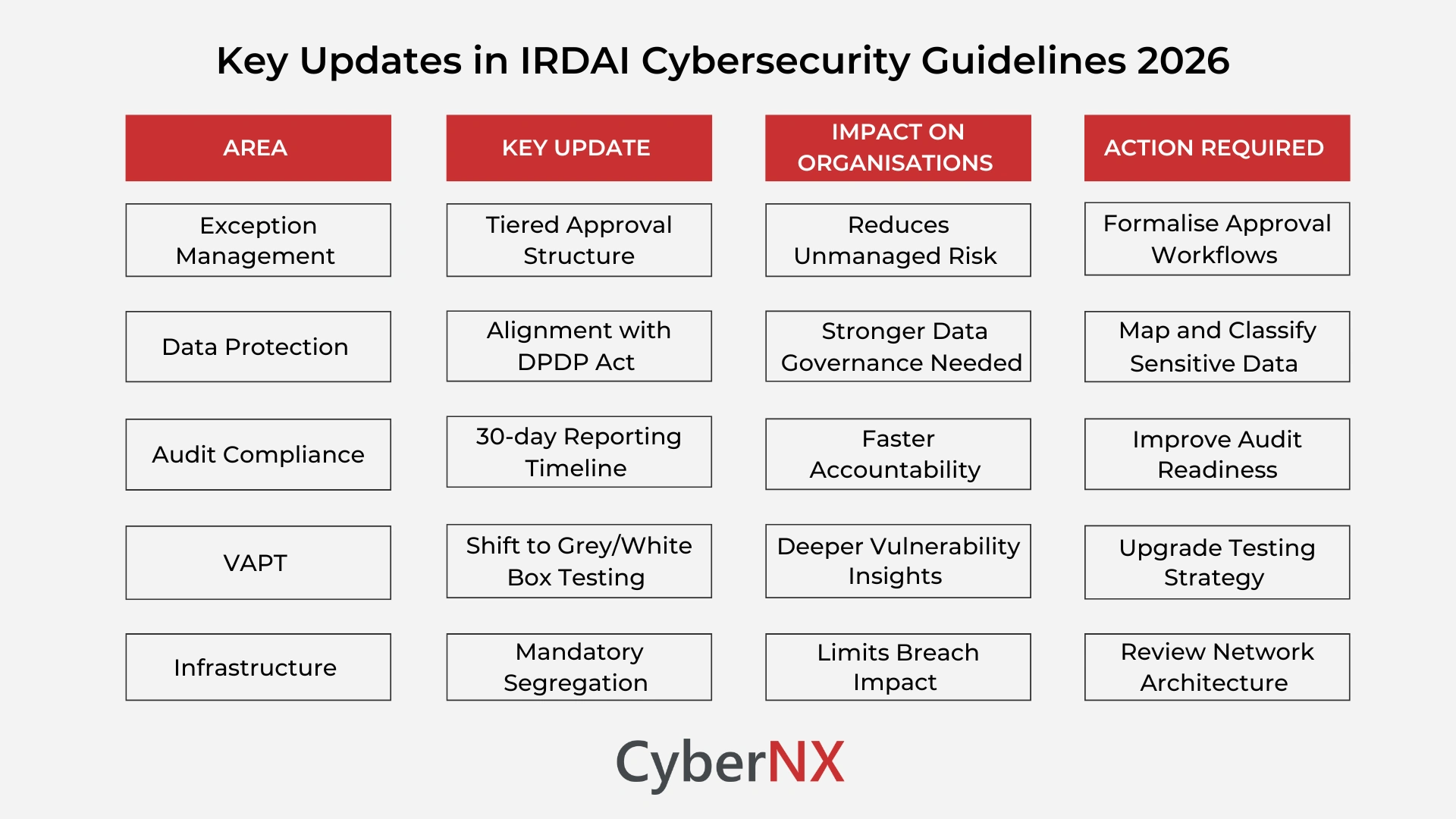
IRDAI cybersecurity updates at a glance
Below is a structured view of the most critical updates in the IRDAI cybersecurity guidelines 2026:
Key takeaways for security leaders
The guidelines require a shift in how security is approached. It is no longer about isolated controls. It is about integration across governance, operations, and technology. Security leaders should focus on five priorities:
- Strengthen communication with the Board. Translate risk into business impact
- Review reporting structures to ensure CISO independence
- Build tighter coordination between security and IT teams
- Formalise exception management processes with clear ownership
- Reassess VAPT strategies to meet new depth and frequency requirements
- Validate cloud vendor compliance and contractual safeguards
- Build visibility into cryptographic assets and dependencies
- Test backup and recovery processes in realistic scenarios
Each of these areas contributes to a stronger, more resilient security posture.
Conclusion
The IRDAI cybersecurity guidelines 2026 bring much-needed clarity. They set clear expectations across governance, operational discipline, and technical controls.
For many organisations, the real challenge lies in consistent implementation. Policies alone are not enough. Execution across teams and systems is what drives real impact.
This is where a structured and practical approach makes a difference. Small, focused improvements across key areas can significantly strengthen overall security.
At CyberNX, we work closely with organisations to translate regulatory requirements into actionable security strategies. From VAPT enhancements to cloud security validation, we help teams move from compliance to confidence.
IRDAI cybersecurity guidelines 2026 FAQs
How often should VAPT be conducted under the 2026 IRDAI guidelines?
VAPT must be conducted every six months, with a shift towards more in-depth grey box or white box testing approaches.
What is the role of the DPDP Act in these guidelines?
The DPDP Act mandates stronger data protection practices, requiring organisations to implement structured governance, visibility, and accountability for personal data.
Are cloud providers required to meet specific certifications?
Yes, cloud providers must be empanelled by MeitY and maintain valid STQC audit status, along with clear data exit provisions.
What are immutable backups and why are they important?
Immutable backups cannot be altered or deleted. They ensure data recovery remains possible even during ransomware or destructive attacks.