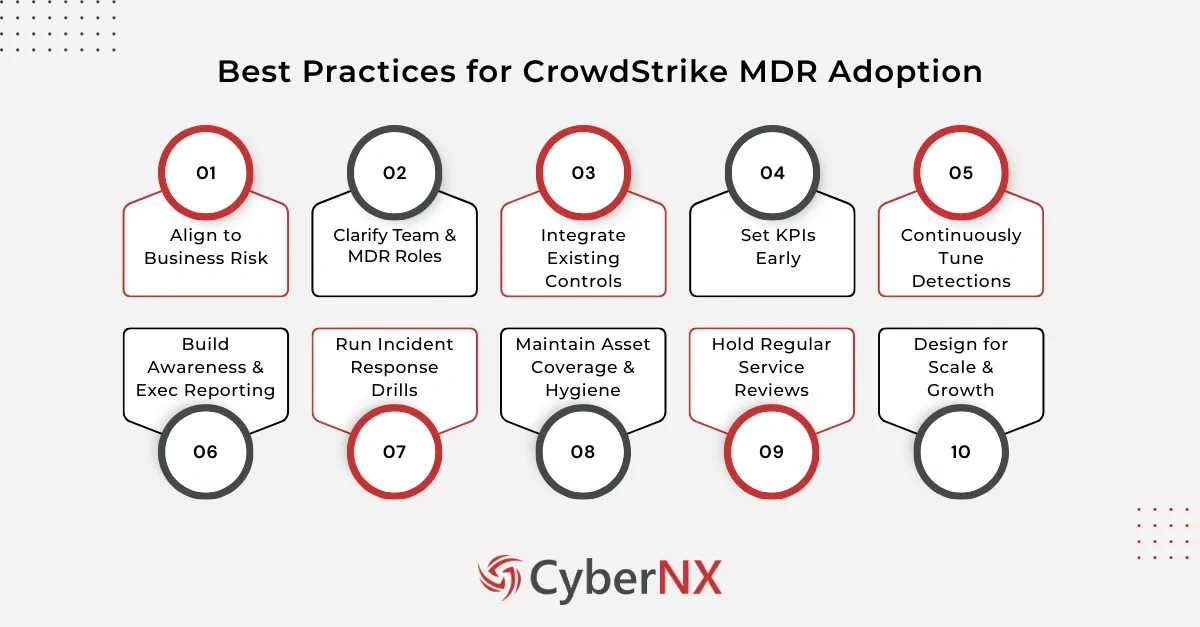
Modern enterprises are investing heavily in CrowdStrike managed detection and response. However, many struggle to extract full value out of the platform. Best practices for CrowdStrike MDR adoption often determine whether your security programme evolves or simply adds another tool to manage.
We have seen organisations deploy advanced MDR capabilities but fail to align them with business risk, internal processes, or response workflows. The result is alert fatigue, confusion over ownership, and underused intelligence. That’s why in this blog we break down practical best practices you should follow while adopting and implementing CrowdStrike MDR.
Why a structured approach to MDR adoption matters
Before diving into specific actions, it is important to understand why best practices need executive focus. MDR is not a tool like EDR or XDR. It is an operational model which blends technology, people, and processes. Without clarity on scope, ownership, and escalation paths, even the strongest MDR platform underperforms. A structured approach ensures faster detection, sharper response, and clear accountability.
Here, we discuss the best practices for CrowdStrike MDR, which will help you leverage its full potential and operational value.
1. Align with business risk priorities
The first of the best practices is strategic alignment. Security leaders should map MDR capabilities directly to business risks.
Start by asking:
- Which assets generate the highest revenue?
- Which systems hold regulated data?
- Which environments are most exposed to external threats?
Once identified, configure policies and detection priorities accordingly. For example, high value assets may require tighter detection thresholds and faster containment actions.
We often recommend holding a joint workshop with business stakeholders before finalising deployment scope. This avoids the common trap of treating all endpoints equally.
When MDR aligns with business context, every alert has meaning.
2. Define clear roles between your team & MDR provider
One of the most overlooked practices while adopting CrowdStrike MDR is clarity in shared responsibility. MDR is a partnership. Your provider monitors, investigates, and escalates. However, internal teams must decide:
- Who approves containment actions?
- Who handles post incident remediation?
- Who communicates with leadership?
Document these roles formally. Establish a RACI matrix if needed. Many organisations delay containment because approval paths are unclear. During an active threat, minutes matter. Pre-approved playbooks prevent hesitation.
We encourage clients to simulate at least one major incident during onboarding. This surfaces friction early and builds trust between teams.
3. Integrate with existing security controls
CrowdStrike MDR delivers powerful endpoint visibility. Yet its impact increases when integrated with other systems.
Effective best practice includes integration with:
- SIEM platforms for centralised logging
- Identity systems for user context
- SOAR tools for automated workflows
- Ticketing systems for response tracking
Integration creates a unified view. Analysts gain context beyond endpoint telemetry. Automated actions reduce manual workload.
For example, if MDR flags suspicious credential activity, automated integration with identity systems can disable accounts instantly. That containment step may prevent lateral movement. Security leaders should treat MDR as a core component of a broader ecosystem, not an isolated layer.
4. Establish measurable KPIs from day one
Adoption without metrics leads to vague outcomes. A strong practice is to include clear performance indicators.
Track metrics such as:
- Mean time to detect
- Mean time to respond
- Number of incidents auto contained
- False positive rates
- Coverage across endpoints and workloads
Regular reviews of these metrics help identify gaps. If response times are high, investigate process bottlenecks. If coverage is incomplete, prioritise onboarding remaining assets.
We recommend quarterly strategic reviews with stakeholders. These sessions shift the conversation from alerts to business impact.
5. Optimise detection policies over time
Threat landscapes evolve and your MDR configuration should evolve as well.
Another critical element is continuous tuning. Initial settings may be broad to establish visibility. Over time, refine them based on:
- Industry specific threats
- Internal risk trends
- Past incident learnings
- Regulatory requirements
For example, financial institutions may prioritise detection rules around credential abuse. Healthcare organisations may focus on ransomware precursors.
Avoid static configurations. Periodic tuning ensures relevance and reduces noise.
6. Invest in internal awareness & executive reporting
MDR adoption is not just technical. It requires organisational buy in.
Security leaders should translate MDR outcomes into board level language. Reports should highlight:
- Business risks mitigated
- Attack trends observed
- Cost avoidance through early containment
- Compliance improvements
Executives rarely need raw telemetry data. They need clarity on risk posture.
Strong executive reporting is among the most strategic best practices for CrowdStrike MDR adoption. It secures continued investment and reinforces security as a business enabler.
7. Conduct regular incident response exercises
Even with a managed service, internal readiness matters. Tabletop exercises and red team simulations test the coordination between your team and CrowdStrike MDR analysts. They validate:
- Escalation speed
- Communication clarity
- Decision making authority
- Recovery processes
These exercises also highlight technical gaps. Perhaps certain servers are not fully onboarded. Perhaps contact lists are outdated. Practise reduces panic during real incidents. It builds confidence in the partnership model. We suggest running at least two structured simulations annually.
8. Ensure full asset coverage & hygiene
Partial visibility creates blind spots. One of the simplest yet most powerful best practices is complete asset onboarding. Verify that:
- All endpoints are enrolled
- Remote workers are included
- Cloud workloads are monitored
- Legacy systems are assessed
Shadow IT often undermines MDR effectiveness. Regular asset discovery scans help close gaps. In addition, maintain agent health checks. Unhealthy or outdated agents reduce detection accuracy.
Comprehensive coverage ensures that attackers cannot exploit unmanaged devices as entry points.
9. Strengthen collaboration through regular service reviews
MDR is dynamic. Ongoing communication enhances performance. Schedule monthly operational calls to review:
- Notable incidents
- Detection improvements
- Emerging threat intelligence
- Planned infrastructure changes
Changes in your environment such as mergers, cloud migrations, or new business units should trigger MDR scope updates. Proactive communication prevents misalignment. Plus, it is a best practice to rely on transparency and shared learning.
10. Plan for scalability & future growth
As your organisation grows, so does attack surface. Consider how MDR will support:
- Cloud expansion
- Remote workforce growth
- Mergers and acquisitions
- New regulatory frameworks
Scalability should be part of the initial adoption roadmap. When planning strategically, these best practices become long term enablers of digital growth rather than reactive safeguards.
Conclusion
Best practices for CrowdStrike MDR adoption focus on alignment, integration, measurable outcomes, and continuous improvement. When executed thoughtfully, MDR becomes a force multiplier for your security operations.
At CyberNX, our experts work with security teams to design, optimise, and govern MDR programmes that align with business priorities. If you are planning or refining your MDR journey, let us help you turn advanced detection into tangible risk reduction.
Ready to maximise your CrowdStrike MDR investment? Speak with our experts for a tailored CrowdStrike Consultation.
Best practices for CrowdStrike MDR adoption FAQs
1. How long does it take to fully implement CrowdStrike MDR in an enterprise environment?
Implementation timelines vary by organisation size and asset complexity. Most mid-sized enterprises achieve baseline deployment within four to eight weeks. Optimisation continues over several months.
2. Can CrowdStrike MDR replace an internal SOC team?
It can augment or partially replace internal monitoring functions. However, many organisations retain internal teams for governance, strategic oversight, and remediation coordination.
3. What industries benefit most from CrowdStrike MDR adoption?
Highly regulated sectors such as finance, healthcare, and critical infrastructure benefit significantly due to constant threat exposure and compliance pressures.
4. How does CrowdStrike MDR support compliance requirements?
MDR supports compliance by improving detection, maintaining audit logs, and providing documented incident response processes. It strengthens evidence for regulatory reviews.