Dark web monitoring is a must-have for organisations in the age of digitization, AI and unprecedent advancements in tech-innovations. A vendor might promise to alert you the moment your data appears on hidden dark web forums. But many times, when you decide to look closer, those details might feel vague. It is, therefore, crucial to evaluate a dark web monitoring services with questions such as What exactly is being monitored? How often? What happens after an alert? Without clarity, you risk paying for noise rather than intelligence.
This dark web monitoring checklist gives you a practical framework. It helps you assess what an organisation should monitor and how to evaluate a vendor’s capability with confidence.
Why finding a dark web monitoring vendor is complicated
Before we explore the dark web monitoring checklist, it helps to understand the common pain points.
1. Lack of visibility into sources
Vendors often say they monitor “thousands of dark web sites”. That sounds impressive. But which sites? Are they high risk ransomware leak sites? Closed forums? Telegram channels? Or recycled data dumps? Without transparency, you cannot judge coverage.
2. Too many false positives
Raw data dumps are easy to collect. Contextual intelligence is harder. Many teams receive alerts for old breaches or irrelevant data, which wastes analyst time and reduces trust. Right dark web monitoring tools should be used to retrieve valuable information, which in turn, can assist security teams to curb the damage.
3. No link to business risk
An alert that says “email found on dark web” means little on its own. Security leaders need to know:
- Is the password exposed?
- Is it reused?
- Does it link to privileged access?
- Is there active threat chatter?
If the vendor cannot translate data into risk, the value drops quickly.
4. Weak incident response alignment
Some providers send alerts but offer no guidance. Others delay notifications. In a live ransomware situation, hours matter. This is where a clear dark web monitoring checklist becomes critical.
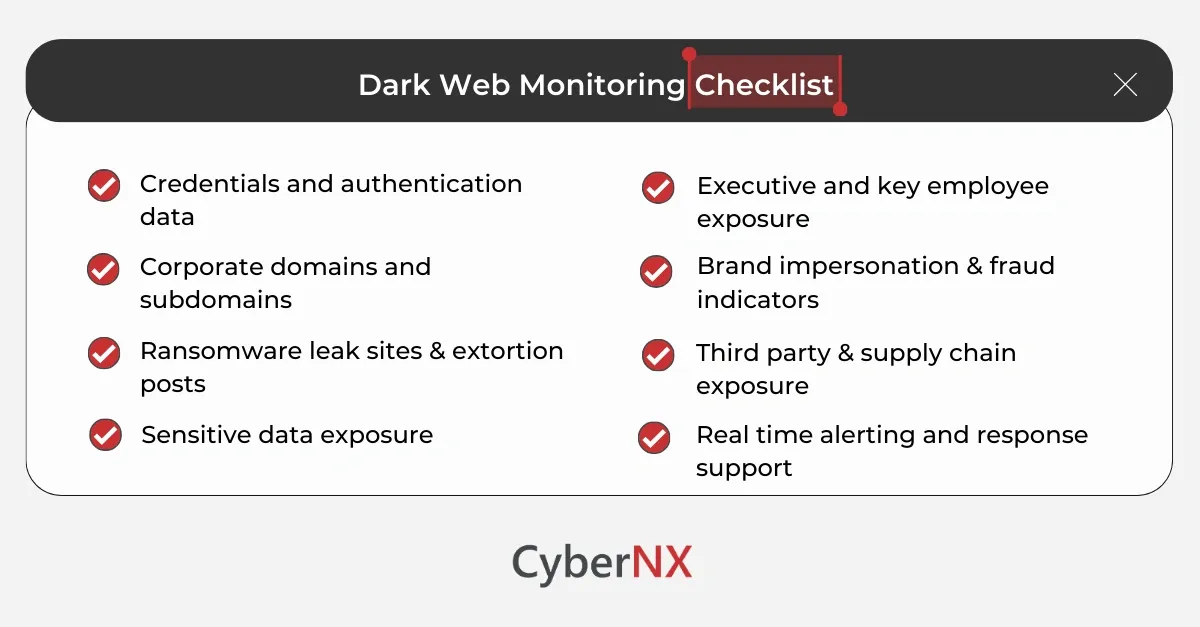
Dark web monitoring checklist: what every organisation should monitor
Before you sign with a vendor, use this checklist to validate coverage, depth, and actionability.
1. Credentials and authentication data
Compromised credentials are still the primary entry point for attackers.
Your monitoring should include:
- Corporate email addresses across all domains
- Leaked passwords in plaintext or hashed form
- Credential pairs from stealer logs
- Privileged accounts and admin emails
- VPN, RDP and cloud login references
Ask the vendor how they differentiate between old breach data and fresh credential exposure. Real value lies in identifying newly compromised accounts quickly.
2. Corporate domains and subdomains
A strong checklist includes full domain visibility. Ensure monitoring covers:
- Primary corporate domains
- Subsidiary domains
- Legacy domains
- Cloud service subdomains
Threat actors often test forgotten assets. We have seen cases where an old acquisition domain becomes the weak link. Ask how the vendor maps domain ownership and discovers related assets.
3. Ransomware leak sites and extortion posts
Modern ransomware groups publish stolen data to pressure victims. Monitoring must include:
- Known ransomware leak blogs
- Data auction announcements
- Extortion posts naming your organisation
- Mentions in threat actor discussions
A vendor should not just notify you of publication. They should track threat actor activity patterns and alert you early if your name appears in pre-publication chatter.
4. Sensitive data exposure
Your checklist must go beyond credentials. Look for monitoring of:
- Financial records
- Internal documents
- Source code
- Customer databases
- Intellectual property
- API keys and tokens
Ask how the vendor validates authenticity. Is it real internal data or recycled samples from public breaches?
5. Executive and key employee exposure
Senior leaders are prime targets for spear phishing and business email compromise.
Monitoring should cover:
- Executive email addresses
- Board members
- Finance team members
- IT administrators
- Developers with privileged access
Some vendors also monitor doxxing attempts and personal data leaks. This can reduce targeted social engineering risk.
6. Brand impersonation and fraud indicators
Attackers often use your brand to deceive customers and partners. Your monitoring checklist should include:
- Fake domains similar to yours
- Fraud campaigns discussed on forums
- Sale of branded phishing kits
- Discussions about exploiting your organisation
Early detection here protects both revenue and reputation.
7. Third party and supply chain exposure
Your security posture depends on your partners.
Advanced monitoring should track:
- Mentions of key suppliers
- Breaches affecting critical vendors
- Data dumps referencing shared credentials
Ask if the vendor can monitor specific partner domains relevant to your ecosystem.
8. Real time alerting and response support
Monitoring without response creates risk.
Evaluate:
- Alert frequency and latency
- Severity scoring methodology
- Integration with your SIEM or SOC
- Access to analyst validation
- Guidance for containment
A good vendor supports your team with context and recommended actions. We believe this is where monitoring becomes risk reduction.
Evaluating vendor capability using this checklist
Once you review what to monitor, assess how the vendor operates.
- Source diversity and access: Do they access closed communities or only surface indexed content? Ask for examples of unique findings.
- Human intelligence versus automation: Automation collects data fast. Human analysts validate context. You need both. Confirm whether analysts review critical alerts.
- Reporting clarity: Reports should translate technical findings into business impact. CISOs need executive ready summaries, not raw data feeds.
- Compliance alignment: Check whether the service supports regulatory needs such as breach detection obligations or third-party risk management documentation.
- Data privacy and legal considerations: Monitoring must follow legal boundaries. Ask how the vendor ensures lawful collection and handling of data.
Using a structured checklist makes vendor evaluation objective rather than emotional.
Conclusion
Dark web monitoring can strengthen your threat detection strategy. Yet value depends on clarity, coverage, and response capability.
This dark web monitoring checklist helps you ask the right questions. It ensures you monitor credentials, sensitive data, ransomware leaks, executive exposure, brand misuse, and supply chain risk with context and speed.
If you want to evaluate your current provider or explore a more intelligence led approach, our team can help. Contact us to know more about our dark web monitoring services to turn signals into practical action.
Dark web monitoring checklist FAQs
How often should dark web monitoring alerts be reviewed?
Critical alerts should be reviewed immediately. Routine intelligence can be reviewed daily or weekly depending on your risk profile and industry exposure.
Can dark web monitoring prevent breaches?
It does not prevent breaches directly. However, it helps detect exposed credentials, stolen data, and attacker activity early, which reduces impact and dwell time.
Is dark web monitoring only relevant for large enterprises?
No. Mid-sized organisations are frequently targeted because attackers expect weaker controls. Monitoring supports visibility regardless of company size.
How does dark web monitoring differ from threat intelligence feeds?
Threat intelligence feeds provide broad indicators such as IP addresses or malware hashes. Dark web monitoring focuses on exposure specific to your organisation, such as leaked data and credentials.