In 2020, cybercriminals launched a wave of phishing campaigns impersonating global brands like Microsoft, Amazon, PayPal etc. The infrastructure behind these attacks consisted of fake domains, cloned websites, impersonated accounts and often existed days or even weeks before detection.
It led to reputational damage. Customers lost trust, fraud incidents increased and support teams were overwhelmed.
This is the reality modern firms face today. Your brand is no longer limited to your official website or owned channels. It exists across search engines, social platforms, marketplaces, mobile apps, and even underground forums.
And attackers know exactly how to exploit it. This is where brand abuse monitoring becomes critical.
This guide explains what brand abuse monitoring is, why it matters, and how companies can build an effective monitoring strategy to detect and respond to threats before they escalate.
What is brand abuse monitoring?
To put in simple words, brand abuse is any activity where someone illegally uses a company’s logo, name, or identity to deceive customers or to purposely harm the business. Brand abuse monitoring is the process of continuously identifying, tracking and responding to such threats across digital platforms.
This includes detecting:
- Fake domains and phishing websites
- Impersonation on social media
- Fraudulent mobile applications
- Unauthorized use of brand assets
- Credential leaks linked to brand campaigns
The goal of brand abuse monitoring is to identify threats early, prevent customer impact and protect brand trust.
Why brand abuse monitoring is now a security priority
Brand abuse is no longer just a marketing or legal concern. It is a cybersecurity issue.
Attackers increasingly use brand impersonation as an entry point for:
- phishing campaigns
- financial fraud
- credential harvesting
- malware distribution
Without brand abuse monitoring, companies discover these threats only after customers report fraud. By that time, the damage is already done. For CISOs and security leaders, brand abuse monitoring provides visibility into external threats that traditional security tools cannot detect.
Common types of brand abuse enterprises face
Brand abuse can take many forms. Understanding these attack patterns helps you build stronger monitoring strategies.
Fake websites
Attackers register sites that resemble legit brand names. These domains are then used to perform harmful tasks:
- host phishing pages
- collect customer info
- distribute harmful content
Social media impersonation
Fake profiles impersonate executives, customer support teams or official brand accounts. These accounts often target customers with scam offers, phishing links and support scams.
Mobile app impersonation
Attackers publish harmful apps that look like legitimate applications. These apps can steal login passwords, sensitive data and even install harmful viruses.
Data leaks and credential exposure
Stolen credentials associated with your firm may appear on breach databases, underground forums and cybercrime marketplaces like the ones on dark web. Monitoring these sources is an important part of brand abuse monitoring.
Why traditional monitoring approaches fail
Many firms depend on disconnected monitoring tools or reactive processes.
This mismatch creates several gaps:
- limited visibility across digital platforms
- delayed detection of impersonation attacks
- lack of correlation between threat signals
- inability to prioritise risks effectively
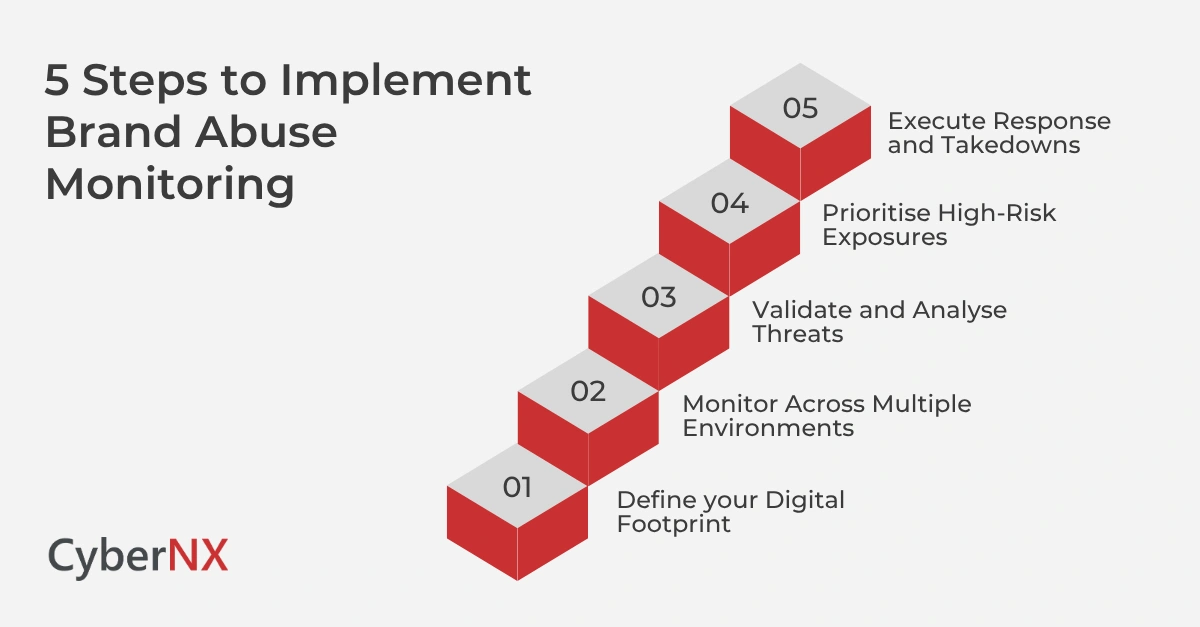
How to build an effective brand abuse monitoring strategy
A strong monitoring strategy needs a lot more than tools. It needs a structured and intelligence-driven approach. When done right, it helps organisations stay ahead of attackers, reduce fraud, and protect customer trust at scale. Security teams that are implementing brand abuse monitoring should follow these key steps.
Define your digital footprint
Start by identifying and maintaining a living inventory of all brand-linked assets across the digital ecosystem. This is the foundation of effective monitoring.
This includes:
- domains & subdomains
- social media handles
- mobile applications
- third-party platforms
Go beyond static discovery. Continuously update this inventory as your company expands, launches new services or enters new markets.
Monitor across multiple environments
Attackers do not operate in isolation, they operate across many environments at the same time. Good brand abuse monitoring will provide broad and continuous coverage across multiple environments:
- open web (phishing sites, spoofed domains, fake landing pages)
- social platforms (impersonation accounts, scam campaigns)
- deep web (leaked data, exposed assets)
- dark web forums (credentials, fraud kits, chatter)
Validate and analyse threats
Every alert does not represent a real threat. To reduce noise and focus on high-risk issues, security teams must verify if the asset is truly harmful or a false positive. They should also analyse attacker intent. They should correlate findings with internal data and estimate the scope and reach of the threat.
Prioritise high-risk exposures
Prioritisation makes sure that resources are properly used and the critical alerts are addressed first. Threats should be prioritised based on:
- potential customer impact (credential theft, financial fraud)
- financial and regulatory risk
- brand reputation damage and public visibility
A risk-based approach helps security teams allocate resources efficiently and avoid alert fatigue.
Execute response and takedowns
Detection without action creates exposure. A mature strategy includes clearly defined response playbooks and escalation paths. Organisations must take action to:
- remove phishing domains
- disable impersonation accounts
- block malicious applications
Speed is very important here. Faster response directly reduces potential damage.
Real-world impact of poor brand abuse monitoring
Organisations that lack effective brand abuse monitoring often face increased customer fraud incidents. This can lead to serious reputational damage as well as regulatory scrutiny. The outcome is ultimately the loss of customer trust in your brand. In many cases, these incidents could have been prevented with early detection. But delay in detection can lead to serious consequences.
How brand abuse monitoring improves security posture
When implemented correctly, brand abuse monitoring becomes an import4ant layer of external threat intelligence and risk management. It helps firms proactively detect and respond to threats targeting their brand and customers.
- Early detection of external threats: Identifies phishing domains, fake websites, impersonation attempts and malicious campaigns before they impact customers.
- Faster and more effective incident response: Helps with quicker investigation and takedown of threats. As a result, it reduces potential damage and response time.
- Improved visibility into attacker behaviour: Provides insights into tactics, techniques and patterns used by threat actors targeting your brand.
- Stronger protection of customer trust: Prevents fraud, scams and impersonation attempts that could reduce customer confidence and brand reputation.
It also helps security teams to shift from reactive to proactive defence.
Conclusion
Your brand is one of your most valuable assets. But unfortunately, in today’s digital age, it is also one of the most targeted.
Attackers exploit brand trust to launch phishing campaigns, impersonate organisations and defraud customers. Without effective brand abuse monitoring, these threats remain invisible until they cause real damage.
A structured monitoring strategy helps you protect your digital presence across multiple platforms.
If you need support to build a strong brand abuse monitoring program, we can help you out. At CyberNX, we combine intelligence, technology & human expertise to protect firms from fast-moving threats.
We also provide brand monitoring, contextual threat intelligence as well as coordinated takedown support that reduces exposure time and reputational damage. To know about our complete digital risk protection services, connect with our experts today.
Brand abuse monitoring FAQs
What is brand abuse monitoring?
Brand abuse monitoring is the process of detecting and responding to illegal use of a company’s brand across digital platforms like websites and social media.
Why is brand abuse monitoring important?
It helps organisations detect phishing attacks, impersonation, and fraud campaigns early, reducing customer impact and reputational damage.
What types of threats does brand abuse monitoring detect?
It detects phishing domains, fake social media accounts, malicious mobile apps, and credential leaks linked to brand misuse.
How often should brand abuse monitoring be performed?
Monitoring should be continuous because attackers operate across digital platforms at all times.
Who needs brand abuse monitoring?
Enterprises in banking, fintech, e-commerce, healthcare, and technology sectors benefit significantly due to high exposure to brand-based attacks.