“It takes 20 years to build a reputation and five minutes to ruin it.” – Warren Buffett
In today’s digital ecosystem, it may not even take five minutes.
Your brand is no longer protected by perimeter security alone. It lives on search engines, social platforms, marketplaces, mobile apps, domain registries, code repositories and even dark web forums. Every digital touchpoint creates exposure. And every exposed surface creates risk.
For CISOs and CXOs, brand risk monitoring is no longer a marketing concern. It is a cybersecurity responsibility.
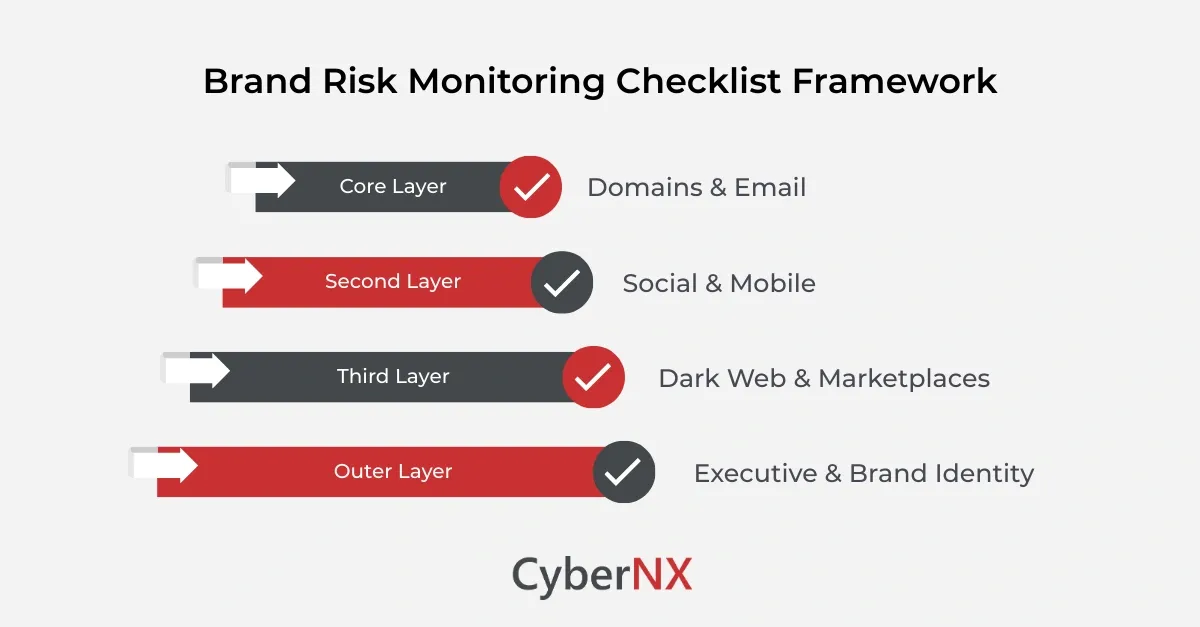
This brand risk monitoring checklist is designed to help you identify what must be protected and controlled before brand damage converts into a business incident.
What is brand risk monitoring?
Brand risk monitoring is the continuous process of identifying, detecting and responding to threats that misuse your brand identity or digital assets.
It includes tracking:
- Impersonation domains
- Phishing campaigns
- Fake social media accounts
- Dark web data leaks
- Mobile app clones
- Credential exposure
- Marketplace fraud
A structured brand risk monitoring checklist makes sure that protection efforts are proactive rather than reactive.
Why brand risk monitoring is now a board-level priority
Brand abuse today is not isolated.
A phishing domain impersonating your company can lead to:
- Credential theft
- Financial fraud
- Customer distrust
- Regulatory scrutiny
Dark web leaks can expose employee credentials, API keys or even internal data.
Fake mobile apps can extract sensitive user information.
This is why a formal checklist is becoming part of enterprise cybersecurity strategy.
Brand risk monitoring checklist: what should you protect
Below is a structured checklist designed for enterprise security leaders.
Before using any tools, you must clarify your exposure surface. Brand risk monitoring must cover the full digital ecosystem.
1. Domain ecosystem
Attackers often register typo-squatted or lookalike domains.
Protect and monitor:
- Misspelled domain variants
- Different TLD combinations
- Newly registered domains that are similar to your brand
- Parked domains using your name
2. Email spoofing and phishing infrastructure
Phishing campaigns are one of the most damaging forms of brand abuse.
Check for:
- Unauthorized SPF/DKIM configurations
- Email spoofing attempts
- Phishing landing pages
- Bulk phishing domain registrations
Early detection prevents reputational and financial impact.
3. Social media impersonation
Fake profiles can damage customer trust quickly.
Track:
- Impersonation accounts
- Fake customer support pages
- Fraudulent promotions
- Suspicious engagement spikes
Social monitoring is an essential layer within your brand risk monitoring checklist.
4. Dark web and deep web exposure
Brand-related data leaks often appear in underground forums before they reach mainstream channels.
Monitor for:
- Leaked employee credentials
- Stolen customer data
- Internal document dumps
- Mentions of your brand in online adversary communities
Dark web visibility transforms brand monitoring from reactive to intelligence-driven.
5. Mobile app cloning
Fraud apps mimicking your brand can affect users directly.
Check for:
- App store lookalikes
- Unauthorized APK distribution
- Brand misuse in app descriptions
- Counterfeit versions of official applications
Mobile ecosystem monitoring is often overlooked in traditional security programs.
6. Marketplace and e-commerce fraud
If your brand sells products, counterfeit listings can reduce revenue and trust.
Monitor:
- Fake seller accounts
- Counterfeit product listings
- Unauthorized discount campaigns
- Brand misuse in marketplace ads
This expands your checklist into digital commerce ecosystems.
7. Executive impersonation
C-level impersonation attacks are rising.
Monitor for:
- Fake LinkedIn profiles
- Impersonation emails
- Fraudulent WhatsApp or messaging accounts
- Business email compromise attempts
Executive identity monitoring protects both leadership and the organisation’s credibility.
How to operationalise your brand risk monitoring checklist
A checklist is only effective if operationalised.
Security leaders should:
- Define ownership: Brand monitoring should be owned jointly by security and digital risk teams.
- Establish detection thresholds: Not every mention is a threat. Define severity tiers.
- Integrate with incident response: Brand threats must feed into SOC workflows.
- Automate monitoring intelligence: Manual search is insufficient. Continuous intelligence feeds are required.
- Conduct periodic risk reviews: Review the brand risk monitoring checklist quarterly to adapt to new threats.
Common mistakes in brand risk monitoring
Even mature organisations make avoidable errors.
- Ignoring domain sprawl: Failing to monitor newly registered domains creates blind spots.
- Treating social monitoring as marketing: Security must be involved in impersonation detection.
- Neglecting dark web intelligence: Brand data exposure often surfaces in underground communities first.
- Operating without response workflows: Detection without action does not reduce risk.
A structured brand risk monitoring checklist reduces these gaps.
When should enterprises implement a brand risk monitoring program
Brand monitoring should not begin after a phishing incident.
Implement it when:
- Expanding digital presence
- Launching new products
- Entering international markets
- Increasing online transactions
- Handling sensitive customer data
In 2026, brand abuse is inevitable and your preparedness will determine impact.
Conclusion
Trust and reliability are very important factors for the success of a brand. A structured brand risk monitoring checklist can help you move from reactive takedowns to proactive threat intelligence.
Brand abuse, impersonation, phishing and dark web exposure are no longer isolated incidents. They are systemic risks tied directly to revenue, compliance and customer trust.
We support firms with structured brand risk monitoring (BRM) and dark web monitoring services powered by advanced technology, real-time alerts, global coverage, expert analysis, proactive detection and compliance-aligned reporting.
If you want to strengthen your firm’s digital brand resilience, connect with us to build a structured and proactive brand risk monitoring program tailored to your specific environment.
Brand Risk Monitoring Checklist FAQs
How often should a brand risk monitoring checklist be reviewed?
At minimum quarterly, or immediately after major digital expansion initiatives.
Is brand risk monitoring only relevant for large enterprises?
No. Any organisation with digital presence, customer interaction or online transactions requires monitoring.
Does brand risk monitoring replace traditional cybersecurity controls?
No. It complements existing controls by focusing on external threat exposure.
What is the role of dark web monitoring in brand protection?
Dark web monitoring helps detect leaked credentials, data exposure, and brand mentions in threat actor communities before damage escalates.
Who should own brand risk monitoring within an organisation?
It should be jointly managed by cybersecurity, digital risk and executive stakeholders.