Implement or Remediate Your Cloud Security with
Cloud Security Implementation & Remediation Services
Ensure readiness for cloud migrations or fixing security loopholes in existing deployments.
Talk to our Experts Today




















INTRODUCTION
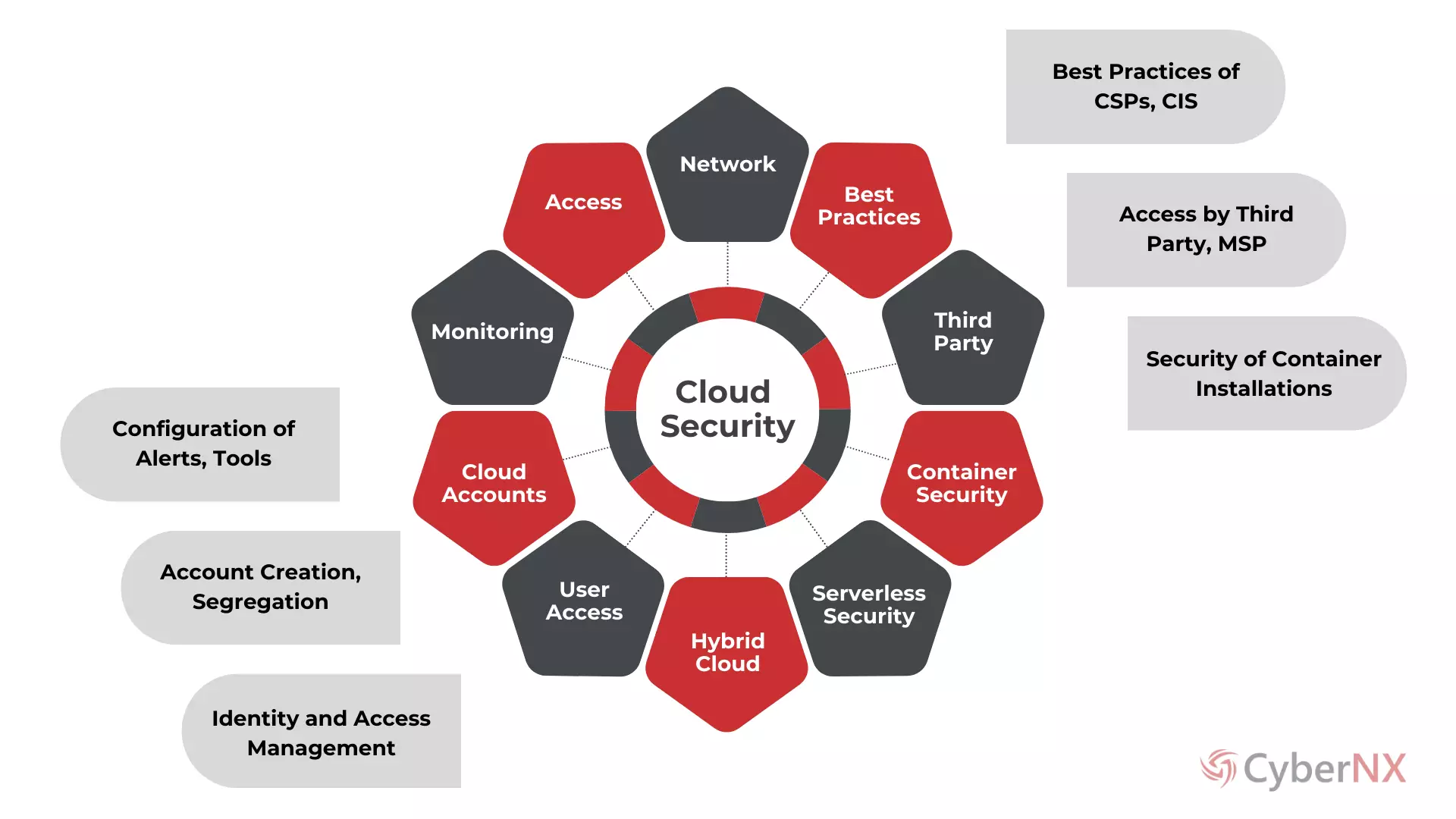
Cloud Security Implementation and Remediations with CybeNX Specialists
CyberNX Cloud Security Implementation and Remediation services are designed to ensure your readiness for migrations to cloud infrastructures or assessing existing cloud setup. We help you prevent long-term damage and significant financial loss.

We address your key challenges:
Remediate security misconfigurations in the cloud environment that could become security incidents.
Cloud infrastructure must be aligned with the best practices recommended by Cloud Service Provider (CSP) and industry standards.
Cloud infrastructure must compliant with regulatory requirements such as RBI, SEBI, or IRDA.
Organizations must have a cloud security governance practice in place that aligns with its security policy.
An effective cloud security monitoring practice established to detect and respond to security threats in real-time.
Critical cloud components such as virtual machines (VMs), storage buckets, load balancers, and containers must be securely configured and deployed.
PROCESS
How It Works?
Connect with our Team of Cloud Security Specialists!
APPROACH
Why CyberNX for Cloud Security Implementation?
Cutting-Edge Tools
Client-Centric Approach
Risk Mitigation
Actionable Insights
Regulatory Compliance
Customer first Approach is our guiding principle.
BENEFITS
Expert Cloud Security Implementation & Remediation Services
Highly Specialised Professionals
We bring extensive experience in implementation and remediation of diverse cloud environments across various industries.
Comprehensive Security Controls
We provide a thorough evaluation and control implementation in your cloud environment.
Technical Insights and Recommendations
We help you with actionable technical insights and recommendations to prioritize the remediations as per threat profile.
Enhanced Incident Response Preparedness
We help you to improve incident detection and response capabilities by developing incident response procedure.
Documentation and Reporting
We provide you a comprehensive report with remediations implemented - valuable for stakeholders, IT teams, and auditors.
For Customized Plans tailored to Your Needs,
Get in Touch Today!
FAQ
Frequently Asked Questions
RESOURCES