The internet age has ushered in limitless opportunities for your modern, digitally equipped enterprise. In the same breath, however, it is important to take a hard look at the fact that data shared, stored and available online is not secure. In many cases, hackers break into organisations, extract sensitive information and sell them in the dark web. It is only quite later that someone realizes that a data breach has occurred.
Data breach detection is an effective process of identifying unauthorized access to your data. It needs to extend beyond internal logs and more into external visibility. Dark web monitoring gives you that edge by surfacing leaked credentials, datasets, and access points early.
In this blog, we lay bare the process of how to detect data breach activity using dark web monitoring in a practical, grounded way.
Dark web monitoring for data breach detection
Every thief needs a marketplace to sell what’s stolen. The dark web is a network of forums, marketplaces, and private groups where cybercriminals/hackers exchange stolen data for money.
So, how does dark web monitoring helps? As the stolen data often appears here before it is used in attacks, the experts have the chance to block the sale. Timing is everything.
Dark web monitoring focuses on identifying exposed data linked to your organisation. This could be employee credentials, customer records, or even internal documents. In practice, security teams often start by tracking a few critical data types:
- Corporate email domains that may appear in credential dumps
- Customer data sets being traded or shared
- Mentions of internal systems or brand identifiers
This early visibility helps detect data breaches before they escalate. It gives you a chance to act while the window is still small.
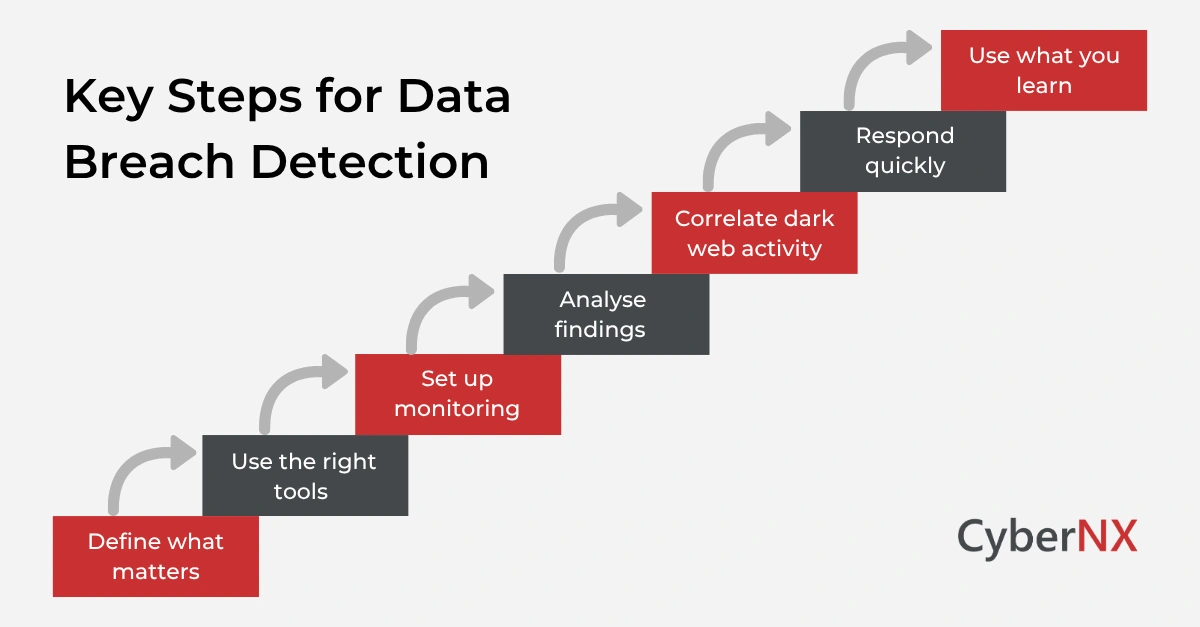
How to detect data breach: step-by-step guide
A structured approach keeps things manageable. Without it, monitoring turns into noise. Here is how experienced teams handle data breach detection using dark web intelligence.
1. Define what matters before you start monitoring
One common mistake is trying to monitor everything. That quickly becomes overwhelming. Instead, focus on assets that would cause real damage if exposed. For most organisations, this includes employee identities, privileged accounts, and sensitive customer data.
For example, a SaaS company may prioritise admin credentials and API keys. A financial services firm may focus more on transaction-related data. We usually suggest starting narrow. Once you see useful signals, you can expand coverage with confidence.
2. Use the right tools, but focus on context
Dark web monitoring at scale is not something you can do manually. You need tools that collect and analyse data continuously. Security teams often use a combination of platforms such as Recorded Future, SpyCloud, or Digital Shadows. Each brings a slightly different strength. Some focus on credentials, others on broader threat intelligence.
A small but important nuance here. The real value is not just in finding exposed data but understanding it. Knowing whether a credential is part of a recent breach or an old dataset change how you respond. That context is what separates useful alerts from noise.
3. Set up monitoring that works in real time
Once tools are in place, the next step is making sure they work continuously.
This means configuring alerts for meaningful triggers. For instance, teams often track when new credentials linked to their domain appear or when their brand is mentioned in underground discussions.
Rather than relying on periodic reports, the goal is to create a steady stream of signals. These signals should ideally flow into your existing security platforms so that they do not sit in isolation. This integration is where things start to click. External intelligence begins to complement internal visibility.
4. Analyse findings instead of reacting blindly
Not every alert means a new breach. Some data gets recycled across forums. Some datasets are years old. This is where teams slow down and assess what they are seeing. They look at how recent the data is, whether it maps to active users, and whether there are signs that the data is being actively used or discussed.
For example, a fresh credential dump containing valid passwords is a very different situation from an old database leak resurfacing. This step is less about speed and more about accuracy. It prevents overreaction while ensuring real threats are not missed.
5. Connect dark web signals with what is happening internally/ Correlate dark web activity
This is where data breach detection becomes far more effective. A single external alert might raise suspicion. But when you connect it with internal behaviour, patterns emerge.
Imagine you discovering exposed employee credentials on a dark web forum. Around the same time, your systems show repeated access attempts on that account from unfamiliar locations. On their own, each signal might seem minor. Together, they tell a clear story. This correlation helps teams move from “something might be wrong” to “we need to act now.”
6. Respond quickly and contain the risk
Once you confirm a potential breach, action needs to be immediate. Security teams typically focus on containing access and preventing further misuse. This often includes resetting credentials, revoking sessions, and tightening authentication controls.
In more serious cases, teams may also investigate whether attackers have moved deeper into the environment. The earlier you act, the smaller the impact. That is the real advantage of detecting breaches at this stage.
7. Use what you learn to strengthen your defences
Every exposure gives you valuable insight. Ignoring that insight means missing an opportunity to improve. Over time, patterns start to appear. Maybe employees are reusing passwords. Maybe certain systems are more exposed than expected. Maybe third-party risks are higher than assumed.
These insights often lead to focused improvements such as:
- Strengthening identity and access controls
- Improving employee awareness around credential hygiene
- Reviewing third-party access and integrations
This is how data breach detection evolves from a reactive process into a learning system.
Real-world example: catching a breach early
A growing SaaS company once identified a small set of employee credentials through a dark web monitoring tool. At first glance, it did not seem critical. But the details told a different story. The credentials were recent and the passwords appeared valid. Some of the accounts had elevated access. When the team checked their systems, they noticed unusual access attempts linked to those accounts.
They acted quickly. Access was secured, sessions were terminated, and stronger authentication was enforced. What could have turned into a major incident was contained early. This is often how dark web monitoring proves its value. Not through dramatic discoveries, but through timely ones.
Conclusion
Data breaches often begin outside your immediate view. Waiting for internal alerts means reacting after the fact. Dark web monitoring brings those early signals into focus. It helps detect data breaches while there is still time to act. Data breach detection becomes more proactive, more connected, and more aligned with how threats actually unfold.
Looking to strengthen your data breach detection approach? Our dark web monitoring services can help you build a strategy that fits your environment and risk profile. Let us work together to improve how you detect and respond to threats.
Data breach detection FAQs
How to detect data breach activity early?
By monitoring external sources like the dark web, organisations can identify leaked data before attackers fully exploit it.
What makes dark web monitoring effective for data breach detection?
Its ability to surface exposed credentials and datasets early makes it a valuable addition to internal monitoring systems.
Can dark web monitoring replace traditional security tools?
No. It complements existing tools by adding external visibility.
How often should dark web monitoring be reviewed?
Monitoring should run continuously, with regular analysis to validate and prioritise findings.