Asking a software vendor for an SBOM sounds simple. But in practice, it often turns awkward very quickly.
Most buyers assume an SBOM already exists. Most vendors assume nobody will ever ask. The result is a short email chain full of delays, vague assurances and eventually a PDF that tells you very little. Or nothing at all.
If you are responsible for managing third party risk, the goal is not just to request an SBOM. It is to get one that is current, usable and tied to the product you actually run. That requires a bit more care than sending a line item in a questionnaire.
This is what tends to work.
Start by being clear about why you want it
It helps to be clear with yourself before you approach anyone else.
An SBOM is not a vulnerability report. It does not tell you what is exploitable. It does not guarantee secure code. All it does is it gives you visibility. That is all. But visibility is powerful when time is short.
When Log4j landed, many organisations spent days emailing suppliers a single question. Are we affected? The suppliers who could answer quickly were not guessing. They had an inventory of components. Everyone else was scrambling.
That context matters because vendors often assume you are asking for something you do not fully understand. Being precise about your intent avoids a lot of noise later.
You are not asking them to justify their development practices. You are not asking for source code. You are asking for a component inventory tied to the product you run, so you can assess impact when new issues emerge.
Keep that framing in mind. You will need it.
Lead with a practical explanation, not a standard
The fastest way to slow an SBOM request is to anchor it in abstract requirements.
If the first sentence mentions regulation, frameworks, or industry mandates, expect the reply to involve legal, procurement and a review cycle that stretches on for weeks. Even if you are subject to those requirements, leading with them rarely helps.
A more effective approach is operational and plain.
You manage vulnerability response. You track advisories. When a new issue is published, you need to know whether your environment includes the affected component. The SBOM helps you answer that question without guesswork.
That explanation resonates with engineering teams. It also reassures commercial contacts that you are not building a compliance case against them.
Be explicit about format from the outset
If you do not specify format, you are inviting disappointment.
Many vendors will respond with whatever they think an SBOM looks like. That might be a static PDF. Sometimes a spreadsheet. Occasionally a marketing document with a reassuring title and very little substance.
None of these are particularly useful when you need to match components against vulnerability feeds at speed.
Be clear, early, and calm. Ask for a machine readable SBOM in a recognised format like SPDX or CycloneDX. Do not over explain. Do not justify it as a preference. State that this is what your internal tooling consumes.
This small detail does a lot of work for you. Vendors who already generate SBOMs will recognise the request immediately. Vendors who do not will reveal that quickly as well.
If they push back, ask what format they can provide and how it is generated. That answer tells you more than the document itself.
Anchor the SBOM to a specific product version
One of the most common problems with vendor SBOMs is vagueness.
You receive a file that claims to cover the product, with no reference to version, build or release date. It might technically be accurate at some point in time. You just have no idea when.
An SBOM without version context is almost useless during an incident. When a vulnerability advisory drops, the first question is always whether the affected component exists in the version you are running. If the SBOM cannot answer that, it has failed its primary purpose.
When you make the request, tie it explicitly to the version deployed in your environment. If possible, reference the build or release identifier. Ask how often it is regenerated and what triggers an update.
This is also where you quietly learn whether the SBOM is produced automatically as part of the build pipeline or assembled manually when requested. Automated generation is not perfect, but it is far more reliable than a document built once and forgotten.
Expect legal concerns and do not dismiss them
Even vendors with mature security practices often hesitate because of legal anxiety.
There is a constant fear that sharing an SBOM exposes intellectual property or increases liability. In reality, most SBOMs list open-source components and versions. They rarely reveal anything exclusive. But fear does not always track reality.
Try not to argue this point with the vendor. Involve your own legal team early and align on a clear position. A short statement clarifying that the SBOM is used for security risk management, not reverse engineering, can make a significant difference.
Sometimes an NDA is unavoidable. Whether that is acceptable depends on your organisation’s stance. What matters is deciding deliberately, not drifting into an agreement without understanding the implications.
If a vendor refuses outright on legal grounds, that is still useful information. It tells you how they are likely to behave when you need fast answers during an incident.
Treat silence and delay as data
One of the most revealing aspects of an SBOM request is not the document you receive, but the time it takes and the friction involved.
Vendors who understand their supply chain can usually respond quickly, even if the answer is that they are still maturing their approach. Vendors who do not often go quiet, send holding messages or redirect the conversation repeatedly.
Do not chase endlessly without noting the pattern. Delay itself is a risk signal. It suggests that if a critical vulnerability appears, you may face the same silence when it matters most.
This is not about punishing suppliers. It is about understanding the operational reality of the relationship.
Validate what you receive, lightly but deliberately
When an SBOM finally arrives, resist the urge to file it away and move on.
You do not need to conduct a deep technical audit. You do need to check whether it makes sense.
Look at the component list. Does it align with the technology stack you expect? For example, if the product is Java based, are common Java libraries present? If it is a web application, do the frameworks line up with what you have observed?
Compare it against a recent high-profile vulnerability that affected similar software. Does the SBOM reflect the presence or absence of that component? If everything appears magically unaffected, ask why.
An SBOM that never changes across versions might be a red flag. Software evolves. Dependencies shift. A static document usually means it is not embedded in the development process.
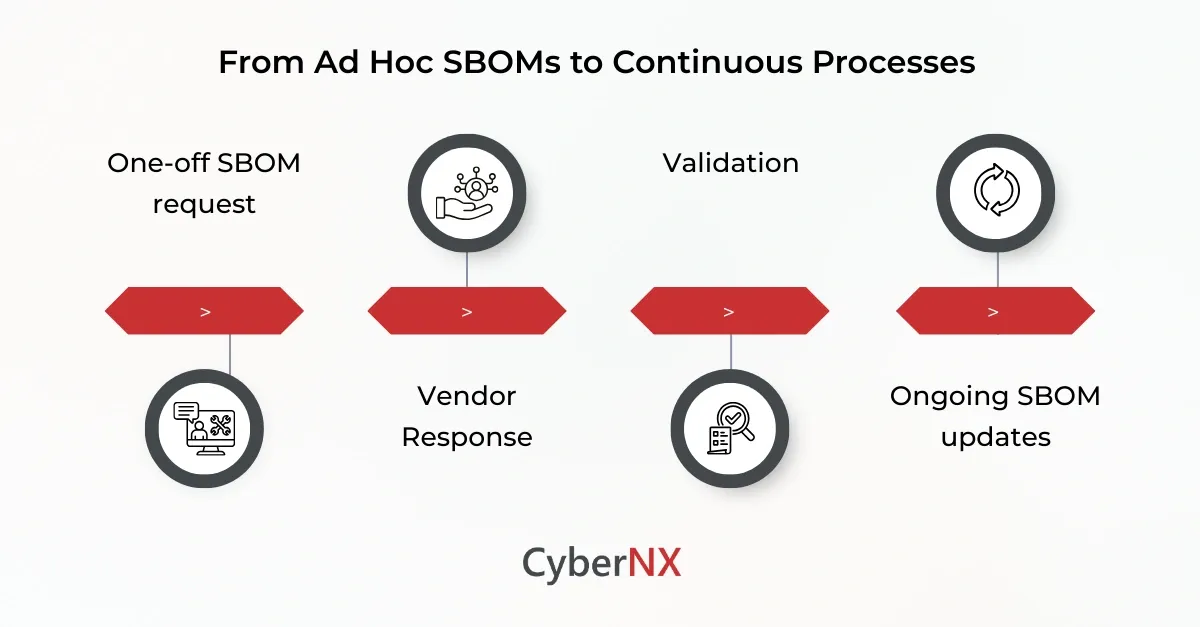
Move from one off request to standing expectation
The real value of an SBOM comes when it stops being a special request.
If the vendor relationship is ongoing, set expectations around updates. Agree when a new SBOM will be provided. Tie it to major releases, significant dependency changes or a regular cadence that fits their development cycle.
This does not need to be formal or heavy handed. A simple shared understanding is often enough.
Vendors who take supply chain security seriously usually welcome this clarity. It removes ambiguity and reduces last minute pressure when issues arise.
Those who resist every follow up or treat each request as exceptional are signalling a different level of maturity.
Use the process as a maturity indicator
Over time, SBOM conversations become a useful filter.
Vendors who can generate accurate, timely SBOMs tend to have better visibility into their own environments. They are usually faster during incident response. They communicate more clearly under stress.
Vendors who struggle often struggle elsewhere too. Not because they are negligent, but because their processes have not caught up with the reality of modern software dependency chains.
This does not mean you drop them immediately. It does mean you factor that reality into risk decisions, compensating controls, and escalation planning.
Conclusion
Getting an SBOM from a third party is rarely smooth the first time. It involves education, reassurance and sometimes friction. That is normal.
What matters is approaching it as a practical risk management discussion, not as a compliance demand. Speak in the language of incidents and impact. Avoid abstract mandates unless you genuinely need them.
Over time, these conversations get easier. They also change the nature of supplier relationships. Transparency becomes expected rather than exceptional.
At CyberNX, we provide an in-house built, AI-enabled SBOM management tool that enables end-to-end automation from collection to analysis, ensuring complete visibility into software components. This tool helps in vendor management by collecting and managing third-party vendor SBOMs with secure vendor portal.
Talk to our experts today to know more about our SBOM capabilities and design an SBOM process that fits your ecosystem and needs.
How to get an SBOM from your third-party software vendor FAQs
Is it mandatory for vendors to provide an SBOM?
SBOM requirements depend on regulatory, contractual and industry-specific expectations. Including SBOM clauses in contracts ensures vendors provide transparency and support supply chain risk management.
How often should a third-party vendor update their SBOM?
SBOMs should be updated whenever a new software version, patch or dependency change is released. For critical systems, continuous or release-based SBOM updates are preferred over one-time delivery.
Can organisations generate their own SBOM for third-party software?
In some cases, organisations can generate partial SBOMs using binary or runtime analysis tools. However, Vendor-provided SBOMs remain the most reliable source, as they reflect build-time dependencies and internal packaging details.
What should I do if an SBOM reveals vulnerable components?
When vulnerabilities are identified, organisations should assess exploitability, business impact and exposure. Engage the vendor to understand remediation timelines, available patches or mitigation steps.