“Reputation takes years to build and seconds to lose.” – Warren Buffett
In the digital economy, that loss doesn’t start inside the corporate network. It usually begins somewhere outside the organisation’s visibility. For example, a phishing domain appearing using your company’s name, or a fake mobile application mimics your brand in app store.
Security teams often discover these threats only after customers or regulators raise concerns.
This is where digital risk monitoring becomes critical. Instead of waiting for incidents to happen, companies continuously track their external digital footprint to detect threats early.
For CISOs and security leaders, digital risk monitoring has become a core component of modern cybersecurity strategy.
This guide talks about the most important real-world use cases and how organisations use monitoring intelligence to reduce digital threats.
What is digital risk monitoring for enterprises?
Digital risk monitoring refers to the continuous monitoring of external digital environments to identify threats that affect an organisation’s brand, employees, customers and data.
Unlike traditional cybersecurity tools that focus on internal systems, digital risk monitoring for enterprises focuses on external exposure.
Security teams monitor areas like:
- Phishing domains and fake websites
- Brand impersonation on social platforms
- Credential leaks in breach databases
- Dark web marketplaces selling stolen data
- Mobile applications impersonating corporate brands
- Fraud campaigns targeting customers
These external signals provide the earliest indicators of security risk.
Why digital risk monitoring matters for modern enterprises
Modern organisations operate across multiple digital ecosystems. Corporate websites, social platforms, cloud services, marketplaces and mobile apps create an extended digital footprint.
This expanded footprint increases the attack surface.
Without structured digital risk monitoring, organisations may miss early signs of:
- Brand impersonation attacks
- Credential compromise
- Customer fraud campaigns
- Data exposure incidents
Security teams increasingly treat digital risk monitoring as a proactive intelligence layer that complements other cybersecurity controls.
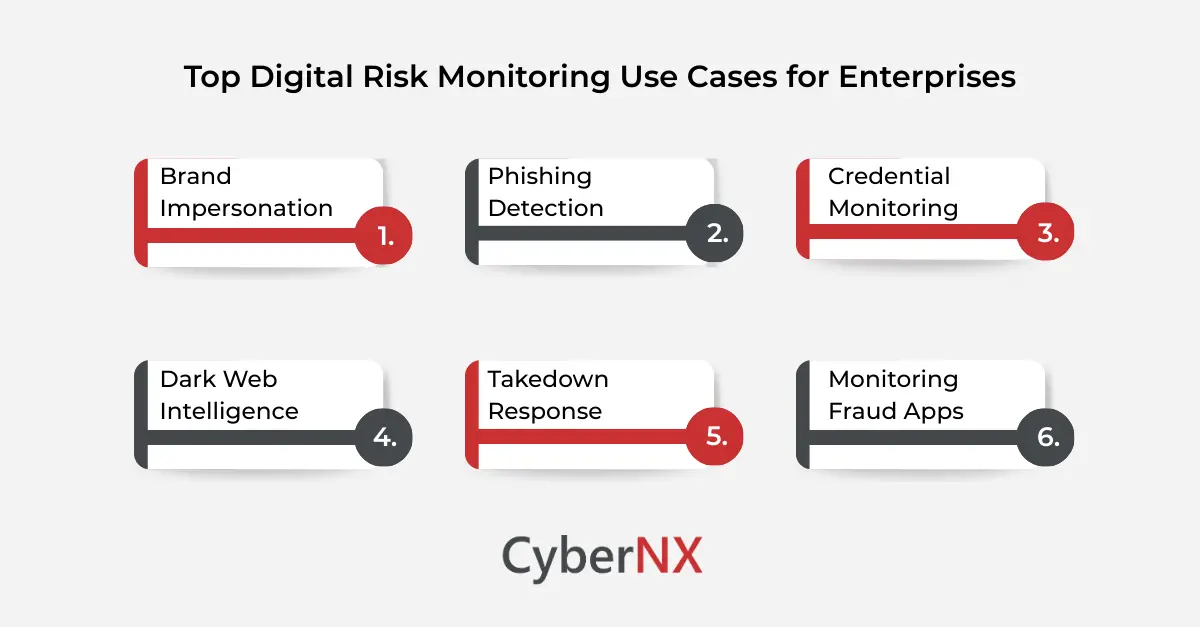
Top use cases of digital risk monitoring for enterprises
Digital risk monitoring supports multiple security objectives. Below are some of the most practical use cases security leaders rely on today:
Detecting brand impersonation and fake domains/Brand impersonation
Brand impersonation remains one of the most common external threats.
Attackers often register domains that closely resemble legitimate company websites to conduct phishing campaigns or fraud.
Digital risk monitoring helps organisations detect:
- Typosquatted domains
- Fake corporate websites
- Fraudulent landing pages targeting customers
- Brand misuse across global domain registrations
For enterprises operating globally, early detection prevents reputational damage and financial loss.
Identifying phishing campaigns targeting customers/ Phishing detection
Phishing attacks often leverage trusted brands to trick users into revealing sensitive information.
Attackers may create fake login pages or impersonate corporate support teams.
Digital risk monitoring for enterprises helps detect phishing infrastructure before campaigns escalate.
Security teams can identify:
- Newly registered phishing domains
- Fake customer support websites
- Fraudulent payment pages
- Email infrastructure used in phishing campaigns
Early detection allows organisations to initiate takedown actions before customers are affected.
Monitoring leaked credentials and exposed data/ Credential monitoring
Credential theft is one of the leading causes of security breaches. Employee usernames and passwords often appear in underground forums or breach databases after incidents involving third-party services.
Monitoring exposed credentials lets organisations respond fast.
Security teams can:
- Reset compromised accounts
- enforce stronger authentication controls
- identify potential insider risks
- investigate related security incidents
Credential monitoring is one of the most valuable capabilities in digital risk monitoring for enterprises.
Tracking dark web activity related to the organisation/ Dark web intelligence
Cybercriminal communities often discuss vulnerabilities, stolen credentials or potential attacks in underground forums.
Monitoring these discussions provides valuable threat intelligence.
With digital risk monitoring for enterprises, organisations gain visibility into:
- Data leaks posted in dark web forums
- Access sales involving corporate networks
- Discussions about potential attacks
- Threat actor chatter related to specific companies
This intelligence helps security teams detect risks before they escalate.
Protecting executives from impersonation/ Takedown response
Executive impersonation attacks have increased a lot in recent years.
Threat actors create fake profiles of senior executives on social media or messaging platforms to conduct fraud campaigns.
Digital risk monitoring allows organisations to track:
- Fake LinkedIn or social media profiles
- Messaging impersonation attempts
- Fraudulent investment or recruitment scams
- Brand misuse targeting partners or customers
Protecting executive identity is an increasingly important use case for digital risk monitoring for enterprises.
Monitoring fraudulent mobile applications/Monitoring fraud apps
Mobile app impersonation is another major threat. Attackers may release malicious apps disguised as official corporate apps to steal user data.
Digital risk monitoring helps detect:
- Fake apps using company branding
- Unofficial APK distribution websites
- App store impersonation listings
- Fraudulent updates targeting customers
Early detection helps organisations remove malicious applications quickly.
How enterprises operationalise digital risk monitoring
Monitoring external threats requires more than automated tools. Organisations must integrate monitoring intelligence into security operations.
Security leaders usually implement the following process:
- Identify the organisation’s external digital footprint
- Monitor digital ecosystems continuously
- Validate potential threats
- Prioritise high-risk exposures
- Initiate takedown or remediation actions
This structured workflow makes sure that digital risk monitoring for enterprises gives actionable security intelligence.
Common challenges organisations face with digital risk monitoring
While digital risk monitoring provides valuable insights, companies often face many operational challenges.
- Alert overload: Monitoring platforms may generate large volumes of alerts.
- Threat validation: Security teams must verify whether signals represent genuine risk.
- Response coordination: Removing malicious domains or social profiles requires coordination with multiple platforms.
- Resource constraints: Many organisations lack dedicated teams to manage external threat monitoring.
These challenges highlight the importance of specialised monitoring services.
Conclusion
External threats evolve much faster than traditional security controls.
Phishing domains, credential leaks and brand impersonation campaigns often originate outside the corporate network. Without visibility into these environments, organisations find out incidents too late.
This is why digital risk monitoring for enterprises has become a key part of modern cybersecurity programs.
We work with security teams to monitor and manage their digital footprint with precision. If you want a clear view of what is truly exposed and how to reduce risk quickly, you can start with a focused assessment tailored to your environment.
Speak with our experts to learn more about our digital risk protection services and turn your digital monitoring strategy into a living defence system.
Digital risk monitoring FAQs
What is digital risk monitoring for enterprises?
It is the process of continuously monitoring external digital environments like domains, social platforms, dark web forums and marketplaces. The purpose is to identify threats targeting an organisation.
Why is digital risk monitoring important for enterprises?
It helps firms detect phishing campaigns, credential leaks, brand impersonation and other external threats before they affect customers or internal systems.
What industries benefit most from digital risk monitoring?
Industries like banking, financial services, healthcare, e-commerce and technology companies benefit greatly because they handle large volumes of sensitive data.
Can digital risk monitoring prevent cyberattacks?
It does not prevent attacks directly. But it provides early warning signals that allow companies to respond fast and reduce potential damage.
How often should enterprises monitor digital risks?
Digital risks should be monitored continuously, because threat actors operate around the clock across global digital platforms.