You have deployed powerful security tools before and you know that success lies in execution. A missed configuration or unchecked integration can limit visibility and weaken detection outcomes. That is why a structured CrowdStrike NG-SIEM implementation checklist is critical.
If you have already reviewed the CrowdStrike NG-SIEM implementation guide, this checklist acts as your validation layer. It confirms that each essential task has been completed, tested, and aligned with your enterprise security objectives.
We created this checklist to help SOC leaders and IT heads ensure that their NG-SIEM rollout delivers measurable value from day one.
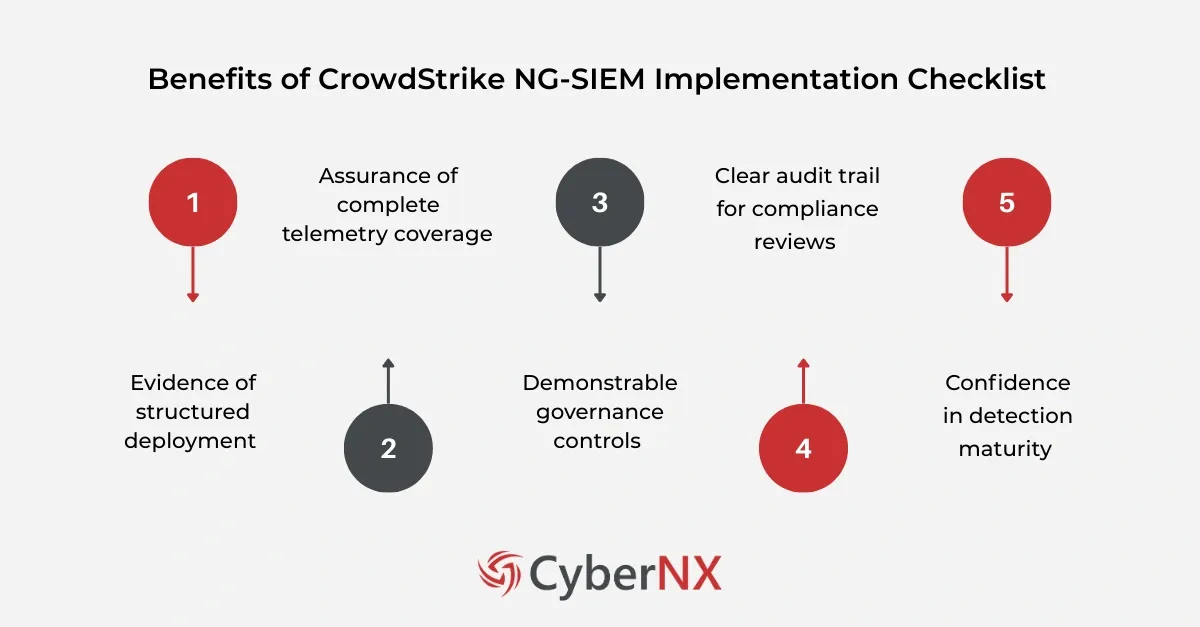
Why a validation checklist matters
CISOs today answer difficult questions from boards and regulators. They must prove that security investments deliver outcomes.
A documented checklist provides:
- Evidence of structured deployment
- Assurance of complete telemetry coverage
- Demonstrable governance controls
- Clear audit trail for compliance reviews
- Confidence in detection maturity
It turns a technical rollout into a strategic control framework.
Pre-Deployment validation
Before activating production workloads, you must validate foundational readiness. Skipping this stage often leads to ingestion gaps and performance issues later.
1. Environment readiness validated
- Infrastructure capacity assessed for expected log volume
- Network bandwidth verified for real time data transfer
- Endpoint, cloud, and identity integrations reviewed
- Time synchronisation confirmed across systems
- Existing SIEM coexistence or migration strategy defined
Ensure that storage and compute planning match projected daily ingestion. Underestimating log volume is a common oversight.
2. Licensing verified
- Appropriate CrowdStrike licensing tier confirmed
- Data ingestion limits reviewed
- Retention entitlements validated
- User licences mapped to SOC roles
Licensing alignment avoids unexpected ingestion throttling. It also ensures the SOC team can access required features without delay.
Data onboarding and log ingestion
Visibility defines detection quality. If telemetry is incomplete, threat detection will always lag.
1. Data sources identified
- Endpoints enrolled via CrowdStrike Falcon agent
- Cloud platforms connected including AWS, Azure, and GCP
- Identity providers integrated
- Network security tools configured for log export
- Critical business applications identified for logging
Prioritise high risk assets first. Domain controllers, privileged accounts, production workloads, and internet facing systems should never be delayed.
2. Log ingestion configured
- Data connectors enabled
- API integrations authenticated and tested
- Parsing and normalisation verified
- Log format consistency confirmed
- Sample logs validated in the console
Review ingestion dashboards daily during rollout. This confirms steady data flow and helps detect silent failures early.
Detection and alerting configuration
Deployment without detection logic delivers limited security value. Configuration must align with your threat model.
1. Alerting rules enabled
- Default detection policies reviewed and activated
- Custom detection rules configured for business risks
- MITRE ATT&CK mapping verified
- False positive thresholds adjusted
- Alert severity levels aligned to incident response playbooks
CrowdStrike intelligence feeds provide strong baseline coverage. However, custom use cases such as insider risk or regulatory monitoring require tailored rules.
2. Escalation workflows validated
- Alerts integrated with ticketing systems
- Automated response playbooks tested
- Notification channels verified
- Escalation matrix documented
SOC fatigue often stems from unclear workflows. Validate routing before going live.
Dashboards and reporting
Security data must inform decisions. Dashboards help leadership understand posture in real time.
Dashboards configured
- Executive summary dashboard created
- SOC operational dashboard configured
- Threat hunting views customised
- Compliance reporting templates built
- KPI tracking metrics defined
Executives need clarity, not noise. Focus on risk exposure, incident trends, and response time metrics.
Access and governance controls
A SIEM platform stores sensitive telemetry. Governance must be tightly managed.
1. Access controls reviewed
- Role based access configured
- Least privilege principles applied
- Administrative accounts reviewed
- Multi factor authentication enforced
- Access logging enabled
Periodic access review prevents privilege creep. It also strengthens compliance posture.
2. Data retention policies applied
- Retention duration aligned with regulatory requirements
- Legal hold processes defined
- Archive storage configured
- Deletion policies documented
Regulations such as GDPR or sector specific mandates may dictate retention periods. Align policies early to avoid reconfiguration later.
Testing and validation
Deployment is not complete until validation confirms expected outcomes.
1. Testing and validation completed
- Controlled attack simulations executed
- Detection accuracy validated
- False positive rates measured
- Incident response runbooks tested
- Performance benchmarks recorded
Run red team exercises or simulated phishing campaigns. Observe whether alerts trigger correctly and whether analysts respond within target SLAs.
Document findings. Fine tune configurations before full production sign off.
Operational readiness and continuous improvement
Even after validation, optimisation remains ongoing.
1. Operational processes established
- Daily health monitoring procedures defined
- Weekly rule tuning sessions scheduled
- Monthly reporting cadence established
- Quarterly architecture review planned
A SIEM is not a static deployment. It evolves with your threat landscape.
Common gaps we see in enterprise deployments
Even mature teams occasionally miss critical steps. Our experience working alongside enterprise security leaders shows recurring patterns:
- Data ingestion is enabled but not monitored. Silent log failures remain undetected.
- Alert rules are activated but not tuned to business context. Analysts face noise.
- Dashboards are built for operations but not for board level visibility.
- Retention settings are configured without validating regulatory alignment.
Small configuration gaps can reduce detection effectiveness significantly. A structured CrowdStrike NG-SIEM implementation checklist prevents these blind spots.
Conclusion
A successful deployment is not defined by installation. It is defined by validation. This CrowdStrike NG-SIEM implementation checklist ensures your platform is configured, governed, and tested for real world threats.
If you want an independent validation of your deployment, our experts can help. We work with SOC team to review configurations, identify blind spots, and optimise detection performance. Book a CrowdStrike Consultation to ensure your NG-SIEM delivers measurable security outcomes.
CrowdStrike NG-SIEM implementation checklist FAQs
How long does a CrowdStrike NG-SIEM implementation validation typically take?
Validation timelines depend on environment size and log sources. Mid-sized enterprises typically complete structured validation within two to four weeks.
What metrics should be tracked after deployment?
Track ingestion volume, alert accuracy, mean time to detect, mean time to respond, and false positive rate. These indicators reflect operational maturity.
Should legacy SIEM systems run in parallel during transition?
Yes, parallel operation helps ensure no telemetry gaps. Gradual migration reduces operational risk.
How often should detection rules be reviewed?
Quarterly reviews are recommended. However, high risk industries may require monthly tuning to adapt to evolving threats.