CrowdStrike NG-SIEM is undoubtedly one of the advanced SIEM platforms for modern cybersecurity. In fact, it is seen as a bridge connecting SIEM, SOAR and EDR, aligning it more with detection and response solutions. That’s why we are doing this blog series covering different facets of CrowdStrike’s Next Generation SIEM.
For any SOC leader, knowing CrowdStrike NG-SIEM use cases is important to get full value out of it. By combining endpoint telemetry, threat intelligence and cloud-native analytics in a unified platform, SOC leaders can reduce noise and improve response speed. In this guide, we outline practical, enterprise-focused use cases that security teams can adopt to strengthen detection, streamline investigations and gain measurable value.
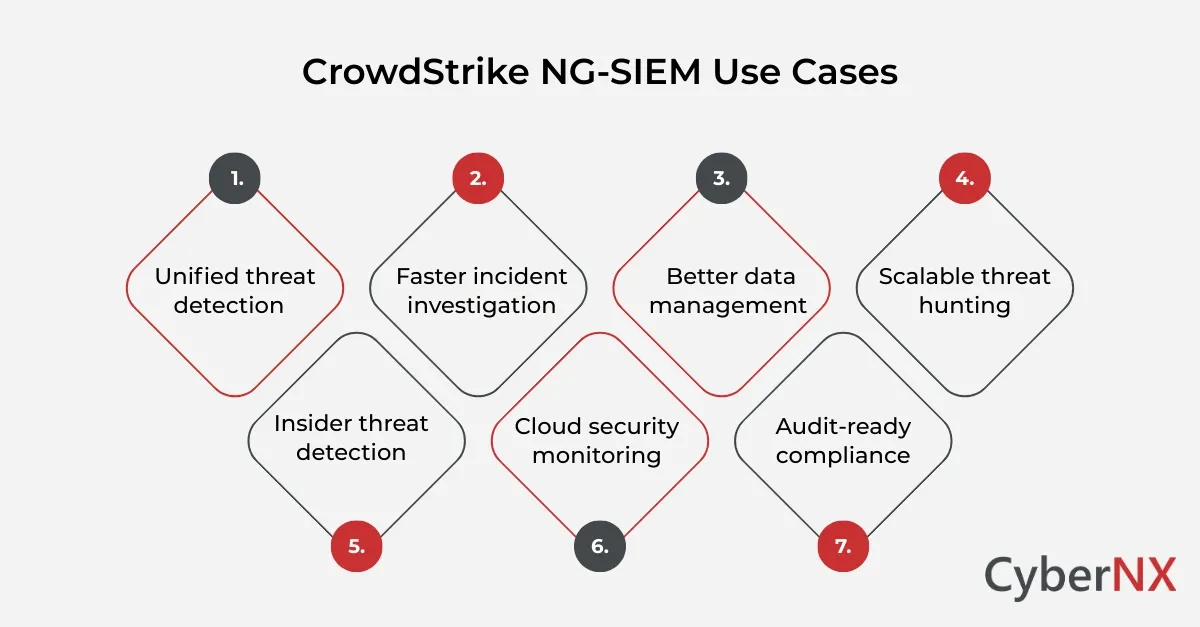
Key CrowdStrike NG-SIEM use cases for modern SOCs
Below are enterprise-relevant use cases that resonate with CISOs, SOC managers, and IT heads.
1. Unified threat detection
Fragmented visibility is one of the biggest SOC challenges.
With NG-SIEM, telemetry from endpoints, cloud workloads, identity systems, and third-party logs flows into a centralised detection engine. This improves context.
For example, an unusual login attempt combined with suspicious endpoint behaviour can trigger correlated alerts. Instead of two separate investigations, analysts see a unified incident view.
This reduces dwell time and improves response accuracy.
2. Faster incident investigation
Incident response often slows down because data sits in silos. Analysts must pivot between tools.
NG-SIEM reduces this friction by offering enriched events and pre-correlated data. Analysts can track:
- Process execution
- User behaviour
- Network connections
- Cloud API activity
All from a single interface.
The result is faster root cause identification. In our experience, streamlined telemetry correlation significantly reduces investigation time, sometimes by hours per incident.
3. Better data management
Many organisations struggle with unpredictable SIEM costs due to high log ingestion volumes.
Cloud-native architecture enables better data management strategies. Instead of ingesting everything blindly, organisations can prioritise high-value telemetry and archive lower-value logs intelligently.
This approach helps control cost without compromising detection depth. CFOs appreciate the predictability. SOC teams appreciate sustained visibility.
4. Advanced threat hunting at scale
Modern attackers use living-off-the-land techniques. Static rules are rarely enough.
NG-SIEM supports proactive threat hunting with large-scale telemetry access and powerful search capabilities. Analysts can query historical data efficiently to detect:
- Lateral movement patterns
- Suspicious PowerShell execution
- Credential misuse
- Cloud misconfigurations
Proactive hunting moves the SOC from reactive to investigative. That shift strengthens overall security posture.
5. Insider threat detection
Insider risks often go unnoticed because they appear as legitimate activity.
By correlating identity logs, endpoint behaviour, and access patterns, NG-SIEM can highlight anomalous user behaviour.
For instance, a privileged user accessing sensitive data outside business hours combined with unusual data transfer activity can trigger alerts.
This capability is particularly relevant for regulated sectors such as finance and healthcare.
6. Cloud-native security monitoring
As enterprises migrate to multi-cloud environments, monitoring becomes complex.
NG-SIEM provides visibility into:
- Cloud workload activity
- Container environments
- API calls
- SaaS interactions
Security teams gain centralised oversight across hybrid infrastructures. This is crucial for organisations adopting zero trust strategies.
7. Compliance reporting & audit readiness
Auditors often request detailed logs and evidence trails.
With centralised telemetry and searchable historical data, NG-SIEM simplifies compliance workflows. SOC teams can generate reports quickly without scrambling across multiple tools.
This improves audit confidence and reduces operational stress during compliance cycles.
Conclusion
Modern SOCs require visibility, speed, and cost efficiency. Legacy SIEM systems often create complexity without delivering agility.
CrowdStrike NG-SIEM offers a cloud-native, integrated approach that enhances detection, investigation, and threat hunting. Its ability to unify telemetry across endpoint, cloud, and identity makes it highly relevant for enterprise environments.
Technology alone will not solve security challenges. Strategy and execution matter equally. If you are evaluating your SOC maturity or planning SIEM modernisation, we can guide the journey.
Speak with our experts for a focused CrowdStrike Consulting and to assess how your SOC can evolve with confidence and clarity.
CrowdStrike NG-SIEM use cases FAQs
1. How can NG-SIEM support ransomware detection beyond endpoint alerts?
NG-SIEM can correlate endpoint behaviour with lateral movement, privilege escalation, and unusual file encryption patterns. By analysing cross-domain telemetry, it detects early indicators that may not trigger standalone endpoint alerts. This broader visibility helps contain ransomware before widespread impact.
2. Can NG-SIEM help in securing mergers and acquisitions environments?
Yes. During M and A activity, visibility gaps often emerge between integrating networks. NG-SIEM can centralise telemetry from both environments, identify misconfigurations, and detect suspicious access attempts. This ensures smoother and safer integration.
3. How does NG-SIEM assist in monitoring third-party vendor access?
It can track identity logs, remote access sessions, and behavioural anomalies linked to vendor accounts. By correlating access timing, device posture, and privilege use, SOC teams can quickly flag unusual third-party activity and reduce supply chain risk.
4. Can NG-SIEM enhance zero trust implementation efforts?
NG-SIEM strengthens zero trust strategies by validating user and device behaviour continuously. It correlates identity authentication events with endpoint and cloud activity. This provides ongoing verification instead of one-time access checks, improving policy enforcement visibility.