India’s financial sector is now operating under a coordinated SBOM compliance mandate – no longer a future expectation but a present regulatory obligation. The Reserve Bank of India issued a circular in November 2024 compelling the inclusion of SBOMs for software products and components within the banking ecosystem. This followed the RBI’s Master Directions on IT Governance, Risk, Controls and Assurance Practices (effective April 2024), which established a formal governance and control regime for banks, NBFCs, and all-India financial institutions covering software supply chain transparency, vendor risk and incident response readiness.
The regulatory environment has since intensified further. CERT-In issued its Technical Guidelines on SBOM Version 2.0 in July 2025 which expands mandatory coverage to government, public sector and essential services organisations, and broadening the BOM framework beyond software to include HBOM, CBOM, AIBOM and QBOM. SEBI reinforced these requirements in its LODR Master Circular issued January 30, 2026, mandating SBOMs for all core operations including SaaS deployments. Together, RBI, SEBI, and CERT-In now form an aligned, sector-spanning compliance framework that leaves no room for a wait-and-see approach.
This blog explores the key requirements, documentation norms, implementation timeline, and penalties associated with RBI SBOM compliance. And how organisations can build a sustainable compliance posture that meets all three regulators’ expectations.
Understanding RBI SBOM Compliance
First, you need to know what SBOM is, and our blog SBOM Guide will help you do that. The RBI’s SBOM requirement is a strategic imperative for national financial security. With growing reliance on third-party software and open-source tools, hidden vulnerabilities can leave even the most secure systems exposed. By mandating SBOM, the RBI aims to:
- Improve visibility into all software components, including third-party and open-source elements
- Enable faster incident response by identifying and isolating vulnerable components
- Promote accountability among software vendors and financial institutions
What has changed since 2024 is the coordinated nature of this regulatory push. RBI, SEBI, and CERT-In are no longer issuing SBOM guidance in isolation, they are collectively building an interlocking framework. CERT-In’s Version 2.0 guidelines expand the BOM obligation to hardware, AI systems, and cryptographic components. SEBI’s January 2026 LODR Master Circular mandates SBOM for SaaS and core operations with board-level accountability for exceptions. For organisations operating in BFSI, this means that SBOM compliance is not a one-time project. It is a constant governance obligation that includes procurement, development, deployment and vendor management.
Key SBOM Requirements from RBI
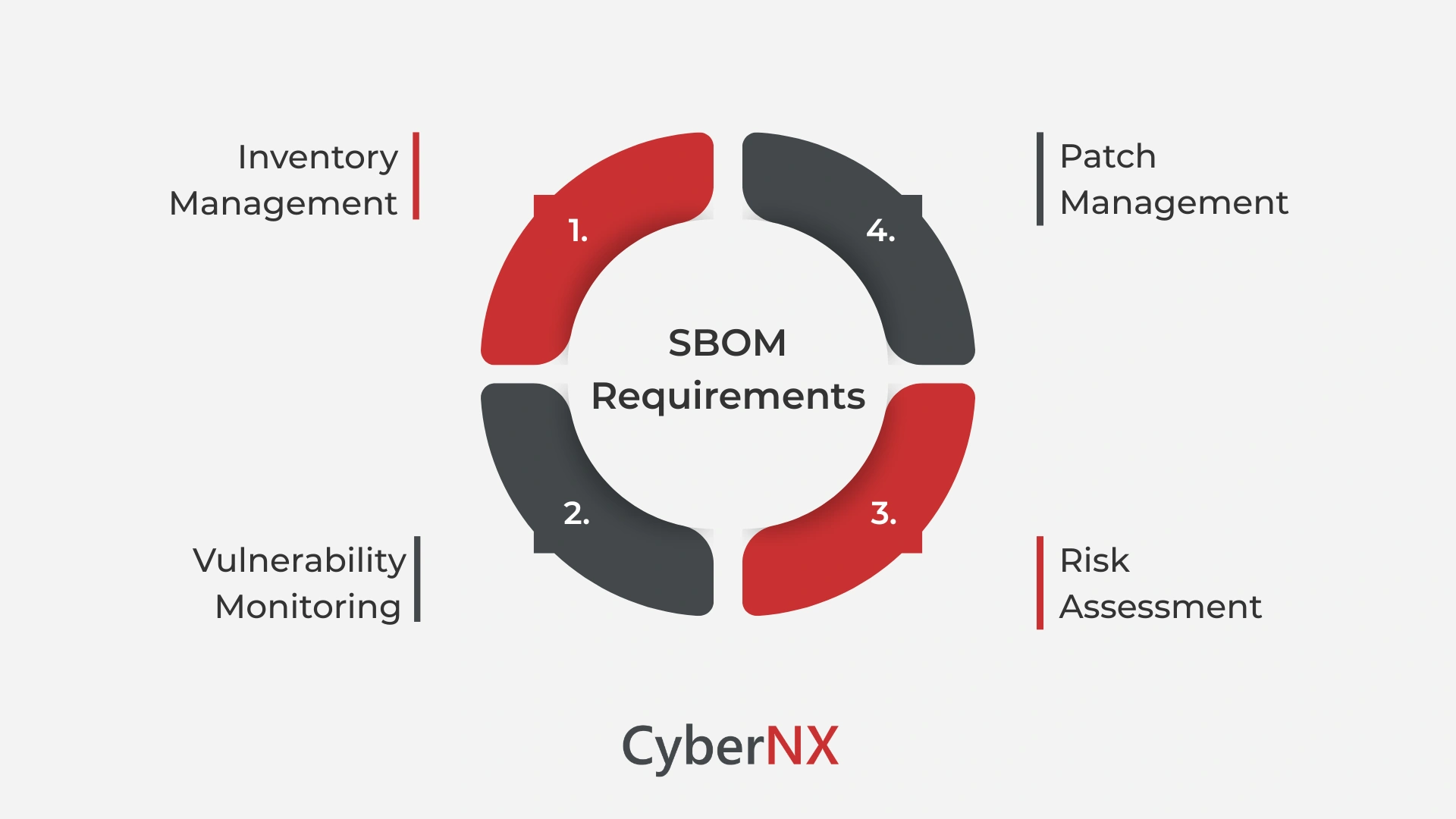
The guidelines for RBI SBOM Compliance outlines four core areas for compliance. These form the foundation of a robust software supply chain governance program.
1. Inventory Management
Every regulated entity must maintain an up-to-date SBOM for all critical applications, listing every software component-proprietary, open-source, or third-party. This includes versioning, licensing, and source information to track components across systems.
2. Vulnerability Monitoring
Continuous monitoring of known vulnerabilities (such as those in the National Vulnerability Database) is essential. Organizations must have tools and processes in place to detect vulnerabilities as soon as they are publicly disclosed.
3. Patch Management
Identified vulnerabilities must be remediated through patches or configuration changes in a timely manner. RBI expects institutions to follow a structured patch lifecycle and document all fixes as part of compliance.
4. Risk Assessment
Periodic risk assessments must be conducted to evaluate the health of the software supply chain. This includes assessing third-party libraries, open-source packages, and vendor software to identify potential entry points for threat actors.
Implementation Timeline for RBI SBOM Compliance
The regulatory timeline for SBOM compliance in India’s financial sector has evolved significantly. Here is where the key milestones now stand:
- April 2024 – RBI Master Directions effective: RBI’s Master Directions on IT Governance, Risk, Controls and Assurance practices came into force for scheduled commercial banks, NBFCs, and all-India financial institutions. These directions establish vendor risk management, third-party oversight, and incident response obligations that directly align with SBOM-like transparency requirements.
- August 2024 – SEBI CSCRF introduced: SEBI revealed its Cybersecurity and Cyber Resilience Framework (CSCRF) that integrates mandatory SBOM requirements for all regulated entities’ critical systems. Initial compliance deadlines applied from January 2025, with the final deadline for most regulated entities extended to August 31, 2025.
- November 2024 – RBI SBOM circular issued: RBI issued a circular specifically forcing the inclusion of SBOMs for software products and components within the banking ecosystem, bringing RBI’s SBOM expectation from implied to explicit.
- July 2025 – CERT-In Version 2.0 guidelines: CERT-In expanded its SBOM framework to include HBOM (hardware), CBOM (cryptographic), AIBOM (AI systems), and QBOM (quantum). It makes SBOMs mandatory for government, public sector and essential services organisations and strongly recommended for all others.
- January 2026 – SEBI LODR Master Circular: As per SEBI’s LODR Master Circular, SBOM is mandatory for core operations – including SaaS deployments – with board approval required for any legacy system exceptions.
- Ongoing – Vendor contracts and quarterly reporting: All new vendor contracts must include SBOM generation and risk-sharing clauses. Quarterly SBOM posture reports covering vulnerability tracking and remediation status must be submitted to the board and, where required, to the RBI.
Organisations that have not yet started their SBOM implementation are already operating behind the compliance curve. The priority now is not planning but execution.
Mandatory Documentation for Compliance
RBI’s compliance regime is documentation-heavy to ensure verifiability and audit readiness. Every regulated entity must maintain:
- A comprehensive SBOM for all critical applications
- Vulnerability assessment reports mapped to CVEs and impact severity
- Documented patch management procedures
- Vendor risk assessment reports, especially for critical third-party tools
- A board-approved software supply chain risk policy
Each of these documents must be updated regularly and made available during regulatory audits or cyber incident reviews.
Penalties for Non-Compliance
The RBI has emphasized strict enforcement. Non-compliance may result in a range of consequences that can impact both operations and reputation:
- Monetary penalties up to ₹1 crore for significant violations
- Increased regulatory scrutiny and reporting obligations
- Business restrictions including delays in product rollouts
- Mandatory third-party audits ordered by the RBI
- Public disclosure of non-compliance, which could damage trust and reputation
How to Prepare for RBI SBOM Compliance?
To get ahead of the RBI SBOM compliance curve, regulated entities should:
- Invest in an automated SBOM management platform that handles the full lifecycle: generation from container scans, image registries, and vendor-provided SBOMs; centralized storage with version control; continuous vulnerability monitoring with risk-based prioritization; and compliance-ready reporting aligned to SEBI CSCRF, RBI, and CERT-In requirements.
- Create a centralized software inventory with versioning and dependency mapping
- Integrate SBOM generation into CI/CD pipelines for ongoing compliance
- Establish a governance team responsible for vulnerability management and policy enforcement
- Work with vendors who demonstrate SBOM readiness and agree to RBI-aligned terms
Conclusion
RBI SBOM Compliance is an obligation reinforced by a coordinated regulatory framework that includes RBI, SEBI, and CERT-In. Organisations that treat SBOM as a compliance burden will find themselves in a reactive cycle of remediation and audit exposure. Those that treat it as a strategic asset will gain faster vulnerability response, stronger vendor governance, and a security posture that regulators and customers can trust.
CyberNX’s SBOM management platform is specifically aligned to India’s regulatory landscape. It covers SEBI CSCRF, RBI Master Directions and November 2024 circular, and CERT-In Technical Guidelines Version 2.0. Our four-stage approach – automated collection, centralised management, continuous analysis, and actionable reporting -delivers compliance-ready outputs without disturbing your development pipeline.
To know more about our SBOM tool and understand how we can help you generate and manage SBOMs, contact us today.
RBI SBOM Compliance FAQs
Can legacy systems be exempt from RBI SBOM Compliance requirements?
No, RBI has not provided specific exemptions for legacy systems. However, institutions may face practical challenges in generating SBOMs for older applications lacking source control or documentation. In such cases, RBI expects entities to document their limitations, adopt best-effort inventory practices (like binary analysis), and develop a phased plan to bring legacy systems into compliance.
How should financial institutions evaluate third-party vendors for RBI SBOM compliance?
Institutions must assess vendors on their ability to generate, maintain, and share SBOMs in machine-readable formats. Evaluation criteria should include the vendor’s transparency around software dependencies, their vulnerability disclosure practices, update frequency, and support for standards like SPDX or CycloneDX. RBI encourages inclusion of SBOM clauses in procurement and vendor risk contracts.
What SBOM formats are acceptable for compliance with RBI guidelines?
While RBI hasn’t mandated a specific format, industry-standard SBOM formats like SPDX, CycloneDX, and SWID are considered acceptable. These formats support automation, interoperability, and version control-making them suitable for long-term compliance tracking, audit readiness, and integration with CI/CD pipelines.
How frequently should the SBOM be updated to remain compliant?
RBI expects SBOMs to be updated at every major software release, patch, or dependency change. Additionally, regulated entities should conduct quarterly reviews to validate their software inventory, remove outdated components, and align their SBOM with current production environments. Real-time SBOM generation through DevSecOps practices is strongly recommended for dynamic applications.