We often see organisations invest heavily in detection and response tools. Yet they still lack a clear view of what needs protection. Attack surface management helps address this gap. It gives teams continuous visibility into all exposed assets and helps reduce risk before exploitation happens.
If you are already exploring attack surface monitoring, you are on the right track. However, attack surface management is broader, more strategic, and focused on long-term risk reduction rather than just visibility.
What is attack surface management?
Attack surface management is a continuous process of discovering, analysing, prioritising, and reducing an organisation’s exposed digital assets.
It includes everything that could be targeted by attackers. External assets like websites, APIs, and cloud services. Internal assets such as endpoints and servers. Even shadow IT and forgotten systems.
Unlike one-time assessments, attack surface management is ongoing. It adapts as your environment changes.
Key components of attack surface management
Attack surface management works best when it follows a structured lifecycle.
1. Asset discovery
You cannot protect what you cannot see. Modern enterprises often have assets spread across multiple environments. Public cloud, on-premise systems, SaaS platforms, and third-party services. Many of these assets are spun up quickly and forgotten just as fast.
Attack surface management tools continuously scan and identify these assets. This includes unknown or unmanaged ones.
2. Risk analysis
Once assets are discovered, the next step is to assess their risk. This includes identifying vulnerabilities, misconfigurations, outdated software, and exposed credentials. Context matters here. A critical vulnerability on an internet-facing system carries more risk than one on an isolated internal system.
3. Prioritisation
Security teams often deal with alert fatigue. Attack surface management helps prioritise issues based on exploitability and business impact. This ensures teams focus on what truly matters instead of chasing every low-risk alert.
4. Remediation and validation
Fixing issues is only part of the process. Attack surface management also validates whether the remediation has been effective. Continuous monitoring ensures that the same risks do not reappear.
Why attack surface management matters now
The modern attack surface is dynamic. It changes daily. Cloud workloads scale up and down. Developers deploy updates frequently. Employees access systems from different locations and devices. This speed creates opportunities for attackers.
Without attack surface management, organisations rely on outdated asset inventories and periodic scans. These approaches miss critical exposures. We have observed that even mature security teams struggle with:
- Unknown internet-facing assets
- Misconfigured cloud storage
- Expired certificates and forgotten domains
- Third-party risks
Attack surface management provides a unified view. It connects these gaps and helps teams act faster.
Attack surface management vs attack surface monitoring
It is important to understand the difference. Attack surface monitoring focuses on visibility. It tracks changes and alerts teams when new risks appear.
Attack surface management goes further. It includes governance, prioritisation, and remediation workflows. It is a strategic approach that integrates with broader security programmes. If you want a deeper dive into monitoring, you can explore our dedicated blog on attack surface monitoring. It explains how continuous visibility works and why it is essential.
Think of monitoring as a component and management as the full lifecycle.
Real-world attack surface management scenarios
Attack surface management becomes clearer when you look at practical use cases. Below are four scenarios we commonly encounter.
1. Cloud misconfiguration exposure
A large enterprise deploys multiple cloud storage buckets for different teams. One of these buckets is accidentally left public. It contains sensitive customer data. Without attack surface management, this exposure could go unnoticed for weeks. With attack surface management in place:
- The asset is discovered automatically
- Misconfiguration is flagged based on risk
- The issue is prioritised due to data sensitivity
- The team receives actionable remediation steps
This reduces the window of exposure significantly.
2. Shadow IT and forgotten assets
A development team creates a test environment using a temporary domain. The project ends, but the domain remains active. It still runs outdated software with known vulnerabilities. Attackers scan for such forgotten assets. Attack surface management helps by:
- Identifying unknown domains linked to the organisation
- Detecting outdated components
- Highlighting the risk of exploitation
- Enabling quick decommissioning
Small oversights like this often lead to major breaches.
3. Third-party risk exposure
An organisation integrates with a third-party vendor for payment processing. The vendor’s API has a vulnerability. This creates a potential entry point into the organisation’s systems. Traditional security tools may not detect this risk. Attack surface management provides visibility into external dependencies. It helps organisations:
- Map third-party connections
- Assess their security posture
- Monitor for vulnerabilities
- Take proactive action when risks arise
This is especially important as supply chain attacks continue to rise.
4. AI-driven application exposure
An organisation deploys an AI-powered chatbot integrated with internal systems. The chatbot exposes an API endpoint that lacks proper authentication. Attackers discover this and use it to extract sensitive data or manipulate responses. Attack surface management helps detect such risks early by:
- Discovering AI-related assets and endpoints
- Identifying insecure API configurations
- Assessing data exposure risks
- Enabling secure deployment practices
As AI adoption grows, this scenario is becoming more common.
Myriad benefits of attack surface management
Attack surface management delivers measurable outcomes when implemented correctly.
- Improved visibility across environments: You gain a complete inventory of assets. Known and unknown. This clarity helps teams make informed decisions and reduce blind spots.
- Faster risk reduction: By prioritising critical risks, teams can act quickly. This reduces the chances of exploitation and limits potential damage.
- Better alignment with business risk: Attack surface management connects technical issues with business impact. This makes it easier for leadership to understand and support security initiatives.
- Continuous security improvement: Security is not static. Attack surface management ensures that your defences evolve with your environment.
How to implement attack surface management effectively
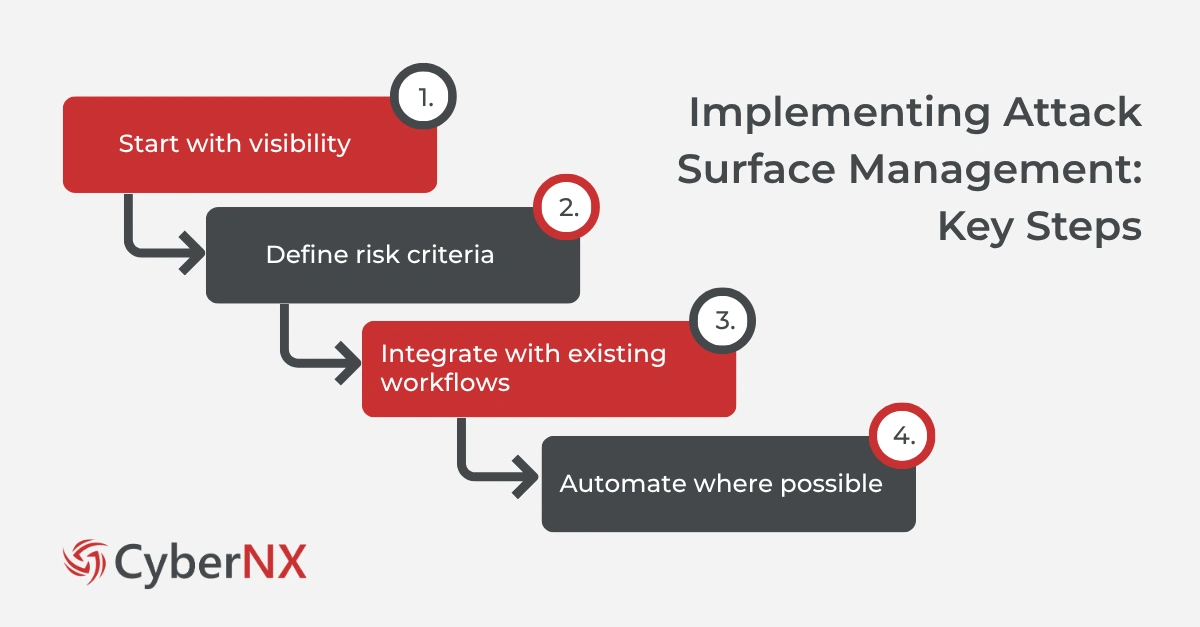
Adopting attack surface management requires more than just tools. It needs a structured approach.
- Start with visibility: Begin by identifying all external and internal assets. Use automated tools to maintain an up-to-date inventory.
- Define risk criteria: Not all risks are equal. Establish clear criteria based on business impact, data sensitivity, and exposure level.
- Integrate with existing workflows: Attack surface management should not operate in isolation. Integrate it with vulnerability management, incident response, and DevSecOps processes.
- Automate where possible: Manual processes cannot keep up with dynamic environments. Automation helps scale your efforts and reduce human error.
Conclusion
Attack surface management gives organisations the clarity they need to stay ahead of evolving threats. It moves beyond simple visibility and focuses on continuous risk reduction.
As environments grow more complex, having a structured and proactive approach becomes essential.
We work closely with organisations to simplify this process. From identifying unknown assets to prioritising critical risks, our approach focuses on practical outcomes. If you are looking to strengthen your security posture, we can help you build and implement an effective attack surface management strategy tailored to your environment. For more details about our digital risk protection services, connect with us.
Attack surface management FAQs
How is attack surface management different from vulnerability management?
Vulnerability management focuses on identifying and fixing known weaknesses. Attack surface management includes this but also covers asset discovery, exposure analysis, and continuous monitoring.
Can attack surface management help with compliance requirements?
Yes. It supports compliance by maintaining asset visibility, identifying risks, and ensuring continuous monitoring of exposed systems.
Is attack surface management only for large enterprises?
No. Any organisation with digital assets can benefit. Even smaller organisations face risks from exposed systems and shadow IT.
How often should attack surface management be performed?
It should be continuous. Modern environments change frequently, so periodic assessments are not sufficient.