The problem is cybercriminals trade stolen credentials, leaked databases and confidential files quickly, sometimes within hours of an incident. This probably answers the important question of how often should dark web monitoring be performed.
Many organisations assume a quarterly or monthly check is enough. In practice, that approach leaves large blind spots. Dark web monitoring helps detect exposed credentials, compromised employee accounts, and leaked company data early. When done properly, it provides a valuable early warning system that allows teams to respond before attackers exploit the information.
Understanding the right monitoring frequency is critical for turning this intelligence into meaningful protection.
Why dark web monitoring matters for organisations
The dark web has become a marketplace for cybercriminal activity. Credentials, access tokens, intellectual property, and corporate databases are regularly traded across hidden forums and marketplaces.
When attackers obtain this information, they often sell it to other groups who specialise in ransomware, phishing campaigns, or corporate espionage.
For organisations, the consequences can be severe. Stolen credentials can lead to account takeovers. Exposed employee emails can fuel targeted phishing attacks. Sensitive business data can damage reputation and regulatory compliance.
Dark web monitoring helps identify these risks early. Security teams gain visibility into leaked information and can take action quickly.
How often should dark web monitoring be performed?
The short answer is simple: dark web monitoring should be continuous rather than periodic.
Threat activity on underground forums does not follow business hours or reporting cycles. Data leaks and credential dumps can appear at any time. A one-time scan or monthly review may detect old breaches but miss active threats that are already being exploited. Continuous monitoring allows organisations to detect exposure within hours or days rather than weeks. Security teams can then reset passwords, revoke access, investigate compromised accounts, and reduce the likelihood of further attacks.
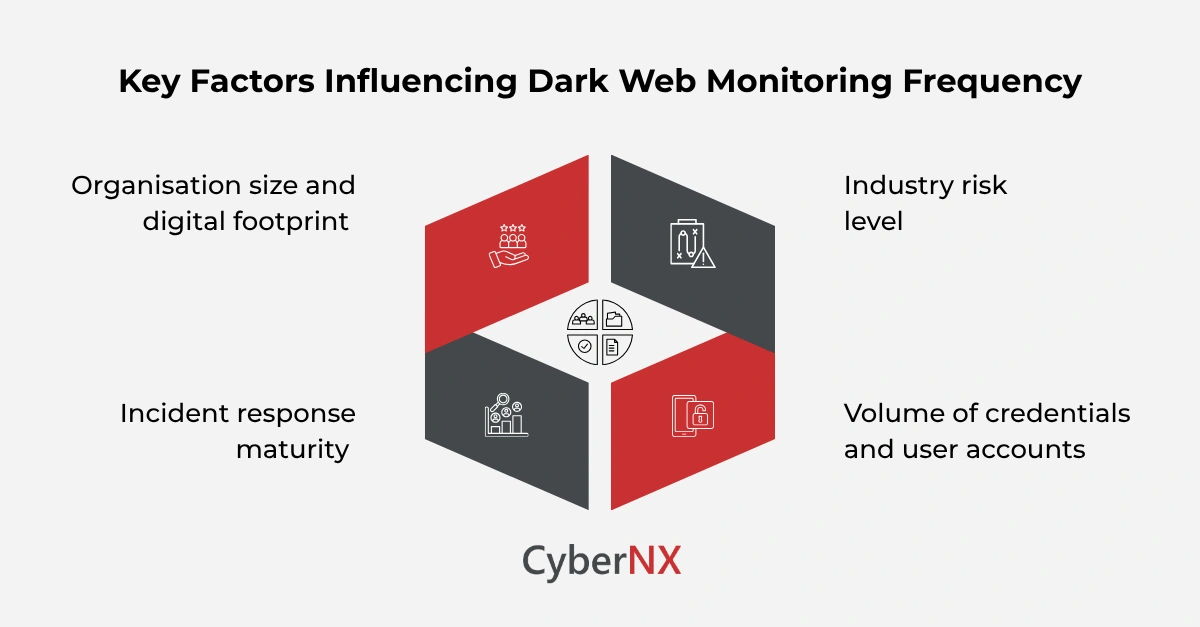
Factors that influence monitoring frequency
While continuous monitoring is ideal, several factors influence how frequently organisations should review and act on dark web intelligence.
1. Organisation size and digital footprint
Larger organisations usually have more employees, domains, and digital assets exposed online. This increases the chance of credentials appearing in underground forums. Enterprises with a large digital footprint benefit significantly from real time monitoring and automated alerts.
Smaller organisations may see fewer leaks but still face similar risks when credentials appear online.
2. Industry risk level
Some sectors face higher targeting from cybercriminals. Financial services, healthcare, technology firms, and government organisations are often targeted for sensitive data or access to valuable systems.
Companies in these sectors should prioritise continuous monitoring and frequent threat intelligence reviews.
3. Volume of credentials and user accounts
Organisations with thousands of employee accounts are more likely to see password reuse and credential exposure. If even a small percentage of users reuse passwords across platforms, a breach on another service can quickly lead to corporate account compromise.
Frequent monitoring helps identify exposed accounts before attackers attempt credential stuffing attacks.
4. Incident response maturity
Organisations with mature security operations centres can act quickly when dark web alerts appear. If monitoring tools generate alerts, but no team reviews them regularly, the value of monitoring decreases significantly. Effective monitoring combines automated detection with clear response processes.
What effective dark web monitoring looks like
Effective dark web monitoring involves more than simply scanning forums for company names. Strong programmes typically include multiple intelligence sources and automated alerting. These include monitoring for leaked employee credentials, compromised domains, exposed corporate emails, and stolen databases linked to the organisation.
Dark web Monitoring tools should also analyse underground marketplaces, paste sites, and criminal communities where breach data is frequently shared. When suspicious data appears, alerts should reach security teams quickly so they can investigate.
The role of automation in continuous monitoring
Manual searches across dark web sources are time consuming and often ineffective. Many underground communities require specialised access or constant monitoring to track new activity. Automated monitoring platforms collect data from multiple sources, analyse mentions of organisational assets, and generate alerts when exposure occurs.
This approach allows organisations to maintain continuous visibility without overwhelming security teams. Automation also helps correlate leaked data with internal assets, making investigation faster and more accurate.
Conclusion
Understanding how often dark web monitoring should be performed helps organisations move from reactive security to early threat detection.
Periodic checks provide limited visibility and often detect incidents after attackers have already exploited stolen information. Continuous monitoring offers a more practical approach. It enables organisations to detect leaked credentials quickly, investigate potential breaches, and prevent attackers from gaining further access.
At CyberNX, we strengthen threat visibility and response capabilities. If you want to understand whether your organisation’s data is already circulating on underground forums, our team can help assess exposure and implement effective monitoring strategies. Contact us today to know more about our dark web monitoring services.
FAQs
What types of data are usually found through dark web monitoring?
Common discoveries include leaked usernames and passwords, corporate email addresses, internal documents, database dumps, and access credentials for company systems.
Can dark web monitoring prevent cyber-attacks?
Dark web monitoring does not stop attacks directly, but it provides early warning signals. This allows organisations to respond before attackers exploit exposed information.
Who should be responsible for dark web monitoring in an organisation?
Typically, security operations teams, threat intelligence teams, or managed security providers handle monitoring and investigation of dark web alerts.
How quickly should organisations respond to dark web alerts?
Security teams should review dark web alerts immediately. Rapid actions such as password resets or account lockdowns can significantly reduce risk.