The future of dark web monitoring is no longer a distant concern. It is unfolding in real time. Dark web feels unpredictable, opaque, and increasingly difficult to track. At the same time, AI is accelerating both sides of the equation.
Attackers are using AI to scale operations, automate fraud, and refine targeting. Meanwhile, defenders are turning to AI to improve visibility and response. This shift is redefining how organisations detect, interpret, and act on digital risks.
In this blog, we explore what the dark web will look like in 2026 and how the dark web monitoring is evolving to meet AI-driven threats.
How the dark web is evolving in 2026
The dark web has changed shape over the years. Let’s see what’s expected in 2026:
A shift from static marketplaces to dynamic ecosystems
Earlier, dark web marketplaces operated like structured platforms. Today, they are fragmented and short-lived. Threat actors move between encrypted messaging apps, invite-only groups, and decentralised platforms.
This creates a moving target. Traditional monitoring approaches struggle to keep up because sources change quickly and often disappear overnight.
Rise of AI-powered cybercrime
AI is not just a defensive tool. It is now deeply embedded in offensive operations. Attackers are using AI to:
- Generate highly convincing phishing messages in multiple languages
- Automate vulnerability discovery
- Create deepfake identities for fraud and social engineering
This lowers the barrier to entry. Even less-skilled attackers can launch sophisticated campaigns. As a result, the volume and quality of threats on the dark web are increasing.
Data is becoming more valuable, more exposed
Stolen data remains the currency of the dark web. However, the nature of that data is changing. Instead of large dumps, threat actors now sell:
- Access credentials to SaaS platforms
- Session cookies and authentication tokens
- Real-time access to compromised systems
This shift makes breaches more actionable. It also shortens the time between exposure and exploitation.
Blurring lines between dark web and open internet
In 2026, the boundaries are less clear. Some threat activity starts on the dark web but quickly moves to public platforms like forums or messaging apps. This convergence means organisations cannot rely on isolated monitoring strategies. Visibility must extend across multiple layers of the internet.
What is the future of the dark web?
To better understand what future holds for dark web monitoring, you need assess what is the future of the dark web first. The direction is becoming clearer, even as the ecosystem grows more complex. The dark web is evolving across several key dimensions:
| TREND | WHAT IT MEANS IN PRACTICE |
| More decentralised | Platforms are harder to take down, with activity spread across multiple networks and channels |
| More automated | AI and machine learning are enabling faster, scalable cybercrime operations |
| More accessible | Lower technical barriers allow more actors to participate in cybercriminal activities |
| More integrated | Dark web activity increasingly overlaps with surface web and mainstream platforms |
This shift signals a more fluid and unpredictable threat landscape. For security teams, visibility alone will not be enough. Context and speed will matter just as much. For organisations, threat landscape will not only grow but also become faster and less predictable.
Future of dark web monitoring in an AI-driven world
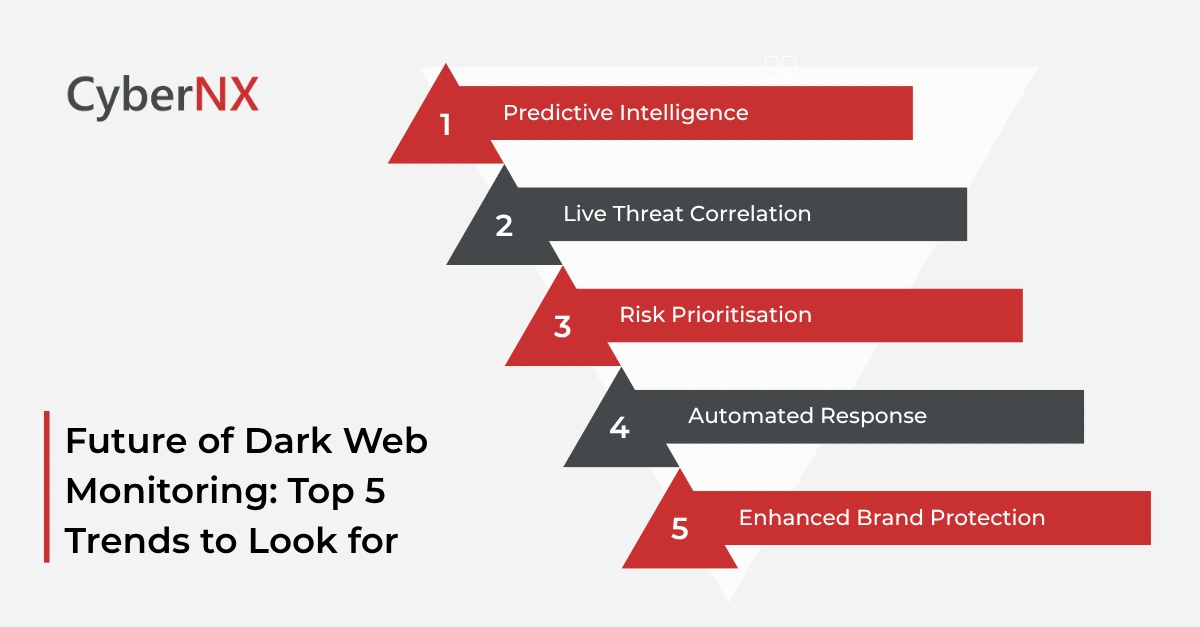
As the threat landscape evolves, so does the future of dark web monitoring. Traditional approaches based on manual tracking and keyword alerts are no longer enough. We will possibly see the following trends in the coming times:
1. Predictive intelligence
Dark web monitoring used to focus on detecting leaked data after exposure. That model is shifting.
AI enables predictive capabilities. By analysing patterns, behaviours, and historical data, organisations can anticipate risks before they fully materialise.
For example, early signals such as discussions about a target company or emerging exploit trends can trigger proactive action.
2. Real-time threat correlation/Live threat correlation
The modern dark web is fragmented. Monitoring tools must aggregate data from forums, marketplaces, messaging platforms, and even the open web.
AI helps correlate these signals in real time. It connects seemingly unrelated data points to reveal meaningful insights.
This reduces noise. It also allows security teams to focus on threats that truly matter.
3. Context-driven risk prioritisation/Risk prioritisation
One of the biggest challenges in dark web monitoring is alert fatigue. Not every mention or data leak is critical.
AI brings context into the picture. It evaluates:
- The credibility of the source
- The relevance of the data
- The potential impact on the organisation
This helps prioritise risks effectively. Security teams can act faster and with greater confidence.
4. Automated response & remediation/Automated response
Detection alone is not enough. In the future, dark web monitoring will have to include automated response mechanisms.
AI can trigger actions such as:
- Forcing password resets
- Blocking compromised accounts
- Initiating incident response workflows
This reduces response time significantly. In many cases, it can prevent incidents from escalating.
5. Enhanced identity & brand protection/Enhanced brand protection
AI-driven monitoring goes beyond data leaks. It also focuses on identity misuse and brand abuse. Organisations can detect:
- Fake domains and phishing sites
- Impersonation attempts
- Fraudulent listings using their brand
This broader visibility strengthens digital risk protection across multiple fronts.
Conclusion
The future of dark web monitoring is being shaped by two forces moving in parallel. AI is enabling more sophisticated cyber threats, while also offering powerful tools to detect and mitigate them.
For organisations, the path forward is clear. Embrace AI-driven monitoring, but do so with a strategic, well-integrated approach. Combine technology with human insight. Expand visibility. Act faster.
At CyberNX, we work closely with your team to strengthen your digital risk protection strategy. Our advanced dark web monitoring services will help you stay ahead of evolving threats with clarity and confidence. Ready to elevate your security posture? Connect with our experts for a tailored consultation.
Future of dark web monitoring FAQs
How is AI changing dark web monitoring capabilities?
AI enables faster data analysis, real-time threat detection, and predictive insights, making monitoring more proactive and accurate.
What types of data can be found on the dark web in 2026?
Data includes credentials, financial information, access tokens, and even live system access, rather than just static data dumps.
Is dark web monitoring enough to prevent cyberattacks?
No, it should be part of a broader security strategy that includes endpoint protection, network security, and incident response.
How often should organisations review their dark web monitoring strategy?
It is advisable to review and update strategies regularly, especially as new threats and technologies emerge.