Digital risks are growing every day. Threats outside the perimeter which can damage reputation, customer trust and revenue are rising exponentially. This is where best practices for digital risk protection become essential.
Digital risk protection helps organisations detect and respond to threats across the open web, deep web and dark web. It protects digital assets, brand identity and sensitive information. The right approach does not rely only on tools. It requires visibility, monitoring and a clear response strategy. Let us explore the best practices for digital risk protection that security leaders should prioritise.
What digital risk mean in modern organisations
Digital risk includes any external threat that affects an organisation’s online presence, data or brand reputation. Many of these risks exist beyond traditional security monitoring.
Common examples include:
- Brand impersonation through fake websites
- Phishing domains targeting customers
- Leaked credentials on dark web marketplaces
- Mobile app impersonation
- Data leaks from third party vendors
- Social media account compromise
These risks spread quickly across the internet. A fake domain can appear within hours. Stolen credentials may circulate for months before detection. Traditional security tools rarely monitor these areas. As a result, organisations need a dedicated strategy for digital risk protection.
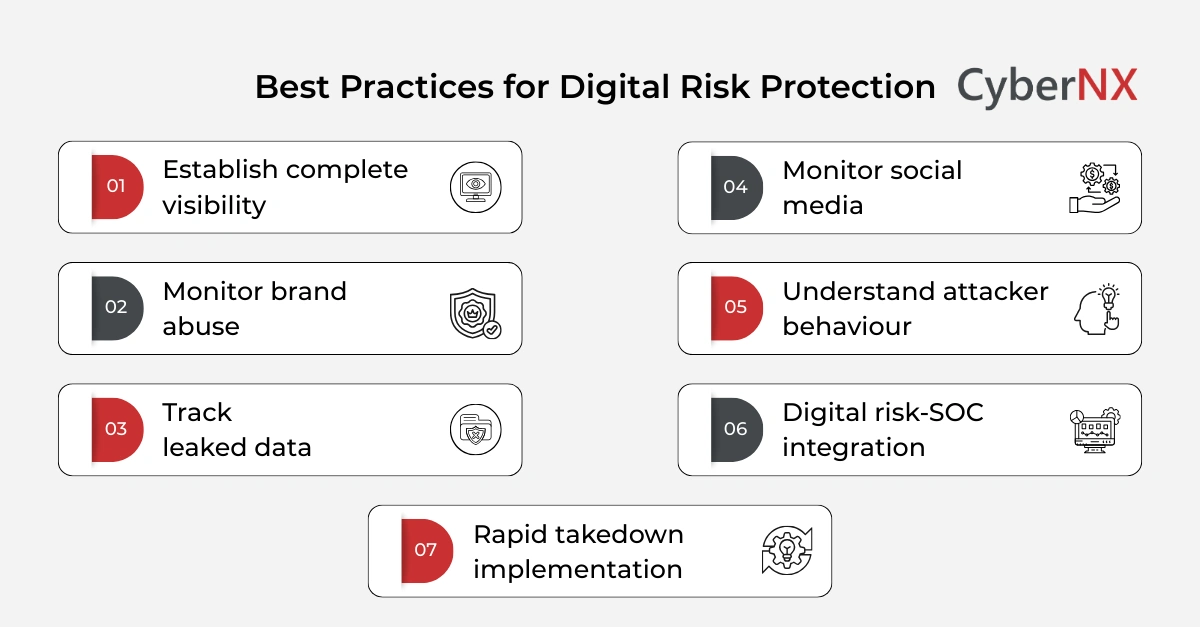
Best practices for digital risk protection
Adopting the best practices for digital risk protection requires a mix of monitoring, intelligence and proactive response. The following strategies help organisations manage digital threats more effectively.
1. Establish complete visibility of external assets/Establish complete visibility
Many organisations do not have a full inventory of their digital footprint. Unknown assets create security blind spots. Security teams should map and monitor all external digital assets. These include:
- Corporate domains and subdomains
- Mobile applications
- Social media accounts
- Third party platforms
- Cloud hosted services
- Public facing APIs
Continuous asset discovery helps identify unknown or shadow assets. Once visibility improves, monitoring becomes more effective.
2. Monitor domain abuse and brand impersonation/Monitor brand abuse
Threat actors frequently create fake domains that imitate legitimate brands. These domains often support phishing campaigns or online fraud.
Proactive monitoring can identify suspicious registrations early.
- Important monitoring areas include:
- Typosquatted domains
- Lookalike domains
- Newly registered domains using brand keywords
- Phishing websites targeting customers
Early detection allows security teams to take down malicious domains before damage spreads.
3. Track leaked credentials and sensitive data/Track leaked data
Credential leaks remain a common entry point for cyber-attacks. Attackers often sell or share stolen credentials in underground marketplaces. Monitoring dark web sources helps identify compromised accounts. Security teams should watch for:
- Employee credentials
- Customer account leaks
- API keys or tokens
- Database dumps
- Internal documents
Once detected, organisations can quickly reset passwords and investigate exposure. This reduces the risk of account takeover or unauthorised access.
4. Monitor social media for impersonation and scams/Monitor social media
Social media platforms have become a frequent target for impersonation. Fake accounts can mislead customers, spread misinformation or promote scams. Security teams should track brand mentions and suspicious accounts.
Monitoring should include:
- Fake company pages
- Fraudulent customer support accounts
- Scam promotions using the brand name
- Malicious links shared through impersonated profiles
Rapid reporting and removal of fake accounts protects both customers and brand reputation.
5. Use threat intelligence to understand attacker behaviour/Understand attacker behaviour
Threat intelligence provides valuable insight into how attackers operate. It helps security teams anticipate threats instead of reacting after an incident. Threat intelligence sources may include:
- Dark web intelligence
- Threat actor forums
- Malware campaigns targeting specific industries
- Credential trading marketplaces
Combining digital risk protection with threat intelligence improves early detection of emerging threats. Security teams gain context around attacker tactics and motivations.
6. Integrate digital risk protection with SOC operations/Digital risk-SOC integration
Digital risk protection should not operate in isolation. It must integrate with the broader security operations workflow. Alerts from external monitoring should feed directly into security operations centres. Integration helps teams:
- Investigate threats faster
- Correlate external intelligence with internal events
- Prioritise high risk alerts
- Respond quickly to emerging attacks
Automation also plays an important role. Automated alert triage reduces investigation time.
7. Implement rapid takedown processes/Rapid takedown implementation
Detection alone is not enough. Organisations must remove malicious assets quickly. Effective takedown processes include coordination with:
- Domain registrars
- Hosting providers
- Social media platforms
- App stores
- Law enforcement agencies
A well-defined takedown workflow significantly reduces exposure time. The faster malicious content disappears, the lower the impact on customers.
Conclusion
External cyber threats continue to grow. Attackers exploit brand reputation, leaked credentials and fake domains to target customers and employees. Traditional security tools rarely detect these threats early. Organisations need broader visibility across the digital ecosystem. Adopting the best practices allows security teams to detect threats earlier, protect brand reputation and reduce the risk of fraud.
The key lies in continuous monitoring, threat intelligence and rapid response.
We support organisations in building stronger external threat visibility. Our experts help identify digital risks, monitor emerging threats and respond quickly when incidents occur. Connect today to know about our digital risk protection services.
Best practices for digital risk protection FAQs
How can organisations measure the effectiveness of digital risk protection programmes?
Effectiveness can be measured through metrics such as the number of detected threats, takedown response time and reduction in brand impersonation incidents. Faster detection and remediation indicate stronger digital risk protection capabilities.
Which teams should be involved in digital risk protection initiatives?
Digital risk protection requires collaboration across security, legal, marketing and fraud teams. Each group helps detect threats, validate impersonation cases and coordinate rapid takedown actions.
Which industries face the highest digital risk exposure?
Industries with strong online presence face higher exposure. Financial services, ecommerce, healthcare and technology sectors often experience phishing campaigns, brand impersonation and credential leaks.
Can digital risk protection reduce phishing attacks targeting customers?
Yes. Continuous monitoring helps identify phishing domains, fake websites and impersonated social accounts early. Quick takedown actions reduce the chances of customers falling victim to scams.