In the fast-paced world of cybersecurity, staying ahead of evolving threats requires more than just reactive measures. CISOs, CXOs, and IT Managers are constantly seeking proactive solutions to fortify their defenses. Continuous Automated Red Teaming (CART) is emerging as a game-changer, revolutionizing how organizations approach security testing. This blog will explore the intricacies of CART in cyber security, its benefits, and how it’s shaping the future of security.
What is Continuous Automated Red Teaming (CART)?
Continuous Automated Red Teaming (CART) is a methodology that leverages automation to simulate real-world cyberattacks on a continuous basis. It allows organizations to proactively identify vulnerabilities and assess their security posture in real-time. The CART represents a shift from periodic, manual red teaming to an ongoing, automated process.
The Evolution of Red Teaming: From Traditional to Automated
Red teaming has transformed from manual, time-intensive operations conducted by small expert teams. Today, it is sophisticated and automated system that can simulate complex attack scenarios at scale. This evolution represents a fundamental shift in how organizations approach cybersecurity testing and vulnerability assessment.
Traditional Red Teaming
Traditionally, red teaming involved manual penetration testing and vulnerability assessments conducted at specific intervals. While effective, this approach can be time-consuming and resource-intensive.
Check out our related blog post Red Teaming Guide for a deep-dive into the topic.
Challenges of Traditional Red Teaming
Traditional red teaming often suffers from limitations such as:
- Infrequent testing cycles, leaving gaps in security coverage.
- High costs associated with manual testing.
- Difficulty in scaling testing efforts to cover complex environments.
Continuous Automated Red Teaming (CART)
CART addresses the above challenges by automating key aspects of red teaming, enabling continuous testing and real-time feedback. This transition enhances the efficiency and effectiveness of security assessments. CART security has become a vital part of modern security strategy.
The Need for Continuous Automated Red Teaming (CART)
Organizations today face a constant barrage of cyberattacks. CART provides the following benefits:
- Continuous monitoring and testing to identify vulnerabilities promptly.
- Real-time feedback on security posture.
- Scalability to cover complex and evolving environments.
- Reduced reliance on manual testing, leading to cost savings.
How Does Continuous Automated Red Teaming Work?
Continuous Automated Red Teaming (CART) employs automated tools to simulate real-world cyberattacks, providing ongoing security assessments. The process involves:
- Defining Scope: Security teams configure the CART platform with specific attack scenarios and testing parameters, outlining the systems to be tested.
- Automated Simulations: CART runs continuous or scheduled simulations, mimicking various attack vectors like vulnerability exploitation, network penetration, and phishing.
- Real-Time Monitoring: The platform monitors systems for vulnerabilities and potential breaches, analyzing logs and network traffic for anomalies.
- Reporting and Alerts: Detailed reports and real-time alerts are generated, providing information on vulnerabilities and recommended remediation steps.
- Continuous Improvement: Insights from the simulations are used to refine security controls and improve incident response.
- Integration: CART integrates with existing security tools and workflows, enabling seamless automation and analysis.
Benefits of CART in Cybersecurity
CART (Continuous Automated Red Teaming) delivers ongoing, scalable threat simulations that mimic real-world attacks with precision and speed. It helps organizations stay ahead of evolving threats by enabling continuous testing, rapid feedback, and proactive defense tuning.
- Continuous Testing: Real-time vulnerability detection.
- Realistic Threat Simulations: Accurate representation of attack scenarios.
- Cost Efficiency: Reduced reliance on manual testing.
- Proactive Defense: Early identification of security gaps.
- Compliance: Continuous monitoring for regulatory requirements.
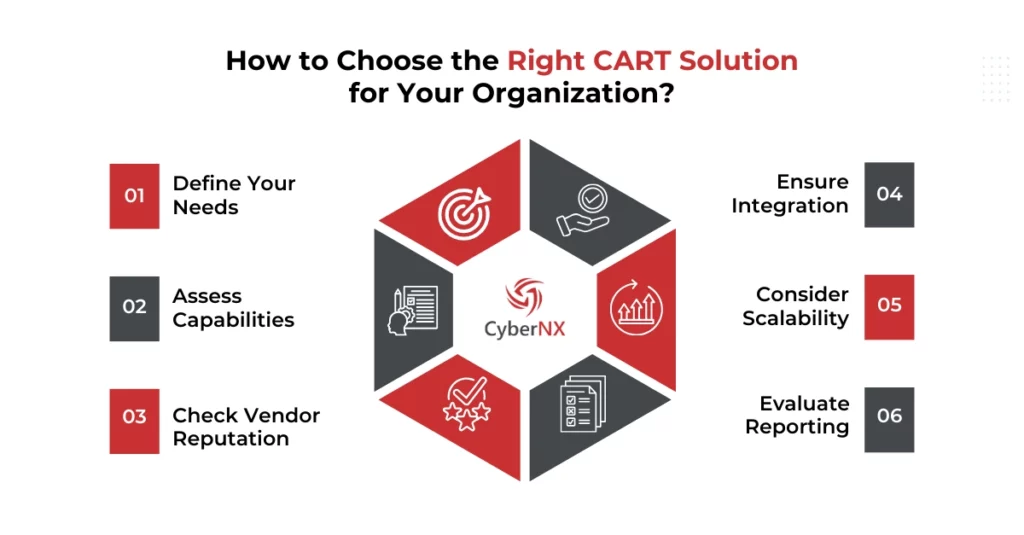
How to Choose the Right CART Solution for Your Organization?
Selecting the right CART solution is vital for your security. Consider these key factors:
- Define Your Needs: Identify your specific security challenges and required testing scope.
- Assess Capabilities: Evaluate the solution’s features, attack simulations, and integration potential.
- Check Vendor Reputation: Choose a reputable vendor with strong support and expertise.
- Ensure Integration: Verify seamless integration with your existing security tools.
- Consider Scalability: Ensure the solution can grow with your organization.
- Evaluate Reporting: Confirm the solution provides actionable vulnerability reports and analytics.
Conclusion
The shift towards Continuous Automated Red Teaming (CART) represents a pivotal leap in cybersecurity, moving from periodic assessments to a state of constant vigilance. By automating red team activities, organizations gain the ability to proactively identify and mitigate vulnerabilities. It significantly enhances security posture while optimizing resource allocation.
This continuous approach, however, relies on a strong foundation of red teaming expertise to configure and interpret the results effectively. To truly leverage the power of CART, a deep understanding of offensive security is paramount.
Ready to harness the power of CART and elevate your security? Our expert red teaming services provide the foundational knowledge and implementation support. Plus, you will be able to maximize the benefits of automated security assessments with us. Discover how our tailored solutions can help you proactively identify and mitigate vulnerabilities.
Continuous Automated Red Teaming FAQs
What types of attack scenarios can CART simulate beyond standard penetration tests?
Unlike traditional penetration tests that are time-bound and often narrow in scope, CART platforms simulate a wide spectrum of real-world attack scenarios. These include phishing campaigns, credential theft, ransomware deployment, privilege escalation, lateral movement within internal networks, and even simulated data exfiltration. This allows organizations to test their entire kill-chain resilience across people, processes, and technology – continuously and dynamically.
How does CART integrate with existing security tools like SIEM and SOAR?
CART platforms are designed to work in tandem with your existing security ecosystem. They can push simulated attack data and findings directly into SIEM platforms for log correlation and alert generation, and into SOAR systems for automated response playbooks. This integration ensures that simulated threats are treated like real incidents, helping teams validate detection rules, automate remediation workflows, and identify gaps in incident response readiness.
What are common implementation challenges organizations face with CART?
Implementing CART isn’t plug-and-play. Challenges often include integrating with complex, hybrid IT environments; ensuring simulations don’t disrupt critical business services; managing false positives from attack detection; and keeping the attack library current with evolving threat tactics. Additionally, gaining organizational buy-in and aligning simulations with specific business risks and compliance requirements can require cross-functional coordination.
How often should CART simulations run to be effective?
The effectiveness of CART lies in its frequency. Ideally, simulations should run continuously or on a frequent, automated schedule – such as daily or weekly – depending on the organization’s risk posture, compliance obligations, and resource availability. Continuous testing helps security teams detect vulnerabilities and misconfigurations in near real-time, significantly reducing the window of exposure and enabling faster remediation before real attackers can exploit them.