When a business scales and accelerates, adoption of digital new assets is obvious. As we already discussed in the Attack Surface Monitoring guide, every new digital asset you add acts an attack surface. Sophisticated attackers today only need one exposed asset as an entry point to cause chaos. Therefore, there shouldn’t be a gap between visibility and control of assets because it can build risks quietly.
Types of attack surface monitoring help close this gap. They give security teams a clear, ongoing view of exposed assets, misconfigurations, and vulnerabilities. More importantly, they shift the focus from reactive fixes to continuous awareness. In this blog, we break down the different approaches, what they cover, and how they fit into a strong security strategy.
What are the different types of attack surfaces?
Before we explore monitoring types, it helps to understand what you are actually monitoring. An organisation’s attack surface is not just one layer. It spans across systems, people, and processes. Each layer introduces unique risks and requires a different monitoring approach.
- Digital attack surface: This includes all internet-facing assets such as web applications, APIs, cloud resources, domains, and IP addresses. It is often the largest and most dynamic surface.
- Physical attack surface: Endpoints like laptops, servers, and even office infrastructure fall into this category. Weak access controls or exposed devices can create entry points.
- Human attack surface: Employees, vendors, and partners form this layer. Phishing, credential leaks, and social engineering attacks target this surface directly.
Understanding these categories helps align the right types of attack surface monitoring with actual risk areas.
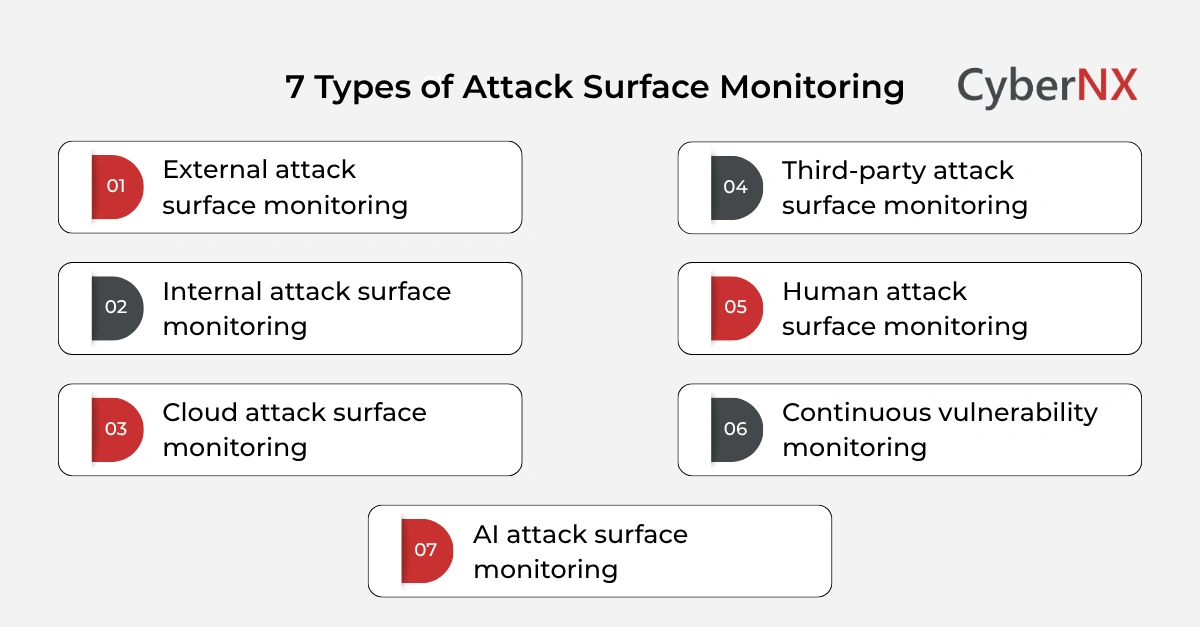
Types of attack surface monitoring
Each monitoring type focuses on a specific layer of exposure. Together, they create a more complete picture.
1. External attack surface monitoring (EASM)
External attack surface monitoring focuses on assets visible from the internet. It continuously scans domains, subdomains, IP ranges, and cloud services to identify exposures. This includes:
- Shadow IT assets
- Misconfigured cloud storage
- Exposed databases
- Forgotten subdomains
What makes EASM valuable is its attacker’s perspective. It shows what outsiders can see and exploit. Our experience shows that organisations often discover unknown assets within the first few scans. These blind spots are where many breaches begin.
2. Internal attack surface monitoring/Internal ASM
While external monitoring looks outward, internal monitoring focuses on what lies within the network. It tracks:
- Internal systems and applications
- Network configurations
- Lateral movement paths
- Privilege escalations
This type of monitoring is critical for limiting damage after an initial breach. Attackers rarely stop at one system. They move deeper and by continuously analysing internal exposure, teams can reduce the blast radius of any incident.
3. Cloud attack surface monitoring/Cloud ASM
Cloud environments evolve rapidly. New workloads spin up daily, and configurations change often. Cloud attack surface monitoring focuses on:
- Misconfigured storage buckets
- Over-permissioned identities
- Exposed APIs
- Publicly accessible workloads
Unlike traditional environments, cloud risks are often tied to configuration errors rather than software flaws. A misstep, like leaving a storage bucket public, can expose large volumes of sensitive data.
4. Third-party attack surface monitoring/ Third-party ASM
Vendors and partners extend your attack surface beyond your control. Yet their vulnerabilities can still impact your organisation. This type of monitoring tracks:
- Vendor security posture
- Exposed partner systems
- Supply chain risks
- Data-sharing vulnerabilities
Recent incidents show how attackers exploit weaker third-party systems to reach larger targets. Monitoring this layer helps security teams make better risk decisions when working with external partners.
5. Human attack surface monitoring
People remain one of the most targeted entry points. This monitoring type focuses on identifying risks related to users. It includes:
- Credential leaks on the dark web
- Phishing exposure
- Weak password practices
- Employee data exposure
Instead of blaming users, this approach highlights where awareness and controls need improvement. Stronger authentication policies can significantly reduce risk here.
6. Continuous vulnerability monitoring
This type of monitoring focuses on identifying known vulnerabilities across all assets. It scans for:
- Outdated software
- Missing patches
- Known CVEs
- Weak configurations
Unlike periodic assessments, continuous monitoring ensures vulnerabilities are tracked in real time. This reduces the window between discovery and remediation, which is often where attackers succeed.
7. AI attack surface monitoring
Although it may come under external and internal surfaces, AI needs special mention. This is because it will soon garner maximum attention in the near future.
AI attack surface monitoring is also something that needs attention. It focuses on risks introduced by AI systems, models, and their interactions. It tracks exposed model endpoints, insecure integrations, and misuse of prompts. This includes prompt injection attempts, data leakage through AI responses, and unauthorised access to model APIs.
In addition, it also aims to monitor shadow AI usage across teams, where sensitive data may be shared with external tools. As AI adoption grows, this layer helps maintain visibility over how models are used, what data they access, and where risks may emerge.
How these monitoring types work together
No single approach provides full coverage. Each type addresses a different part of the problem. When combined:
- External monitoring identifies entry points
- Internal monitoring limits movement
- Cloud monitoring secures dynamic environments
- Third-party monitoring reduces indirect risk
- Human monitoring addresses behavioural gaps
- Vulnerability monitoring ensures known risks are managed
Together, they create a layered view of exposure. We often see organisations rely heavily on one or two types while ignoring others. This creates uneven protection. Attackers tend to find those gaps quickly.
Key benefits for security leaders
Adopting multiple types of attack surface monitoring delivers clear advantages.
- Better visibility: You gain a real-time inventory of assets, including those previously unknown.
- Faster risk detection: Issues are identified early, before they turn into incidents.
- Improved prioritisation: Not all risks are equal. Monitoring helps focus on what matters most.
- Stronger compliance alignment: Many frameworks now expect continuous visibility and monitoring.
- Reduced attack opportunities: By shrinking exposed surfaces, you make it harder for attackers to find a way in.
Conclusion
Attack surfaces are expanding faster than most teams can track manually. Without clear visibility, risks remain hidden until it is too late.
Types of attack surface monitoring provide a structured way to understand and reduce this exposure. Each type plays a distinct role, but together they offer a complete defence strategy.
At CyberNX, we work closely with your team to map, monitor, and manage your attack surface in a way that fits your environment. If you are looking to gain better visibility and control, now is a good time to start the conversation. Contact us today to know more about our digital risk protection capabilities.
Types of attack surface monitoring FAQs
How is attack surface monitoring different from vulnerability scanning?
Attack surface monitoring focuses on discovering all exposed assets, including unknown ones. Vulnerability scanning focuses on identifying weaknesses within known assets.
How often should attack surface monitoring be performed?
It should be continuous. Modern environments change frequently, making periodic checks insufficient.
Can small organisations benefit from attack surface monitoring?
Yes. Smaller organisations often have limited visibility, which makes them attractive targets. Monitoring helps close these gaps.
What tools are used for attack surface monitoring?
Tools vary based on the type. They include EASM platforms, cloud security tools, vulnerability scanners, and threat intelligence solutions.